Article
Cybersecurity Trends: What We Saw in 2020, What We Expect to See in 2021
Cybersecurity Trends

Where change seems a constant, perhaps the biggest and most surprising cybersecurity issue of 2020 was a lack of change. But before we get to that, let’s look at some other key cybersecurity trends.
A continued rise in ransomware attacks
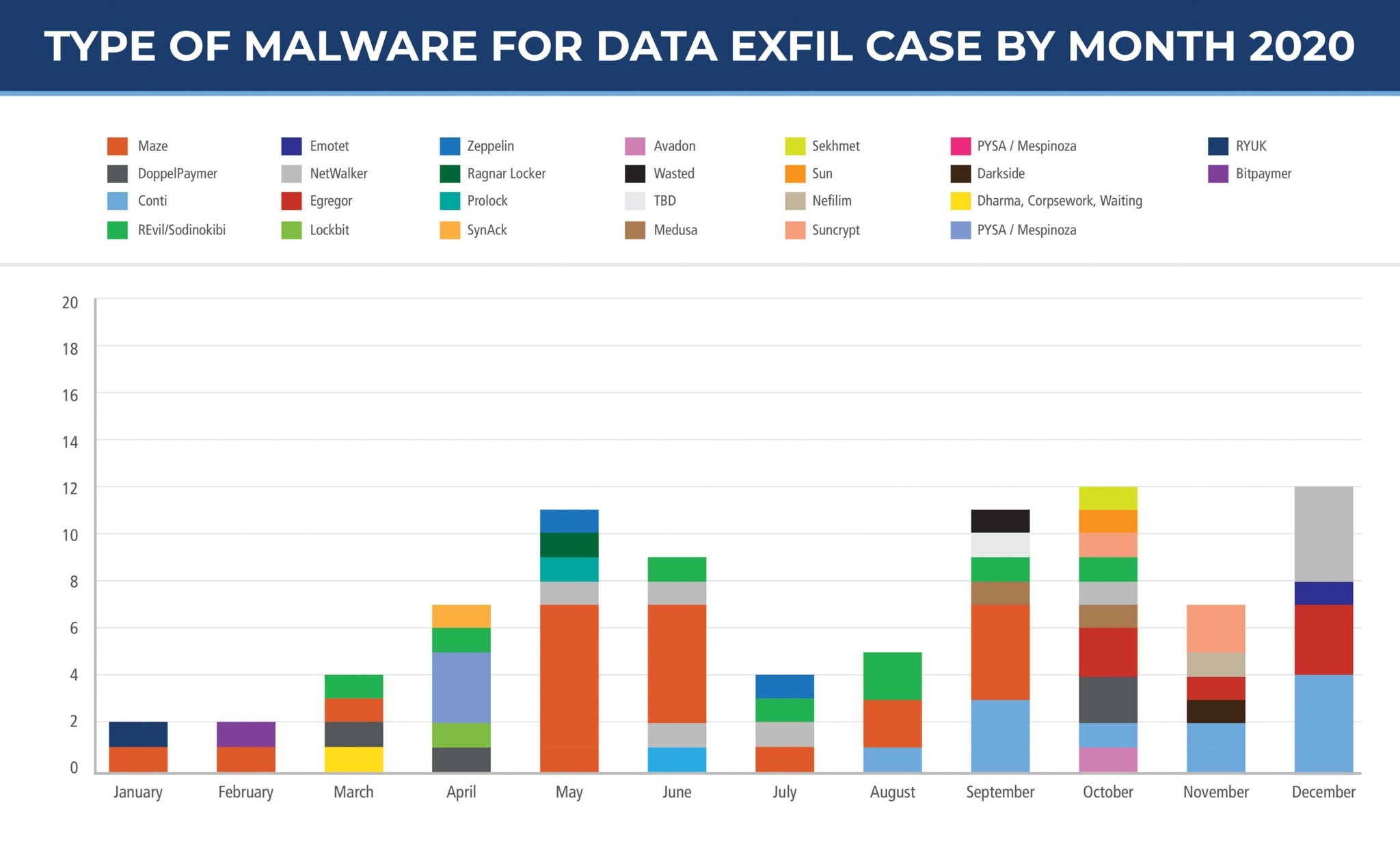
Kidnapping data and holding networks hostage remains a lucrative “business.” In the past year, the number of groups exfiltrating data for double extortion schemes has risen from two to 27.
With so many new entrants on the playing field, it may not come as much of a surprise that Arete saw the number of cases involving data exfil increase by a factor of six from Q4 2019 to Q4 2020.
As data exfiltration became a “common norm” by mid-2020, cyber burglars started to pay closer attention to the data they stole. It was a calculated move that often paid off.
After exfiltrating and encrypting a company’s data, they not only demanded ransoms for decryption, but also applied additional pressure for payments by threatening to sell or post the stolen information to leak sites, also referred to as “double-extortion.” Quite often, in either a blog post or during ransomware negotiations, they would provide specific files — which may have contained social security numbers, credit card information, or even, GDPR-regulated information on EU citizens — as “proof of exfiltration.”
While Maze successfully blazed the leak-site “shaming” trail back in 2019, multiple variants followed suit. By late summer 2020, the trend had evolved even further. Smaller variants were teaming with larger groups to reap the benefits of hosting files on established blog sites.
Big or small, all companies live or die by their reputation. If a single negative online review can get customers second-guessing, imagine the potential damage when a company needs to notify its customers of the theft and sale of their personally identifiable information (PII).
And sure, ransomware attacks on larger companies may get more press coverage, but it’s especially noteworthy that threat actors are increasingly targeting small- to medium-sized businesses (SMBs). According to ConnectWise’s “The State of SMB Cybersecurity in 2020” report, 55 percent of SMBs experienced a cyberattack in 2020. At Arete, we saw attacks on SMBs increase by a factor of three over the course of the year.
In 2021, there’s little doubt these numbers will continue to rise. We can expect threat actors to continue to focus on unpatched, under-secured SMB networks — especially as it’s no secret that the SMB market lacks the resources to pour into cybersecurity to protect the perimeter.
Often, these businesses don’t even have IT staff let alone the in-house security skills to defend against these types of threats. In short, they’re sitting ducks, hamstrung for many reasons, not least of which is an inability to make timely, informed decisions. Attackers know all of this, and they exploit weaknesses primarily for monetary gain.
Remote access compromises more than doubled
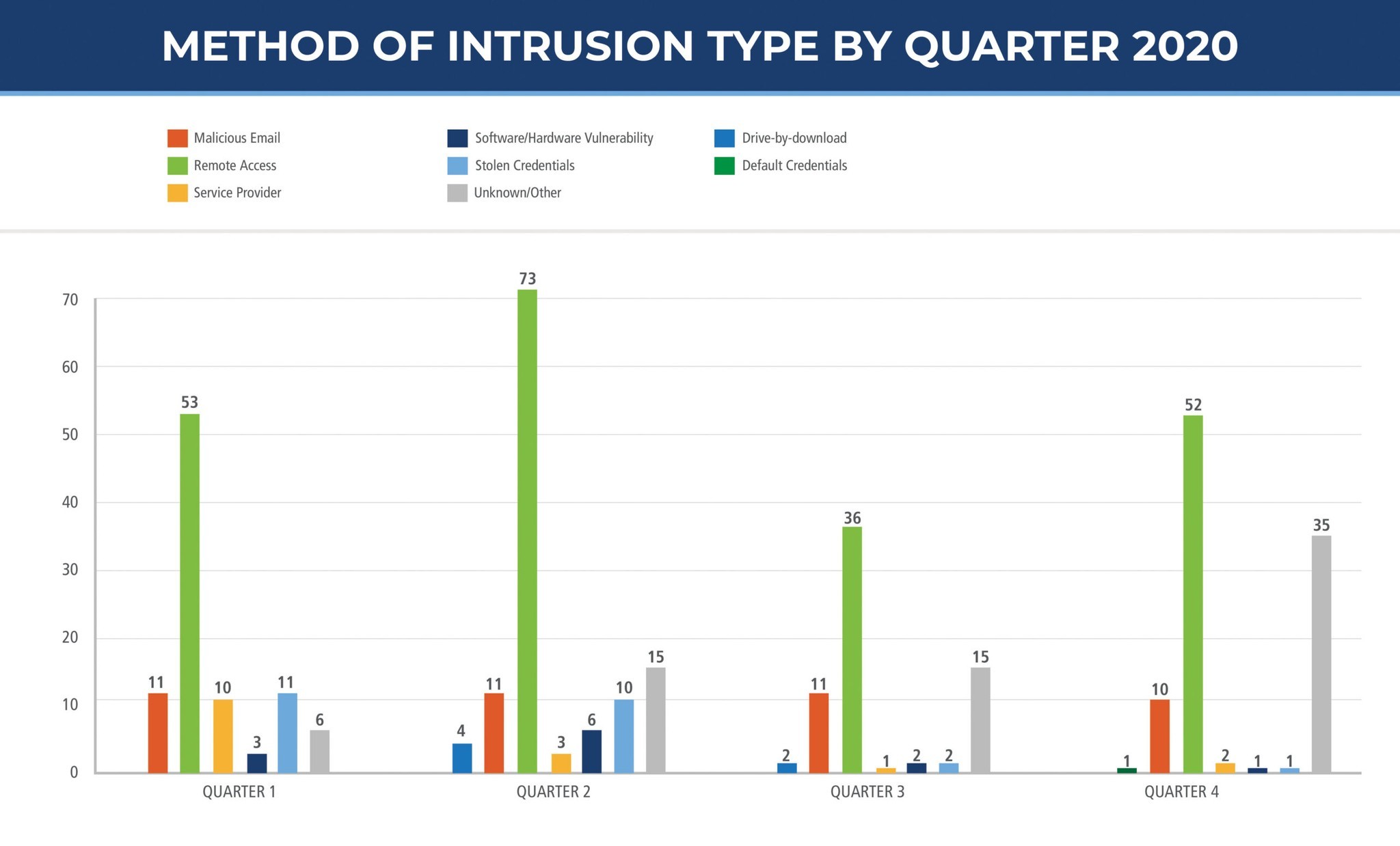
The COVID-19 pandemic certainly added its own twist to cybersecurity. With government mandates to shutter physical offices, many organizations had to adapt quickly to connect their workforce remotely. For some, this meant upgrading their VPN appliances. For others, it required implementing net-new remote access.
In both scenarios, the haste of implementation and upgrades created a metaphorical candy store for cybercriminals to ransack. Loads of misconfigurations, disabling of multifactor authentication (MFA) services, and phishing attacks added to the stress of an already chaotic time. For example, in the cases Arete worked last year, more than 90 percent of clients did not have MFA in place.
For SMBs, average ransom demands tripled, and payments doubled last year. In 2021, we expect more of the same. Ransomware groups will continue to increase attacks on the SMB market while also raising ransom demands and joining forces with other cybercrime groups to wreak maximum damage.
Threat actors stole and publicly released private red team tools
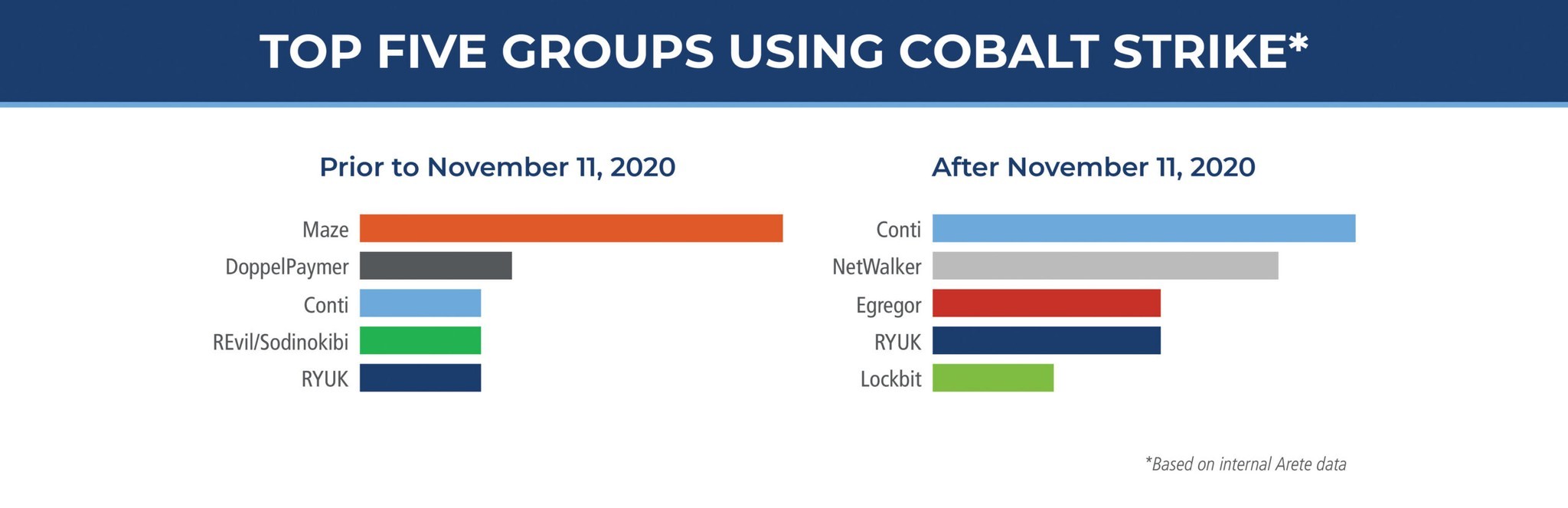
On November 11, 2020, Bleeping Computer published an article stating that someone had allegedly stolen and leaked the source code for the popular post-exploitation framework Cobalt Strike. The leak was identified from a GitHub account, which anyone could access and download.
Cobalt Strike itself is designed with optimum stealth. Essentially, when the program runs on an endpoint, it loads into the computer’s memory and “calls home” (aka beacons). When the command-and-control (C2) server establishes a connection, the attacker can perform any number of actions on the infected system without leaving much, if any, trace of activity.
Cobalt Strike’s stealth evades a large majority of AV products and even, some EDR solutions; and because forensic data is not captured when attackers use Cobalt Strike, it’s difficult to recreate their activity. Arete has observed attackers leveraging Cobalt Strike to move laterally within the environment, establish persistence, harvest credentials, and exfiltrate data.
An interesting observation and point of correlation: Since the source code was posted publicly, downloads from GitHub were anonymous. However, it’s also important to note that while many popular groups — such as Maze (no longer operating), Wasted Locker, Egregor, and Conti — leveraged Cobalt Strike prior to November 11, 2020, Lockbit emerged as the only group that did not leverage it prior to November 11. Given the publicity and strength of Cobalt Strike, we can expect to see wider adoption and use of the post-exploitation framework throughout 2021.
It’s common knowledge that many organizations purchase cyber insurance policies; and now, cyber thieves will explicitly look to target such organizations. On the off chance they find and steal cyber policies, they can use that information to set the ransom price accordingly — and they don’t care how new a policy is. If they obtain an older policy, they most likely know that the monetary coverage amount should still apply, which can then make ransom negotiations that much more difficult.
Most will state up front, “We know the coverage limit is $1 million and we won’t accept less than $900,000. You can use the remaining $100,000 for your legal fees.” The problem with these kinds of assumptions is that, nearly 100 percent of the time, they’re incorrect. Threat actors have minimal understanding of the insurance business and how to read policies. The reality is that there is very little money left to play with.
This trend will continue in 2021, with these groups increasing pressure on victim organizations by searching for sensitive information and cyber policies and contacting and harassing victims or clients of victims via phone or email.
A bigger issue for SMBs: overall cybersecurity
Though ransomware will continue to plague SMBs, these types of attacks are just a symptom of the market’s overall cybersecurity issues. Consequently, because so many SMBs lack security resources, it may be time for them to consider outsourcing. Managed detection and response (MDR) services can offer a cost-effective option that would allow them to re-focus on their core competencies while leaving defense to those with the requisite skills and experience.
At Arete, if we’ve heard it once, we’ve heard it a thousand times. Incident after incident, it’s the same story. A client calls about a breach and as soon as we hear what security products and configurations are in place, we know their next words before they can say them. The “script” goes something like this:
VICTIM
IT received a call that our sales team couldn’t access their email. When IT logged into the Exchange server, they found all the files with a random extension and a readme.txt ransom note.
ARETE
Do you have RDP enabled for external access? Essentially, if I were working from home, could I use RDP to connect to the network? Also, is the file extension different on every system? Does the readme note contain a reference to TOR browser?
VICTIM
Yes. Yes, to all.
ARETE
That’s most likely Sodinokibi ransomware. We will confirm it once we receive the ransom note.
To be frank, we haven’t seen any real change in most points of entry or password usage, not only in 2020, but since the 90s. It’s time to rewrite the script. Most SMB IT technology implementations date back to the early 2000s, and the market hasn’t seen the need to upgrade or enhance security since. RDP is one of the easiest remote access technologies to implement, yet the hardest to secure. Without SMBs putting an emphasis on security, “technologies from the 90s” will continue to be used — and exploited.
Too often, companies with thousands of endpoints will not have an endpoint detection and response (EDR) solution. They may have the latest security technologies in place, but ones that threat actors easily bypass. The toughest aspect of having a threat actor bypass a security product is explaining to clients that the relabeling of their antivirus (AV) product to an endpoint product was just marketing. An AV product isn’t tamperproof. And once attackers gain domain or local administrator privileges, they will disrupt the AV service, unloading virus definitions, disabling the service, whitelisting a folder where they plan to store their tools, and even, uninstalling the product.
By contrast, a true EDR tool will not hook into Active Directory and can’t be uninstalled, disabled, or unloaded by a domain administrator. Rather, only the central console can control the EDR tool. If you’re having doubts about that last statement, take a look at Gartner’s Peer Insights on EDR tools. The reviews may surprise you.
Cybersecurity requires more than technology
The right technology is crucial and can give you a leg up, but it doesn’t replace the experience, talent, and know-how to implement that technology. Again, service delivery will become increasingly important in 2021. In this regard, companies need to: 1) establish and follow the proper protocols in response to attacks; and 2) never cease to innovate and become more relentless in leveraging early warning systems, utilizing threat intelligence, and integrating automation.
A consistent commonality across SMBs is that, while they have successful businesses, they lack documented policy specifically around disaster recovery, responding to computer security events, and general security-leading practices. Managed service providers can work with SMBs to build and enhance security-focused programs to mitigate threats against their organizations. They can apply knowledge they’ve gained from the large Fortune 500 company engagements into a practical format that is easily integrated into SMB business operations.
What’s more, managed services providers should work with their industry partners, current clients, and former clients to “pulse check” the security landscape to identify common challenges — like the need for faster access to intelligence and faster identification and remediation of threats. They should also be able to integrate open-source intelligence with security know-how to deliver actionable information. For example, when mass access or major vulnerabilities are posted to hacker forums, it’s critical to work with partners to respond, threat hunt, and secure client networks before threat actors can exploit access.
Stronger government focus on cyberattacks
Between the COVID-19 pandemic, ransomware groups’ change of tactics, techniques, and procedures (TTPs), and their increased awareness of stolen data, 2020 was a year ripe with challenges.
In 2021, while we’re likely to see more new challenges, we can also expect to see a stronger government focus on cyberattacks, specifically ransomware. We will also see greater government engagement with municipalities, school districts, and healthcare organizations to prevent cyberattacks on these critical services.
Just as Arete IR is trying to stop cyberattacks from occurring, the Cybersecurity and Infrastructure Security Agency (CISA) recently rolled out a new campaign to help grow awareness and fight the increasing ransomware threat. CISA’s intention is to reduce or outright prevent ransomware attacks by equipping organizations with the necessary knowledge and expertise to detect cyberattacks earlier.
In short, a glimmer of hope for better days ahead.
Back to Blog Posts
Article
Arete's 2026 Q1 Crimeware Report
Harness Arete’s unique data and expertise on extortion and ransomware to inform your response to the evolving threat landscape.
Article
CMS Vulnerability Leads to ClickFix Campaign
Threat actors compromised at least 700 education and technology websites in a recent ClickFix campaign by exploiting a critical SQL injection flaw (CVE-2026-26980) in the Ghost content management system (CMS). Adversaries combined the vulnerability with the ClickFix social engineering tactic to steal admin keys and inject a malicious JavaScript that delivers a fake Cloudflare or CAPTCHA verification pop-up, tricking victims into copying and pasting a malicious command into their systems.
What’s Notable and Unique
Rather than targeting the end user first, this campaign is unique in its initial exploitation of the system, followed by social engineering attempts. This hybrid attack style is likely being leveraged to bypass traditional defenses.
This recent campaign also highlights how trusted web properties can be weaponized at scale and coupled with unpatched CMS vulnerabilities. Rather than using the CMS compromise to perpetrate a single attack, threat actors turned it into a supply-chain attack that ultimately affected over 700 trusted websites.
Analyst Comments
As network defenders and their tools enhance threat detection capabilities, adversaries increasingly seek methods to bypass these defenses. By combining vulnerability exploitation, social engineering techniques, and staging for ancillary attacks, this campaign successfully bypassed traditional defenses and inflicted significant impact. Defending against hybrid cyberattacks requires comprehensive security controls beyond simply patching vulnerabilities. Organizations should focus on limiting movement within the environment, detecting abuse of trusted applications, and preventing end-user manipulation.
Sources
700+ education and tech websites hijacked in huge ClickFix malware campaign
Under the engineering hood: Why Malwarebytes chose WordPress as its CMS
Think before you Click(Fix): Analyzing the ClickFix social engineering technique
Ghost CMS Vulnerability Exploited to Infect 700 Sites With ClickFix Malware
Article
Threat Actors Leverage Fake JPEG Files for Initial Access
In a recent campaign, researchers observed threat actors using fake JPEG image files as a delivery mechanism to initiate the deployment of additional malicious components. The false JPEG files are typically distributed via phishing emails or other social engineering-based lures, and are actually PowerShell-based malware that deploys a trojanized version of ConnectWise ScreenConnect to establish and maintain persistence in the compromised environment.
What’s Notable and Unique
This campaign leverages JPEG images as the initial lure, where the images are not merely decoys but part of the infection workflow. Victims are typically led to download or open an image that triggers hidden execution logic or redirects them to a payload-delivery sequence that initiates later stages of the intrusion chain.
The attack chain is designed to blend into legitimate environments, making detection more difficult. Execution typically relies on scripted or native Windows components, often including PowerShell or other living-off-the-land binaries, enabling fileless or near-fileless execution and reducing forensic artifacts on disk.
The multistage design ensures that the initial JPEG does not directly contain the full payload but instead triggers retrieval or decryption steps that progressively assemble the final malicious components in memory.
Analyst Comments
This campaign illustrates how threat actors continue to blur the line between legitimate file handling and malicious execution chains, indicating potential overlap with remote management or administrative tooling. The use of JPEG-based staging combined with script-based execution reflects a broader evolution toward a stealth-first intrusion design, in which file formats serve as triggers rather than payload containers.
Sources
OPERATION SILENTCANVAS : JPEG BASED MULTISTAGE POWERSHELL INTRUSION
Podcast
Cyber Risk and Insurance for Law Firms
In this episode of Bytes of Insight, host Vinny Sakore is joined by Laura Zaroski, Managing Director of the Law Firms Group at Gallagher, as they discuss the evolution of cyber risk for law firms. Tune in for firsthand insights on how to select the right cyber policy, the incident response process, and the nuances of ransom payments and sensitive data.



