Article
Law Enforcement Actions Leave ALPHV/BlackCat Scrambling to Salvage Operations
Cyber Threats
Threat Actors
Combating Ransomware

Through a coordinated law enforcement effort spearheaded by the FBI, ALPHV/BlackCat infrastructure was disrupted on December 7, 2023, in an operation publicly announced on December 19, 2023. After terrorizing businesses and organizations for over two years, the notorious ransomware group may have finally met its match.
What happened to BlackCat’s Infrastructure?
On December 7, 2023, the data leak website for ALPHV/BlackCat went offline and remained offline for more than 30 hours. This is one of the most prolonged disruptions the group has faced, as it previously only experienced periodic outages due to technical hosting issues. The BlackCat data leak site came back online with all data from previous victims removed before apparently being taken down for good on December 19, 2023, when existing BlackCat branding was replaced by an FBI banner including a TOR-based tip line for information on BlackCat and its affiliates.

Figure 1: Law Enforcement Seizure Banner Displayed on Known ALPHV/BlackCat Data Leak Sites on December 19, 2023
The BlackCat Decryptor
Prior to the takedown of BlackCat’s infrastructure, law enforcement maintained access to the threat actor’s environment for months and was able to obtain victim-specific decryption keys to BlackCat’s ransomware executable by monitoring the environment. The FBI used these decryption keys to offer decryption to 500 BlackCat victims as the FBI neared publicizing the takedown. The FBI estimated they were able to save organizations a total of $68 million in ransom demands.
However, based on Arete data, this is likely a conservative number. With an average initial ransom demand of $2.28 million in 2023, BlackCat demands observed by Arete are significantly higher than the demands calculated by law enforcement. While ransom payments are often significantly discounted from the original $2.28 million demand following a negotiation process, it is possible that this action taken by law enforcement could have saved victim organizations as much as five times as what was assessed by the FBI. Alternatively, the gap between Arete and the FBI’s estimated ransom payments may indicate how many organizations had either already paid a ransom before the decryption keys were available or were able to recover without paying the ransom.
The After-Action Report
While the initial data leak site (DLS) disruption nearly two weeks ago caused BlackCat’s operations to decrease significantly, three new victims were posted to the DLS between when the site came back online and when it was finally seized by the FBI. In one of those postings, BlackCat claimed to have reported a new victim to the Securities and Exchange Commission (SEC). In the intervening period, Arete also responded to a BlackCat engagement in which the threat actors utilized an old BlackCat encryptor. Therefore, while the infrastructure takedown certainly disrupted the scale and speed of BlackCat operations, it did not stop the operations of all affiliates.
Shortly after the FBI announced the website seizure on December 19, 2023, ALPHV/BlackCat’s operators stood up a new data leak site and claimed their website was “unseized.” Security researchers assess that BlackCat operators maintained access to the keys used to sign the original data leak site but lost access to their original servers. After standing up the new data leak site, BlackCat made a new post about a victim and stated they will no longer give victims additional time to conduct negotiations. The operators also stated they will harass executive teams and their children, report companies to the SEC and US Department of Health and Human Services (HHS), and release a clearnet (regular internet) link to data on victims.
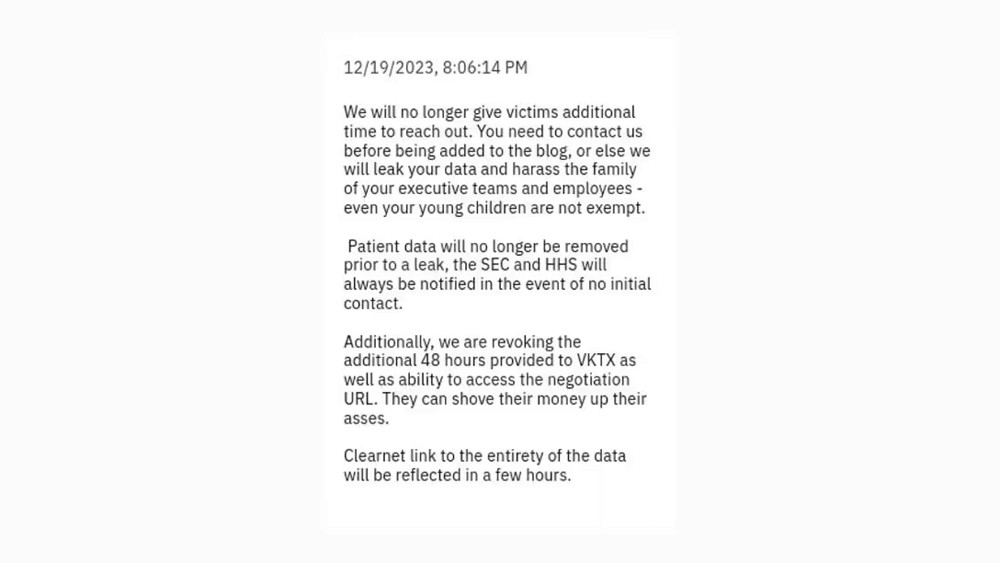
Figure 2 ALPHV/BlackCat Post Excerpt Uploaded December 19, 2023
With a lack of trust in their own infrastructure, BlackCat affiliates began communicating with victims directly via email rather than relying on typical communication methods. While attempting to continue operations to the best of their ability, BlackCat operators reportedly later discovered that law enforcement gained access to a compromised domain controller and issued a concerning statement to their affiliates, giving them permission to “take the gloves off” in future operations.
The statement shared that all previously observed rules, minus the inability to target CIS* countries, no longer apply to BlackCat affiliates, and an increased percentage of ransom payments, now 90%, will go to affiliates. Additionally, several targets that were reportedly previously forbidden, such as hospitals and nuclear power plants, are now fair game for affiliates to target with the BlackCat encryptor. Finally, BlackCat stated they will no longer accept discounts from the original ransom demand. With an average negotiated discount of 63% off the original ransom demand observed by Arete, the inability to negotiate could cost BlackCat victims millions of dollars if they choose to make ransom payments.
Who is ALPHV/BlackCat?
ALPHV/BlackCat is a ransomware-as-a-service (RaaS) group that first emerged in November 2021. The group operates by providing ransomware software and infrastructure to other cybercriminals, who then use it to launch attacks on various targets. The group takes a cut of the ransom payments and leaks the stolen data of its victims on its Dark Web site. The group is also known for its unique extortion methods, which include reporting its victims to the SEC and creating false domains to impersonate victims and leak data.
Since its inception, ALPHV/BlackCat listed over 650 companies on its data leak site, making it one of the most prolific and dangerous ransomware groups active today. Throughout 2023, BlackCat was the most frequently observed ransomware group in Arete’s industry data. Among 56 different ransomware and extortion groups observed in 2023, BlackCat accounted for nearly a quarter of Arete’s overall engagements.
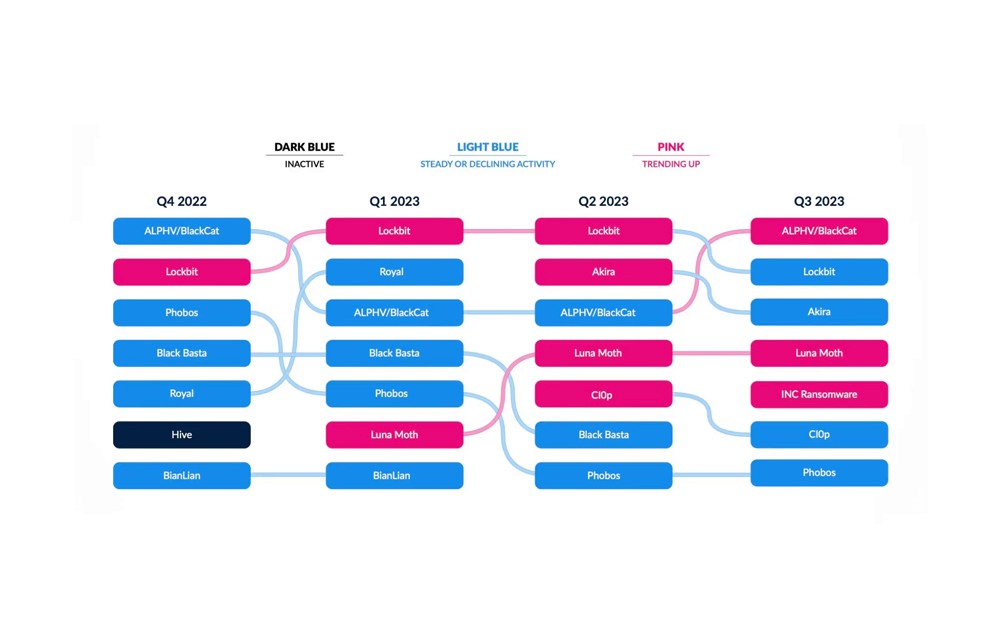
Figure 3: Visual from Arete’s Q3 2023 Crimeware Report
Affiliates of ALPHV/BlackCat include Scattered Spider, the ransomware group behind the brazen cyberattacks against MGM Resorts, Caesars, and more. The FBI and CISA issued a joint advisory about Scattered Spider in November 2023, warning of their use of ALPHV/BlackCat ransomware.
What are the implications of this takedown?
While the full implications of this takedown are currently unknown, it could have significant implications for the ransomware landscape. The takedown may disrupt the activities of many affiliates relying on ALPHV/BlackCat’s ransomware encryptor and infrastructure, likely forcing existing affiliates to move on to other ransomware programs or develop their own. Notably, LockBit ransomware quickly seized the opportunity to advertise that BlackCat affiliates could continue their current operations under LockBit’s RaaS operation. Additionally, this could lead to the emergence of new ransomware variants and groups, with affiliates bringing experience from previous programs. This happened before when law enforcement actions against other ransomware groups, such as DarkSide and REvil, resulted in the formation of new groups, like BlackMatter and Haron. Even before the FBI takedown, Arete observed a splintering of BlackCat affiliates, with groups like Scattered Spider conducting solo operations alongside operations using the BlackCat encryptor.
While the takedown of ALPHV/BlackCat’s websites is a positive development in the fight against ransomware, it is not a definitive victory. Ransomware remains a persistent and evolving threat that requires constant vigilance and collaboration from all stakeholders, including governments, businesses, and individuals.
BlackCat has been a widely impactful ransomware group, in part because it relied on affiliates with diverse means of compromising victims. Arete observed a wide variety of initial access measures in engagements involving ALPHV/BlackCat affiliates, including a sophisticated capability to exploit software and hardware vulnerabilities. Preventing BlackCat attacks and future ransomware attacks from affiliates that escape law enforcement requires a strong patch management program that prioritizes vulnerabilities with publicly released exploit code. Additionally, managing remote management tools in an environment is critical in preventing similar attacks. Arete identified third-party remote access tools as the initial intrusion method in more than eight percent of ALPHV/BlackCat engagements, but analysis of the full lifecycle of an ALPHV/BlackCat engagement showed those tools being used throughout the attacks to enable attacker operations. Neither method is unique to BlackCat operators and remains an important focus for defenders.
Footnotes
*The Commonwealth of Independent States (CIS) is a regional intergovernmental organization formed following the dissolution of the Soviet Union, including Russia, Belarus, Kazakhstan, Moldova, Armenia, Tajikistan, Uzbekistan, Kyrgyzstan, Azerbaijan, and Turkmenistan.
Sources
Back to Blog Posts
Article
Arete's 2026 Q1 Crimeware Report
Harness Arete’s unique data and expertise on extortion and ransomware to inform your response to the evolving threat landscape.
Article
CMS Vulnerability Leads to ClickFix Campaign
Threat actors compromised at least 700 education and technology websites in a recent ClickFix campaign by exploiting a critical SQL injection flaw (CVE-2026-26980) in the Ghost content management system (CMS). Adversaries combined the vulnerability with the ClickFix social engineering tactic to steal admin keys and inject a malicious JavaScript that delivers a fake Cloudflare or CAPTCHA verification pop-up, tricking victims into copying and pasting a malicious command into their systems.
What’s Notable and Unique
Rather than targeting the end user first, this campaign is unique in its initial exploitation of the system, followed by social engineering attempts. This hybrid attack style is likely being leveraged to bypass traditional defenses.
This recent campaign also highlights how trusted web properties can be weaponized at scale and coupled with unpatched CMS vulnerabilities. Rather than using the CMS compromise to perpetrate a single attack, threat actors turned it into a supply-chain attack that ultimately affected over 700 trusted websites.
Analyst Comments
As network defenders and their tools enhance threat detection capabilities, adversaries increasingly seek methods to bypass these defenses. By combining vulnerability exploitation, social engineering techniques, and staging for ancillary attacks, this campaign successfully bypassed traditional defenses and inflicted significant impact. Defending against hybrid cyberattacks requires comprehensive security controls beyond simply patching vulnerabilities. Organizations should focus on limiting movement within the environment, detecting abuse of trusted applications, and preventing end-user manipulation.
Sources
700+ education and tech websites hijacked in huge ClickFix malware campaign
Under the engineering hood: Why Malwarebytes chose WordPress as its CMS
Think before you Click(Fix): Analyzing the ClickFix social engineering technique
Ghost CMS Vulnerability Exploited to Infect 700 Sites With ClickFix Malware
Article
Threat Actors Leverage Fake JPEG Files for Initial Access
In a recent campaign, researchers observed threat actors using fake JPEG image files as a delivery mechanism to initiate the deployment of additional malicious components. The false JPEG files are typically distributed via phishing emails or other social engineering-based lures, and are actually PowerShell-based malware that deploys a trojanized version of ConnectWise ScreenConnect to establish and maintain persistence in the compromised environment.
What’s Notable and Unique
This campaign leverages JPEG images as the initial lure, where the images are not merely decoys but part of the infection workflow. Victims are typically led to download or open an image that triggers hidden execution logic or redirects them to a payload-delivery sequence that initiates later stages of the intrusion chain.
The attack chain is designed to blend into legitimate environments, making detection more difficult. Execution typically relies on scripted or native Windows components, often including PowerShell or other living-off-the-land binaries, enabling fileless or near-fileless execution and reducing forensic artifacts on disk.
The multistage design ensures that the initial JPEG does not directly contain the full payload but instead triggers retrieval or decryption steps that progressively assemble the final malicious components in memory.
Analyst Comments
This campaign illustrates how threat actors continue to blur the line between legitimate file handling and malicious execution chains, indicating potential overlap with remote management or administrative tooling. The use of JPEG-based staging combined with script-based execution reflects a broader evolution toward a stealth-first intrusion design, in which file formats serve as triggers rather than payload containers.
Sources
OPERATION SILENTCANVAS : JPEG BASED MULTISTAGE POWERSHELL INTRUSION
Podcast
Cyber Risk and Insurance for Law Firms
In this episode of Bytes of Insight, host Vinny Sakore is joined by Laura Zaroski, Managing Director of the Law Firms Group at Gallagher, as they discuss the evolution of cyber risk for law firms. Tune in for firsthand insights on how to select the right cyber policy, the incident response process, and the nuances of ransom payments and sensitive data.



