Article
Black Kingdom Returns to Exploit Zero-Day Vulnerabilities in Unpatched Microsoft Exchange Servers
Arete Analysis

Summary
Black Kingdom ransomware recently resurfaced to target a zero-day vulnerability in Microsoft Exchange servers.
Earlier this month, Microsoft released a statement notifying the public of a zero-day exploit that affected its on-premises Exchange Servers, versions 2013 through 2019. Within a week, Arete incident responders spoke to approximately 100 affected companies — small- and medium-sized companies that had no reason to be on the target list of the Microsoft-coined hacking group Hafnium.
The worst part about this zero-day announcement was that sometime around March 10, the threat group published the proof-of-concept (PoC) code to GitHub. The irony: Microsoft owns GitHub; GitHub hosted the PoC code.
Since that publication, the security community has been speculating on a second wave of attacks involving this exploit. A wave that would be worse than the first. A wave that would be linked to all sorts of corporate business interruptions from the likes of data exfiltration and ransomware.
How right was the speculation? Basically, the community #nailedit.
Second Wave of Ransomware Attacks Now Hitting
On March 12, DarkReading.com reported that a hacking group was deploying the ransomware variant, DEARCRY!, which was affecting unpatched Microsoft Exchange Servers.
Now, Arete has identified a second variant — Black Kingdom — that is also exploiting unpatched Microsoft Exchange Servers. The Black Kingdom variant made media headlines when it briefly surfaced and started to exploit the Pulse VPN zero-day in the early summer months of 2020. After, the group quietly disappeared … until this week.
How the Black Kingdom Ransomware Group Operates
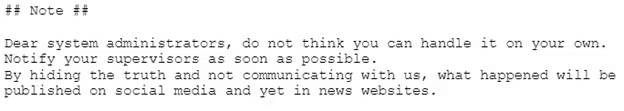
After the Black Kingdom group gains access to a network, they will perform some reconnaissance and start their encryption, leaving behind a fitting ransom note entitled decrypt_file.txt to announce their return.
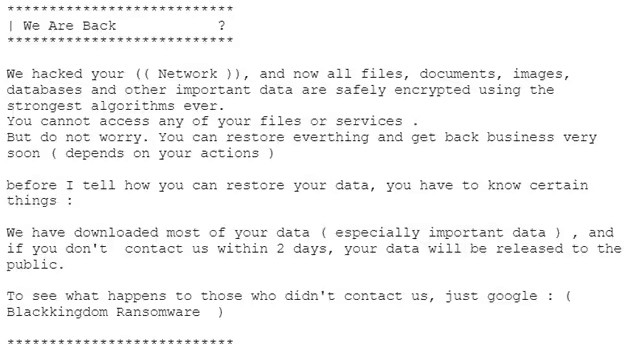
Black Kingdom’s ransom note is one of the longest notes left behind by ransomware groups. It provides explicit instructions on how to contact them, the ransom amount, the Bitcoin wallet ID, and a message stating that they exfiltrated data from the network. The note also states that refusal to pay would lead them to publish the attack and stolen files on social media.
Steps you can take to help prevent unauthorized access to your network
The Microsoft Exchange vulnerability is widespread and, if like many other previously reported vulnerabilities, may not get patched automatically or quickly enough to prevent ransomware groups and any other malicious actors from gaining unauthorized access to your network.
Follow these recommended steps protect your business and systems from unauthorized access:
1. Immediately patch the Exchange Server. If the system is not or cannot be patched, disable Outlook for Web Access (OWA). If you cannot disable OWA, remove the Exchange Server from the internet.
Prior to running the tool, create a backup of the Exchange Server in its current state.
Microsoft released a One-Click Mitigation tool to patch, upgrade, and scan for malicious activity. You can find the tool on the company’s Security Center blog.
Disable OWA according to the Microsoft guidelines. This may cause users to not have access to email.
If you cannot patch or disable OWA, remove the system from the internet by disconnecting the network cable or powering the system down. This action will cause significant disruption and prevent users from receiving emails in certain configurations.
2. The U.S. Cybersecurity & Infrastructure Security Agency (CISA) issued a mitigation alert. Please read the article.
Block IP addresses at the firewall.
Enable geofencing if your organization does not conduct business outside of the United States.
3. Change passwords for all Windows-based user accounts.
Start with the most privileged domain administrator and service accounts, then work towards the least privileged user accounts. Also include the local administrator password.
4. Preserve any firewall, web application firewall, or VPN logs.
5. Deploy an Enterprise Detection and Response (EDR) tool throughout the environment to detect any unauthorized activity.
If you suspect any unauthorized access to your Microsoft Exchange Server or network, contact us.
Back to Blog Posts
Article
Arete's 2026 Q1 Crimeware Report
Harness Arete’s unique data and expertise on extortion and ransomware to inform your response to the evolving threat landscape.
Article
CMS Vulnerability Leads to ClickFix Campaign
Threat actors compromised at least 700 education and technology websites in a recent ClickFix campaign by exploiting a critical SQL injection flaw (CVE-2026-26980) in the Ghost content management system (CMS). Adversaries combined the vulnerability with the ClickFix social engineering tactic to steal admin keys and inject a malicious JavaScript that delivers a fake Cloudflare or CAPTCHA verification pop-up, tricking victims into copying and pasting a malicious command into their systems.
What’s Notable and Unique
Rather than targeting the end user first, this campaign is unique in its initial exploitation of the system, followed by social engineering attempts. This hybrid attack style is likely being leveraged to bypass traditional defenses.
This recent campaign also highlights how trusted web properties can be weaponized at scale and coupled with unpatched CMS vulnerabilities. Rather than using the CMS compromise to perpetrate a single attack, threat actors turned it into a supply-chain attack that ultimately affected over 700 trusted websites.
Analyst Comments
As network defenders and their tools enhance threat detection capabilities, adversaries increasingly seek methods to bypass these defenses. By combining vulnerability exploitation, social engineering techniques, and staging for ancillary attacks, this campaign successfully bypassed traditional defenses and inflicted significant impact. Defending against hybrid cyberattacks requires comprehensive security controls beyond simply patching vulnerabilities. Organizations should focus on limiting movement within the environment, detecting abuse of trusted applications, and preventing end-user manipulation.
Sources
700+ education and tech websites hijacked in huge ClickFix malware campaign
Under the engineering hood: Why Malwarebytes chose WordPress as its CMS
Think before you Click(Fix): Analyzing the ClickFix social engineering technique
Ghost CMS Vulnerability Exploited to Infect 700 Sites With ClickFix Malware
Article
Threat Actors Leverage Fake JPEG Files for Initial Access
In a recent campaign, researchers observed threat actors using fake JPEG image files as a delivery mechanism to initiate the deployment of additional malicious components. The false JPEG files are typically distributed via phishing emails or other social engineering-based lures, and are actually PowerShell-based malware that deploys a trojanized version of ConnectWise ScreenConnect to establish and maintain persistence in the compromised environment.
What’s Notable and Unique
This campaign leverages JPEG images as the initial lure, where the images are not merely decoys but part of the infection workflow. Victims are typically led to download or open an image that triggers hidden execution logic or redirects them to a payload-delivery sequence that initiates later stages of the intrusion chain.
The attack chain is designed to blend into legitimate environments, making detection more difficult. Execution typically relies on scripted or native Windows components, often including PowerShell or other living-off-the-land binaries, enabling fileless or near-fileless execution and reducing forensic artifacts on disk.
The multistage design ensures that the initial JPEG does not directly contain the full payload but instead triggers retrieval or decryption steps that progressively assemble the final malicious components in memory.
Analyst Comments
This campaign illustrates how threat actors continue to blur the line between legitimate file handling and malicious execution chains, indicating potential overlap with remote management or administrative tooling. The use of JPEG-based staging combined with script-based execution reflects a broader evolution toward a stealth-first intrusion design, in which file formats serve as triggers rather than payload containers.
Sources
OPERATION SILENTCANVAS : JPEG BASED MULTISTAGE POWERSHELL INTRUSION
Podcast
Cyber Risk and Insurance for Law Firms
In this episode of Bytes of Insight, host Vinny Sakore is joined by Laura Zaroski, Managing Director of the Law Firms Group at Gallagher, as they discuss the evolution of cyber risk for law firms. Tune in for firsthand insights on how to select the right cyber policy, the incident response process, and the nuances of ransom payments and sensitive data.



