Article
Egregor: The Ghost of Soviet Bears Past Haunts On
Arete Analysis
Combating Ransomware
Threat Actors

Summary
Egregor ransomware, a sophisticated RaaS platform, uses data exfiltration and brazen negotiation tactics to target major sectors like manufacturing and retail and caters to experienced affiliates.
Ransomware variants come. Ransomware variants go. And while Egregor may have only recently surfaced, it is by no means a fly-by-night operation. In fact, one could argue that the foundation upon which Egregor operates has been around since Stalin and Beria’s secret police, and it is been lurking, watching, waiting for the right time to strike.
As a mature and exclusive Ransomware-as-a-Service (RaaS) platform, Egregor poses a serious threat to both public and private organizations. Not only is it supported by seasoned cybercriminal software developers, but it also caters to experienced affiliates who effectively target and compromise organizations, executing enterprise-wide deployment to maximize the monetization of their efforts.
In particular, Egregor plagues the manufacturing and retail sectors, with recent targets including well-known brands like Kmart, TransLink, Embraer, Randstad, Barnes & Noble, and Ubisoft. While the ransomware impacted more than 100 organizations across France, Italy, Germany, the U.K., Asia-Pacific, the Middle East, and Latin America in the final quarter of 2020, U.S. organizations remained top targets, accounting for roughly 50 percent of attacks in that timeframe.
Given the observed consistency of broad, opportunistic targeting, an attack is more a matter of when for organizations that remain unprepared.
Statistical data on Egregor ransomware from Arete metrics
The information listed below is based on Egregor cases investigated by Arete IR since October 2020. Our IR and Data Analytics practices work together to track key data points for every ransomware engagement. Our IR practice tracks data points on the ransomware variant and collects statistics based on handled engagements:
Sectors of clients affected by this threat:
Healthcare | Finance | Professional Services | Manufacturing | Public Service
Malware precursor: Qbot and IcedID
Average ransom demand: $3,407,119
Highest ransom paid: $1,000,000
Lowest ransom paid: $100,000
Average business downtime: 12 days
Data exfiltration has been observed in 99 percent of the cases. In one outlier case, where there was no data exfiltration, Arete assisted the client with data restoration.
From whence the brazen Egregor came
Egregor is a label inspired by the occult, signifying the collective “energy” or “force” of a group of individuals — perhaps befitting an affiliate-serving RaaS platform. It was first publicly identified as early as September 2020, closely following the alleged cessation of Maze ransomware operations the month prior. Both ransomware platforms evolved from the Sehkmet ransomware family, and code analysis of each has provided high-confidence indications that Egregor ransomware is most likely a successor to Maze, whose developers and operators have not ceased operations but merely “re-branded.”
Egregor developers and operator affiliates are likely Russian and/or Eastern European cybercriminals. Security researchers have noted observations of deployment script comments in Russian, and Egregor performs language checks in similar sequence and fashion to its predecessor Maze; it will not execute on systems with a regional designator for Russia or Commonwealth of Independent States (CIS) signatories.
The affiliates operating Egregor are also infamous for their brazen intimidation — for example, allegedly printing ransom demands from victim network printers — and hardline negotiating, executing on the ultimatum that they will leak victim data within 72 hours if they do not receive a response following the encryption of victims’ systems. In many cases, they will leak the entirety of the data they exfiltrate.
Egregor high-level technical overview
While tactics, techniques, and procedures (TTPs) may vary amongst operators, it’s important to note that Egregor caters to semi-exclusive affiliates, likely of Russian or Eastern European origin.
The broader research community has observed consistent commonalities between Egregor and ProLock intrusion cycles. Given their similarities in TTPs, supported by multiple open-source confirmations of our own observations, we assess with high confidence that Qakbot operators have likely transitioned from ProLock to Egregor.
Egregor operators are known to exploit vulnerable and internet-accessible RDP gateways and phish victims with targeted, convincing lures. They also commonly deploy Egregor through Qakbot (Qbot), Ursnif (Gozi/ISFB), IcedID (Bakbot) infostealer/loader hybrid Trojan malware. Cobalt Strike has also been used to deliver Egregor in select instances.
The Egregor payload was likely designed to be portable, serving various affiliate tools, and is commonly encountered as a PE in dynamic linked library (DLL) form. Open-source Intelligence (OSINT) indicates that the DLL contains code and data, natively supporting multiple bot loader functions. The payload will not be decrypted and loaded without the proper key phrase provided to the DLL in the command line.
Egregor operators perform several evasive maneuvers during to the intrusion cycle, including disabling antivirus and endpoint protection (e.g., Windows Defender) via automated scripts (e.g., PowerShell+WMI) executed under elevated privileges.
OSINT reporting reveals that operators have uploaded batch files to victim system that, when executed, will take advantage of the BITSAdmin (bitsadmin.exe) utility to download the ransomware from a remote server and automatically execute it in the system.
The malware supports the following command-line arguments:
–fast: targets files within a size-limit range for encryption
–full: full encryption of the host (including mapped/mounted network drives)
–multiproc: multi-threading for speed
–nomimikatz: switch off Mimikatz module; Mimikatz is an open-source OST credential-harvesting tool
–nonet: do not encrypt network drives
–path: encrypt only specified folder(s)
–target: encrypt file(s) that have a specific extension
–append: select file extension to append to encrypted files
–norename: do not rename encrypted files
–greetings: prepend a name to the ransom note, likely used for directly addressing victims
–samba: establish file-, printer-, and serial port-sharing between compromised nodes
–killrdp: terminate RDP session
During breach response investigations, Arete has observed the following artifacts associated with the ransomware execution:
exe C:%USERNAME%Downloadsclang.dll,DllRegisterServer -pigbutt5 –multiproc
exe \Domain_ControllerIntelmsvc.dll,DllRegisterServer -passegr17 –multiproc
exe C:Windowsmsvc.dll,DllRegisterServer -passegr13 –full
exe C:Windowsdog.dll,DllRegisterServer -pclassified13 –full
exe \Domain_Controllerintelfasm.dll,DllRegisterServer -pbiden17 –multiproc
C:Windowssystem32cmd.exe /c eb2.bat -passegr13
C:Windowssystem32cmd.exe /c eb.bat -pclassified13
The last two artifacts show the threat actor using a batch file to pass the key phrase and properly execute the ransomware with the “–full” option.
The following tools have also been found to be associated with the threat actor activity:
Advanced Port Scanner: A network scanner that enumerates networked hosts and open ports.
ADFind: A tool that is used to enumerate Active Directory.
Lazange: A password recovery tool to harvest credentials.
PsExec: A lightweight tool that lets you execute processes on other systems, complete with full interactivity for console applications, without having to manually install client software.
Security recommendations
Implement a sophisticated endpoint detection and response (EDR) solution that will rely on behavior analysis, instead of just malware signatures, and have tamper-proof capabilities.
Implement multi-factor authentication (MFA).
Implement an email security solution to detect and protect against known and unknown threats.
Lock down and tighten privileges around Microsoft PowerShell in your environment. Apply and enforce PowerShell Constrained Language Mode (CLM) throughout your environments. Consider Just Enough Administration (JEA) policies to allow select PowerShell host administrative capabilities while disabling others.
Hunt for unusual RDP connections.
Prevent users from executing any program or any of the 31 currently known Windows executable filetypes (e.g., .exe, .dll, .hta, .bat, .scr) from the AppDataLocalTemp path of Office365, Microsoft Word, Excel, and Outlook. Alternatively, also inspect C: C:Users[current user]AppDataRoamingMicrosoft as it’s another popular method that achieves the same results.
Develop and implement a user security education program to assist with identifying threats like those in phishing emails.
Implement an off-site backup solution and test it regularly.
Summary of indicators from OSINT and Arete investigations
Egregor filenames
clang.dll | fasm.dll | sed.dll | q.dll |
dog.dll | msvc.dll | b.dll |
Key phrases to decrypt and execute the ransomware
-passgregor10 | -passgregor1313 | -pass2police | -peguard6 | -pclassified13 |
-passengr13 | -passgregor9999 | -pbiden17 | -passengr17 | -websitecounterficker |
Note: ‘dubisteinmutterficker’ is a German profanity: You’re a motherf*****
Bitcoin [BTC] wallet addresses
1MPdDiRhWFawgN2GVi1Jamm8DdC4qypoGL | 112yZpAs3Va6az6JTKZ7iQZEAWdvD5DYoj |
1Mk96FcixjayGZgdPgo4GrnPPSn7rL1jpE | 1D2ZiHwE4pQb8X6NncXdfHwncHa3yrDdYr |
13ELQVGgkM79nW34ncBe7Jz7xhXsXmrRuM | 1PDSGRqkBF7yEjHTNDaxNm6UQT63rrzTGk |
1LdrbQEaersWLi6A83JrCzERyXEZWD4hBP | 1GJ4dp5wwK2E9P74eF7FVujjTHERDTFJX |
1GZV41rSAHAj63pNjLCBwo7rfioxU8JPE9 |
URLs hosting Egregor
hxxp://185.238.0[.]241:81/78.bin | hxxp://49.12.104[.]241:81/sm.dll |
hxxp://49.12.104[.]241/sm.dll | hxxp://49.12.104[.]241:81/78.bin |
Egregor SHA256 hashes
5cb7a352535b447609849e20aec18c84d8b58e377d9c6365eafb45cdb7ef949b 14e547bebaa738b8605ba4182c4379317d121e268f846c0ed3da171375e65fe4 4139c96d16875d1c3d12c27086775437b26d3c0ebdcdc258fb012d23b9ef8345 38b155b6546db882189cc79bcac0b0284d3f858e0feb1e5dbc24b22f78cdfb68 f1ba626b8181bd1cd84f47f70838d9fa4d8117fac3bd07cbd73cb6f73b1297f8 b9b71eb04d255b21e3272eef5f4c15d1c208183748dfad3569efd455d87879c6 6dbe1d2de299359036520f15490834a6ac40b665cf5cd249379d65242af00b44 3b13b6f1d7cd14dc4a097a12e2e505c0a4cff495262261e2bfc991df238b9b04 28f3f5a3ea270d9b896fe38b9df79a6ca430f5edab0423b3d834cf8d586f13e6 7222c8acc69a7598989c335d528b366f801a41b434cbf928c6aef01f8e54f57a a9d483c0f021b72a94324562068d8164f8cce0aa8f779faea304669390775436 14da004cc96b910fb75abb86df09e318d92f4fb8dda39c8bd6a8e0601b6605d8 004a2dc3ec7b98fa7fe6ae9c23a8b051ec30bcfcd2bc387c440c07ff5180fe9a 311baa4d4229a8d6802d82a8d9935592bf9a7b6aaf0949f0fa0b094592f5e8a7 ee06c557f1acd5c4948b1df0413e49f3885f8ac96185a9d986b91a1231444541 2d563dd113a02fdf452544ae2fd7c94162be6db8fb7a287a3474a6ab998159fd 2d01c32d51e4bbb986255e402da4624a61b8ae960532fbb7bb0d3b0080cb9946 9017c070ad6ac9ac52e361286b3ff24a315f721f488b53b7aaf6ac35de477f44 af538ab1b8bdfbf5b7f1548d72c0d042eb14d0011d796cab266f0671720abb4d aee131ba1bfc4b6fa1961a7336e43d667086ebd2c7ff81029e14b2bf47d9f3a7 e6b9d0d356223ed81e635c5702dd47bca1aaeae3471827db03470713e453d5b4 3fc382ae51ceca3ad6ef5880cdd2d89ef508f368911d3cd41c71a54453004c55 319ec80eae65c1d39df27c80b52fe7fe1fadc6e9ceabf72f57d1b29e0467ac02 932778732711cd18d5c4aabc507a65180bf1d4bd2b7d2d4e5506be4b8193596e 3e5a6834cf6192a987ca9b0b4c8cb9202660e399ebe387af8c7407b12ae2da63 3fd510a3b2e0b0802d57cd5b1cac1e61797d50a08b87d9b5243becd9e2f7073f 765327e1dc0888c69c92203d90037c5154db9787f54d3fc8f1097830be8c76ab b027467332243c8186e59f68ff7c43c9e212d9e5074fedf003febcfedad4381a 4c9e3ffda0e663217638e6192a093bbc23cd9ebfbdf6d2fc683f331beaee0321 42ac07c5175d88d6528cfe3dceacd01834323f10c4af98b1a190d5af7a7bb1cb e53ab9a892321f651b73c8468db43b1d82c8c9d7fb8d0131199f501c6a0bafa7 1399e4b4ec1c7f3e38048d526f85472c466421dcd00ecd4515605af191ac61ee 6675c204844476dd8ce59ead0eac082754ded599036551526a8e2c509a1407e4 605c2047be7c4a17823ad1fa5c1f94fd105721fce3621dc9148cd3baf352938e 7fe8d3e63bad6a1628376643a4fe43b9858af5426da808576900b7753bce7614 34c84f171cd6c627d116f9c571b35e11541d68abfce36c852d2d787149f44672 7caed5f406445c788543f55af6d98a8bc4f0c104e6a51e2564dd37b6a485cc18 6a441734b34cdee31a01164140b0c88966fbb4358dcb63a14ae6824f09e9476f 81afd15e8c4d3ae0e34ede646551fe2ed6872d2142f642835cbbbf7dc524131b df5d9251afabd579f85de2f4d0c90150693fa73631317a39d08749d366bf37fd 9c900078cc6061fb7ba038ee5c065a45112665f214361d433fc3906bf288e0eb 967422de1acc14deb7e7ce803d86aff44e2652bfcd550e3a34c2e37abc883dee a7940b9e8ad2a54368999366fe2c50f429008dfb0817000693077e1d1f107d6e c1c4e677b36a2ee6ae858546e727e73cc38c95c9024c724f939178b3c03de906 a5989c480ec6506247325652a1f3cb415934675de3877270ae0f65edd9b14d13 a376fd507afe8a1b5d377d18436e5701702109ac9d3e7026d19b65a7d313b332
Back to Blog Posts
Article
Critical MOVEit Automation Vulnerabilities Disclosed
A security advisory released by Progress Software details critical and high-severity vulnerabilities affecting their MOVEit Automation managed file transfer (MFT) solution. The vulnerabilities, tracked as CVE-2026-4670 and CVE-2026-5174, could allow a threat actor to bypass authentication and escalate privileges, leading to unauthorized access, administrative control, and data exposure. Cybercriminals have leveraged several MFT tools in previous campaigns, including the Accellion File Transfer Application (FTA), Fortra GoAnywhere MFT, and Cleo MFT. Flaws in MFT software are highly targeted by cybercriminals due to the volume and sensitivity of the data they control.
What’s Notable and Unique
MOVEit Transfer was heavily exploited by the Cl0p ransomware group in the summer of 2023. While the window of exploit activity lasted only a few weeks, victim extortion and data leaks continued throughout the remainder of the year, leading to more than 70 class-action lawsuits filed in the U.S.
There is no workaround or hotfix for these vulnerabilities. To fully patch the flaws, MOVEit administrators need to perform a "full install" of the latest version, which will require taking the system offline.
Security researchers have discovered ~1,400 MOVEit Automation instances exposed to the internet, with dozens belonging to U.S. local and state government agencies.
Analyst Comments
While the vulnerabilities patched in Progress Software's recent release differ from the SQL injection vulnerability exploited by the Cl0p ransomware group in 2023, exploitation of CVE-2026-4670 and CVE-2026-5174 could lead to equally impactful outcomes. Beyond the immediate impacts on affected organizations, trusted data-exchange platforms provide threat actors with an avenue to obtain sensitive information and infect partner and supplier environments. Furthermore, Arete has seen the time window between disclosure and weaponization of critical vulnerabilities continue to shrink, especially as threat actors increasingly adopt AI-enabled tooling. As such, organizations should not only implement the patches released by Progress Software, but also hunt for typical post-compromise behavior like enumeration of the underlying database, the creation of new user accounts or users operating with unexpected administrator privileges, and the presence of unauthorized remote monitoring and management (RMM) tools.
Sources
MOVEit Automation Critical Security Alert Bulletin – April 2026 – (CVE-2026-4670, CVE-2026-5174)
From Breach to Courtroom: Inside the MOVEit Exploitation and Mass Litigation
Progress warns of critical MOVEit Automation auth bypass flaw
Article
Ransomware Trends & Data Insights: April 2026
The threat landscape has remained relatively predictable thus far in 2026. In April, Qilin dethroned Akira as the most active threat group for the month. Akira, who had been the top ransomware threat each month since July 2025, was still only slightly behind Qilin and had roughly the same activity level as in March. INC Ransom and DragonForce also remained active threats in April, with those four ransomware groups accounting for half of all ransomware and extortion activity observed by Arete.
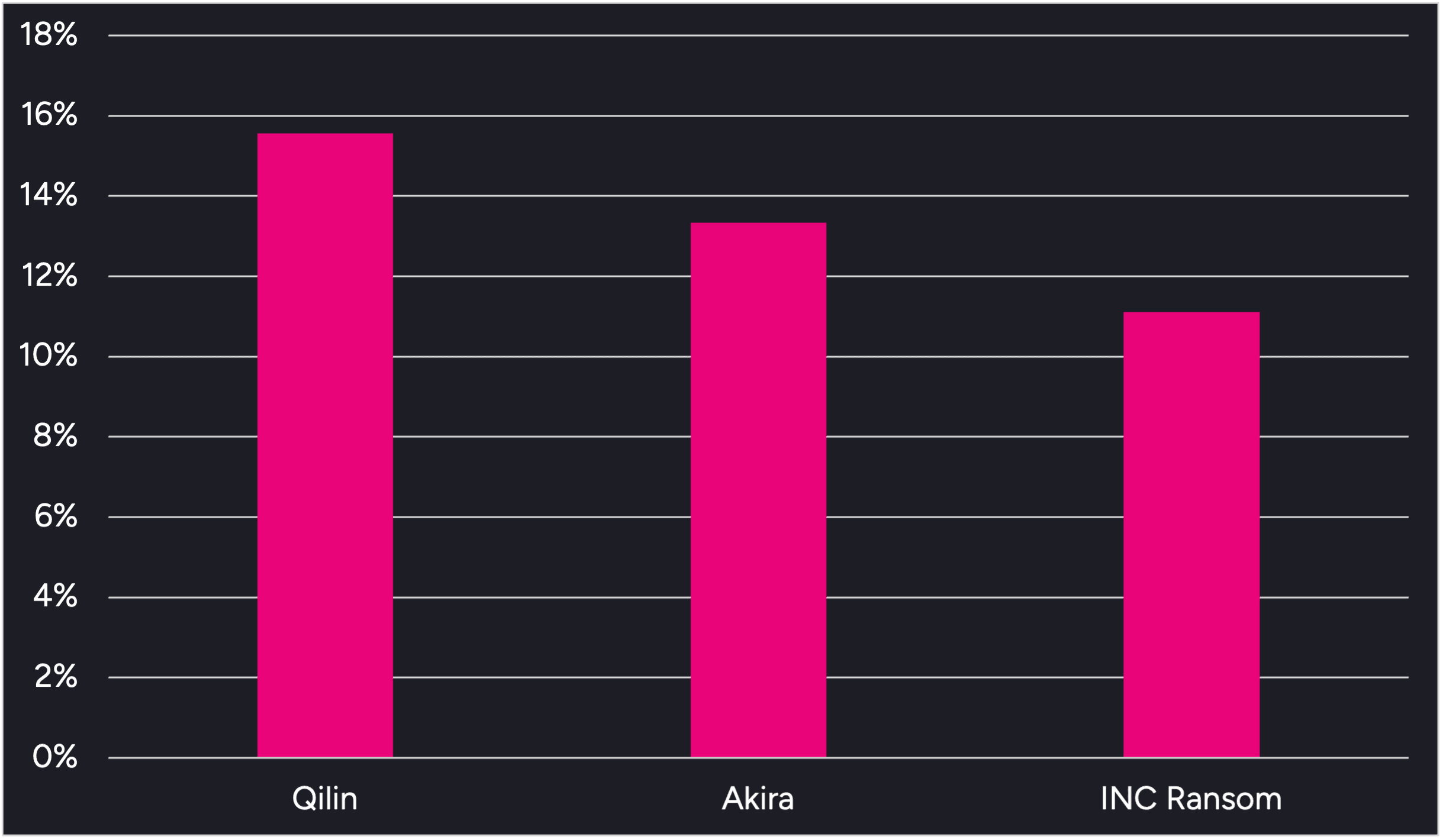
Figure 1. Activity from the top 3 threat groups in April 2026
Throughout the month, analysts at Arete identified several trends behind the threat actors perpetrating cybercrime activities:
Multiple ransomware operations continue to leverage the Bring Your Own Vulnerable Driver (BYOVD) technique to disable endpoint security controls prior to ransomware deployment. Qilin has recently been observed leveraging a malicious file loaded via DLL side-loading along with vulnerable drivers, including rwdrv.sys and hlpdrv.sys, to gain kernel-level access and disable security processes. Arete observed Akira using the same vulnerable drivers in multiple engagements dating back to Q3 2025.
DragonForce has leveraged several of the same tools in recent engagements, including the remote desktop application Remotely Agent and the PoisonX.sys vulnerable driver. Additionally, open-source reporting indicates that the group recently used a Python-based backdoor known as VIPERTUNNEL to maintain reliable operator access and evade detection. DragonForce was responsible for over 7% of Arete ransomware engagements in April, and Arete notes increased activity from the group this year compared to 2025.
A social engineering tactic has reemerged in recent months in which threat actors impersonate IT and helpdesk staff via Microsoft Teams to contact employees and attempt to convince them to install remote access tools like Quick Assist, giving the threat actors remote access to the victim’s environment. This tactic was initially observed in late 2024 and early 2025 and was linked to now-defunct groups like Black Basta and Cactus, but has more recently been observed in intrusions linked to the Akira and Payouts King ransomware groups.
Sources
Arete Internal
Article
Payouts King Utilizes QEMU Emulator to Bypass EDR
Researchers recently identified threat actor campaigns leveraging QEMU, a free open-source virtual machine (VM) emulator, to evade endpoint security solutions. Since QEMU acts as a VM within the target environment, endpoint detection tools cannot scan inside the emulator or detect any malicious files or payloads QEMU contains. Although threat actors have been utilizing QEMU maliciously since 2020, recent activity is attributed to the Payouts King ransomware group and a cluster of threat actors believed to be initial access brokers who have also been exploiting the CitrixBleed2 vulnerability CVE-2025-5777.
What’s Notable and Unique
Payouts King has been observed deploying QEMU since November and uses the VM to create a reverse SSH backdoor to evade detection and install various tools, including Rclone, Chisel, and BusyBox.
In a separate campaign, threat actors are exploiting CVE-2025-5777, a Citrix NetScaler vulnerability that allows attackers to bypass authentication. Once they’ve gained initial access, the threat actors use QEMU to deploy tools inside the VM, which are then used to steal credentials, identify Kerberos usernames, perform Active Directory reconnaissance, and set up FTP servers for staging or data exfiltration.
Analyst Comments
Threat actors continue to focus their efforts on defense evasion, often leveraging legitimate, easily accessible tools such as QEMU. The continued use of QEMU by multiple threat actors highlights the effectiveness of these tactics and the difficulty in detecting and defending against them. To counter this campaign, organizations should proactively monitor for unauthorized QEMU installations, abnormal scheduled tasks, and port forwarding rules.
Sources
QEMU abused to evade detection and enable ransomware delivery
Article
Microsoft Teams Continues to be Leveraged in Social Engineering Attacks
Microsoft warns that threat actors are increasingly abusing Microsoft Teams and relying on legitimate tools to gain access and conduct lateral movement within enterprise networks. The threat actors impersonate IT or helpdesk staff to contact employees via cross-tenant chats and trick them into granting remote access for data theft. Microsoft has observed multiple intrusions with a similar attack chain that utilized commercial remote management software, like Quick Assist and the Rclone utility, to transfer files to an external cloud storage service. This tactic, notably associated with Black Basta and Cactus ransomware operations in late 2024 and early 2025, appears to have resurfaced, with similar activity more recently observed in intrusions linked to the Akira and Payouts King ransomware groups.
What’s Notable and Unique
Initial access is achieved by leveraging external collaboration features in Microsoft Teams to allow impersonation of internal support personnel, tricking users into bypassing security warnings. This reflects abuse of legitimate functionality rather than exploitation of a Microsoft Teams vulnerability.
Following initial access, attackers conduct rapid reconnaissance using Command Prompt and PowerShell to assess privileges, domain membership, and opportunities for lateral movement. Persistence is maintained through Windows Registry modifications, after which attackers leveraged WinRM for lateral movement, targeting domain-joined systems and high-value assets, including domain controllers.
Malicious payloads were staged in user-writable directories and executed through DLL side-loading via trusted, signed applications, enabling covert code execution while blending with legitimate activity. Additional remote management tools were also deployed to support broader access, while Rclone or similar utilities were used to stage and exfiltrate sensitive data to external cloud storage.
Analyst Comments
This activity highlights how modern threat actors can leverage trusted collaboration workflows, remote management tools, and stealthy exfiltration techniques to conduct intrusions through a combination of social engineering and misuse of legitimate functionality. Effective defense depends on layered mitigations that combine identity controls, restricted remote administration, endpoint hardening, network protections, and user awareness measures to disrupt attacker activity at multiple stages of the intrusion lifecycle. To mitigate the risk of this and similar campaigns, users should treat external Teams contacts as untrusted by default, and administrators should restrict or closely monitor remote assistance tools while limiting WinRM usage to controlled systems.
Sources
Cross‑tenant helpdesk impersonation to data exfiltration: A human-operated intrusion playbook
Microsoft: Teams increasingly abused in helpdesk impersonation attacks
Payouts King Takes Aim at the Ransomware Throne



