Article
Fool Us Once … BlackMatter Initial Access Tactics Point to a Possible REvil Association
Arete Analysis
Cyber Threats
Threat Actors

By Kevin Baker
Arete observed an overlap between a recent BlackMatter case and a Q1 2021 REvil case. In both instances, the actors leveraged the NodeJS-based Gootloader to deliver a CobaltStrike payload.
In a March 2021 insight, Arete detailed findings related to complex watering-hole infrastructure used to deliver Gootloader to unsuspecting victims. Highlights included:
REvil actors leveraged compromised web servers of legitimate businesses to host Gootloader.
Actors leveraged search engine optimization (SEO) hijacking to push malicious results to the top.
The malicious search results led to an actor-controlled site masquerading as a legitimate messaging board.
The board contained fake posts by different users, including an “admin” account (Figure 1).
The download link in Figure 1 led to a JS-payload that installed a CobaltStrike (CS) beacon.
The actor leveraged CS to move laterally within the victim’s network to deploy and execute the REvil ransomware.
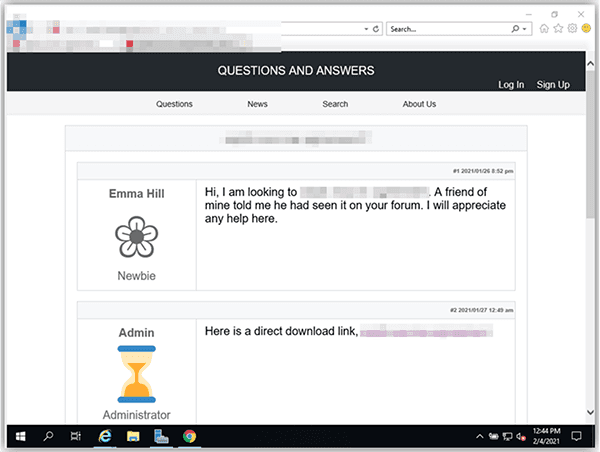
Figure 1 – Actor-controlled forum and fake posts (Source: Arete Forensics Insight)
While watering-hole attacks have been around for years, Arete did not previously observe this specific watering-hole site configuration in the wild or associated with ransomware threat group activity until this specific REvil investigation and response in Q1 2021. Fast forward a few months and REvil is no longer operational and their infrastructure (e.g., communication site, storage sites) is offline. The cause of the REvil’s disappearance is unknown, but the group’s tactics, techniques, and procedures (TTPs) live on with another group: BlackMatter.
In August 2021, Arete was engaged to investigate and respond to a BlackMatter ransomware attack that impacted a law practice in the Midwest United States. Forensic timeline analysis of the observed indicators of compromise (IoCs) led Arete to assess that while the BlackMatter ransomware payload was detonated in August 2021, the initial compromise originally occurred in May 2021 and was attributed to the same type of Gootloader JS payload that impacted the professional services organization we assisted in Q1 2021.
Analysis indicated that in early May 2021, an employee of the victim organization searched in Google for “intercompany agreement transfer pricing sample.” As was the case with the Q1 2021 REvil incident, the actors leveraged SEO hijacking to prioritize the Gootloader infected pages. Arete observed that several keywords were altered to reflect the employee’s search terms (Figure 2).
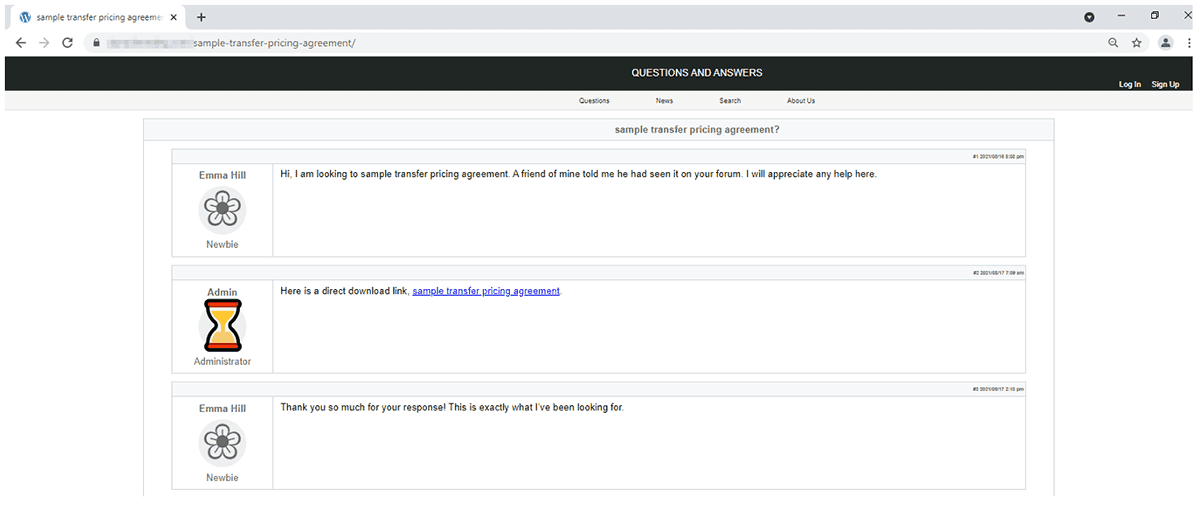
Figure 2 – Gootloader watering hole leads to BlackMatter ransomware deployment.
When compared side by side with the Gootloader watering hole REvil leveraged in Q1 2021, these pages are nearly identical (save for a different link, a different title of the document the user was searching for, and some slight modification to the icons of the fake forum users). Arete observed similarities between the watering hole leveraged by REvil and the watering hole leveraged by BlackMatter (Figure 1, Figure 3, and Figure 4). Similar behavior was previously reported for other Gootloader campaigns, including but not limited to matching “forum themes” and multi-language versions of the forums.
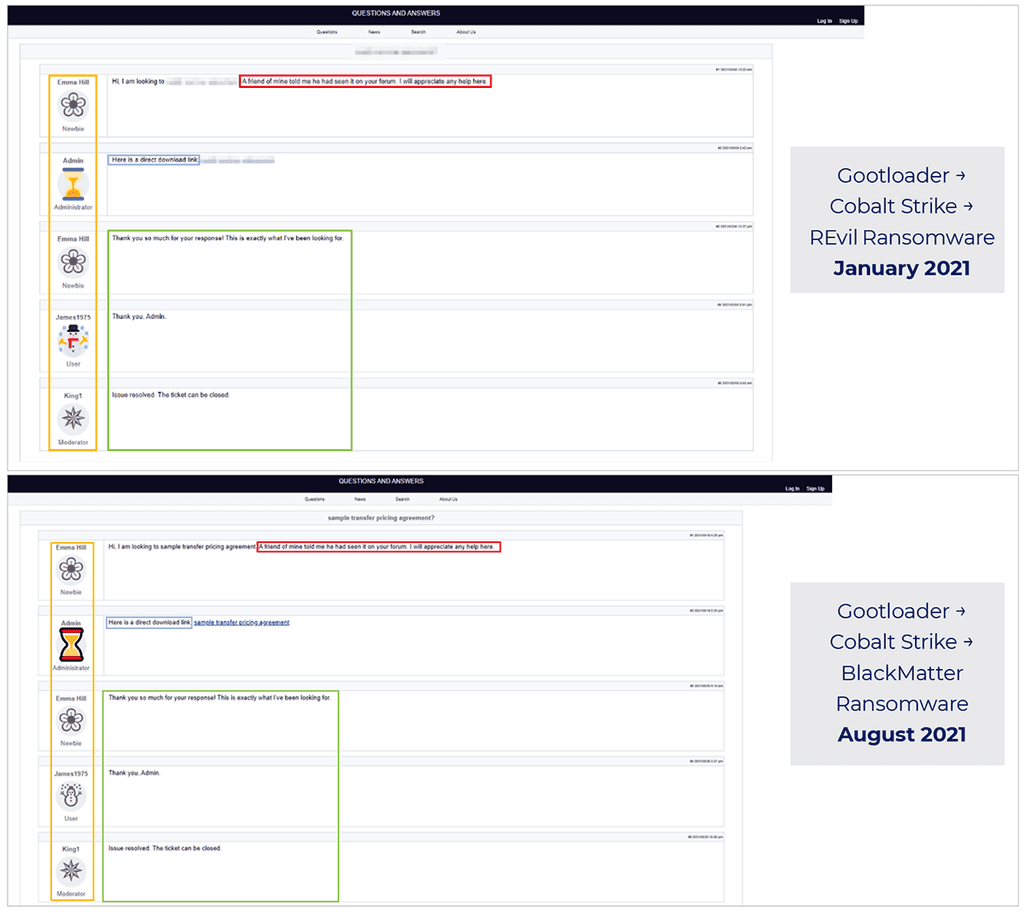
Figure 3 – Comparing REvil to BlackMatter Gootloader-involved attack lifecycle.
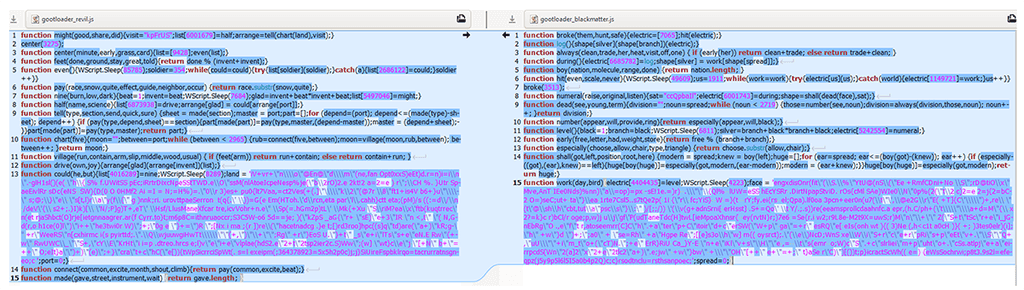
Figure 4 – Gootloader JS payload diff.
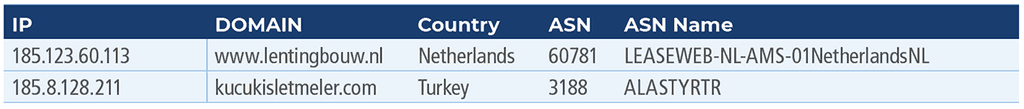
Dynamic analysis of the BlackMatter Gootloader sample resulted in different domain callouts for command-and-control (C2) infrastructure when compared against the older Gootloader sample associated with the Q1 2021 REvil attack. Those domain callouts are documented below for incorporation into EDR/HIDS/NIDS:
While it’s impossible to confirm with absolute certainty the linkage between REvil and BlackMatter, it is notable that both groups share a similar initial access tactic of leveraging fake forum posts weaponized with Gootloader, coupled with SEO hijacking, to gain an initial foothold in targeted environments.
The Arete Threat Intelligence and Forensics teams continue to monitor any potential changes to TTPs for BlackMatter or the re-emergence of REvil.
Acknowledgements
Arete would like to acknowledge the contributions of Senior Forensic Analyst Robert Christine for documenting and timelining the indicators and observables that led to this discovery.
Back to Blog Posts
Article
Arete's 2026 Q1 Crimeware Report
Harness Arete’s unique data and expertise on extortion and ransomware to inform your response to the evolving threat landscape.
Article
CMS Vulnerability Leads to ClickFix Campaign
Threat actors compromised at least 700 education and technology websites in a recent ClickFix campaign by exploiting a critical SQL injection flaw (CVE-2026-26980) in the Ghost content management system (CMS). Adversaries combined the vulnerability with the ClickFix social engineering tactic to steal admin keys and inject a malicious JavaScript that delivers a fake Cloudflare or CAPTCHA verification pop-up, tricking victims into copying and pasting a malicious command into their systems.
What’s Notable and Unique
Rather than targeting the end user first, this campaign is unique in its initial exploitation of the system, followed by social engineering attempts. This hybrid attack style is likely being leveraged to bypass traditional defenses.
This recent campaign also highlights how trusted web properties can be weaponized at scale and coupled with unpatched CMS vulnerabilities. Rather than using the CMS compromise to perpetrate a single attack, threat actors turned it into a supply-chain attack that ultimately affected over 700 trusted websites.
Analyst Comments
As network defenders and their tools enhance threat detection capabilities, adversaries increasingly seek methods to bypass these defenses. By combining vulnerability exploitation, social engineering techniques, and staging for ancillary attacks, this campaign successfully bypassed traditional defenses and inflicted significant impact. Defending against hybrid cyberattacks requires comprehensive security controls beyond simply patching vulnerabilities. Organizations should focus on limiting movement within the environment, detecting abuse of trusted applications, and preventing end-user manipulation.
Sources
700+ education and tech websites hijacked in huge ClickFix malware campaign
Under the engineering hood: Why Malwarebytes chose WordPress as its CMS
Think before you Click(Fix): Analyzing the ClickFix social engineering technique
Ghost CMS Vulnerability Exploited to Infect 700 Sites With ClickFix Malware
Article
Threat Actors Leverage Fake JPEG Files for Initial Access
In a recent campaign, researchers observed threat actors using fake JPEG image files as a delivery mechanism to initiate the deployment of additional malicious components. The false JPEG files are typically distributed via phishing emails or other social engineering-based lures, and are actually PowerShell-based malware that deploys a trojanized version of ConnectWise ScreenConnect to establish and maintain persistence in the compromised environment.
What’s Notable and Unique
This campaign leverages JPEG images as the initial lure, where the images are not merely decoys but part of the infection workflow. Victims are typically led to download or open an image that triggers hidden execution logic or redirects them to a payload-delivery sequence that initiates later stages of the intrusion chain.
The attack chain is designed to blend into legitimate environments, making detection more difficult. Execution typically relies on scripted or native Windows components, often including PowerShell or other living-off-the-land binaries, enabling fileless or near-fileless execution and reducing forensic artifacts on disk.
The multistage design ensures that the initial JPEG does not directly contain the full payload but instead triggers retrieval or decryption steps that progressively assemble the final malicious components in memory.
Analyst Comments
This campaign illustrates how threat actors continue to blur the line between legitimate file handling and malicious execution chains, indicating potential overlap with remote management or administrative tooling. The use of JPEG-based staging combined with script-based execution reflects a broader evolution toward a stealth-first intrusion design, in which file formats serve as triggers rather than payload containers.
Sources
OPERATION SILENTCANVAS : JPEG BASED MULTISTAGE POWERSHELL INTRUSION
Podcast
Cyber Risk and Insurance for Law Firms
In this episode of Bytes of Insight, host Vinny Sakore is joined by Laura Zaroski, Managing Director of the Law Firms Group at Gallagher, as they discuss the evolution of cyber risk for law firms. Tune in for firsthand insights on how to select the right cyber policy, the incident response process, and the nuances of ransom payments and sensitive data.



