Report
Malware Spotlight: Akira Ransomware
Arete Analysis
Cyber Threats

Download The Report
Executive Summary
Since April 2023, Arete’s Incident Response (IR) team has responded to more than one hundred incidents attributed to the Akira ransomware group. Akira is a prolific threat and quickly established itself as one of the most active ransomware groups alongside ALPHV/BlackCat and LockBit in 2023. In 2024, Akira benefited from law enforcement actions that disrupted LockBit and ALPHV/BlackCat’s operations and has continued to be one of the most active threat actor groups.
This spotlight explores the ransomware group’s observed behavior, background information on the threat actor, and statistics from Incident Response engagements, along with a technical analysis of Akira’s ransomware executable. Finally, we discuss security recommendations to better defend against this evolving cyber threat and mitigate the risk of financial and reputational losses.
Incident Response Data on the Akira Ransomware Group
Background
Akira has evolved into a notable ransomware operation and was among the top variants observed by Arete in the first half of 2024.
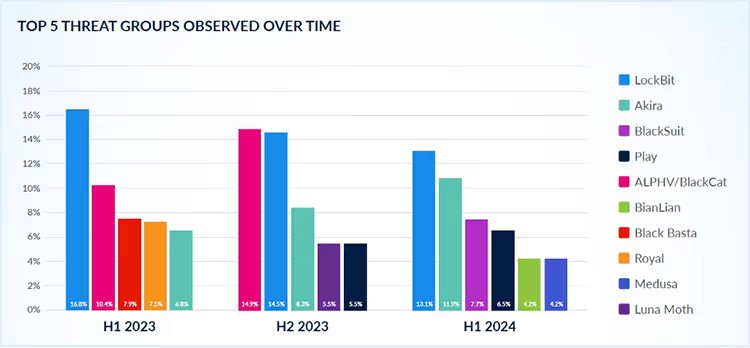
Source: Arete's H1 2024 Crimeware Report
Akira targets a broad range of organizations throughout North America, including Canada, and swiftly lists victims on its data leak site. Targeted sectors include healthcare, hospitality, manufacturing, public and financial services, and professional services. The group maintains Windows and Linux versions of its ransomware and uses virtual private network (VPN) appliances as an initial access vector in 50% of attacks.
Megazord, a variant of Akira, demonstrates the evolution of the group’s ransomware. Introduced around August 2023, this variant is unique due to its Rust-based code, which is a departure from the C++ code of the original Akira ransomware. The Megazord variant also includes different command line arguments and encrypts files with a “.powerranges” extension, which are differentiating attributes.
Technical Analysis
Malware analysis of one of the Windows-based variants revealed that Akira ransomware:
Supports multiple command-line arguments.
Encrypts files on the system and mounted shares.
Adds the following extension to encrypted files (variant dependent): .akira (e.g., file.docx.akira).
Creates a ransom note with the following filename (variant dependent): akira_readme.txt.
References a data leak site in the ransom note that, when accessed, self-identifies the group as AKIRA.
Kills a list of processes and services.
Maintains a list of whitelisted files and directories to ensure it will not render the system unusable, preventing recovery when running a decryptor.
Attempts to prevent system recovery by deleting the system’s volume shadow copies.
Creates a log file with a name based on the date and time: Log-%d-%m-%Y-%H-%M-%S (e.g., Log-19-09-2024-09-21-20.txt).
Execution Pattern/Arguments
Akira ransomware does not need a command line argument to execute and encrypt files in the system. However, Akira supports the following command line arguments:
Command line argument | Description |
|---|---|
-p / –encryption_path | Specify a target directory to encrypt. If not provided, the payload will encrypt the local and mounted shared drives by default. |
-s / –share_file | Encrypt shared volumes/directory files. |
-n / –encryption_percent | Number that represents the percentage of the file that will be encrypted. |
-localonly | Encrypt only local volumes. |
-e/ –exclude | Meant to exclude directories but does not seem to be fully functional. |
Megazord variant:
Command line argument | Description |
|---|---|
–path | Path to encrypt. If not provided, the payload will encrypt the local and mounted shared drives by default. |
–id | Unique token to execute the ransomware. |
–threads | Number of threads (1-1000). |
–h (–help) | Displays help options. |
-log | Logging options with multiple logs supported (info, error, debug). Not displayed by default. |
Examples of how the supported arguments are used:
Akira.exe -p=C:\Users\%USERNAME%\Desktop\MyFiles |
Akira.exe –encryption_percent=10 |
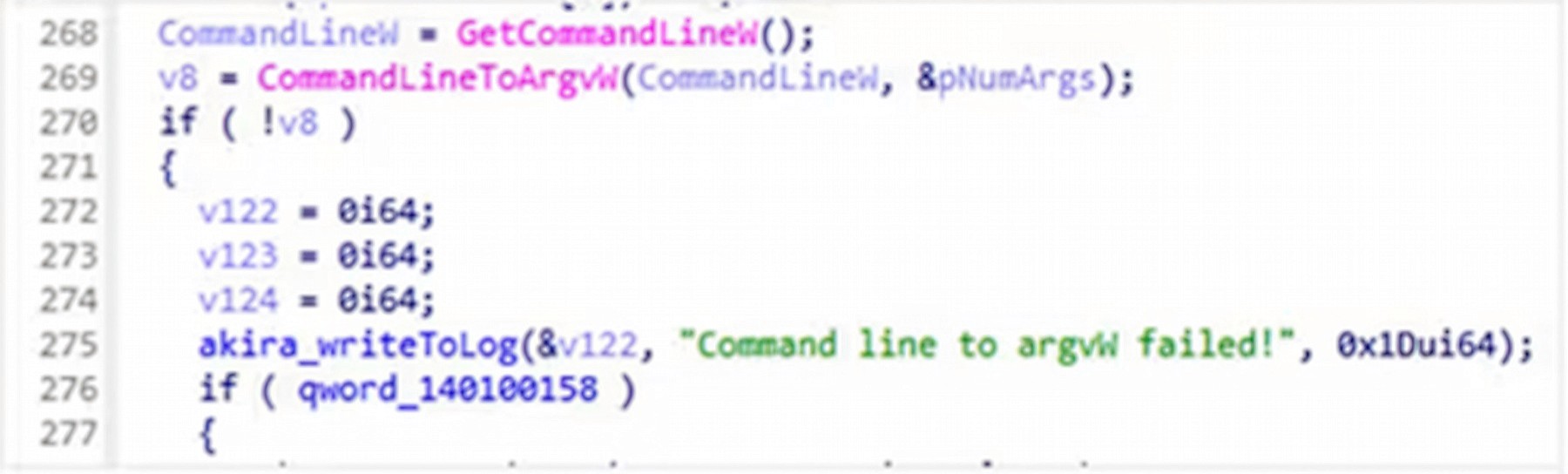
Figure 1. Code in the ransomware written to read command line arguments
Stop Services and Processes
Before file encryption, the ransomware terminates a pre-determined list of processes and services to encrypt as many files as possible. Akira ransomware contains a list of processes it will exclude during process termination, listed below:
Process names:
explorer.exe, sihost.exe, spoolsv.exe, dwm.exe, LogonUI.exe, fontdrvhost.exe, cmd.exe, csrss.exe, smss.exe, SearchUI.exe, lsass.exe, conhost.exe, System, winlogon.exe, services.exe, wininit.exe, Registry, Memory Compression, System Idle Process, Secure System | ||
|---|---|---|
File and Directory Exclusions
The ransomware excludes system-related files and folders, ransomware-related files, and whitelisted extensions during encryption.
Excluded file extensions:
.exe, .dll, .sys, .msi, .lnk, .akira, akira_readme.txt |
Excluded directories:
tmp, temp, winnt, $Recycle.Bin, thumb, System Volume Information, $RECYCLE.BIN, Windows, ProgramData, Trend Micro, ProgramData, Boot |
Inhibit System Recovery
Windows operating systems contain features that can help fix corrupted system files, including shadow copies, which are backups of files created by the Volume Shadow Copy Service (VSS). By deleting shadow copies, the ransomware can prevent victims from restoring files from backups, making it more difficult for them to recover their data without paying the ransom.
The ransomware deletes volume shadow copies before file encryption by starting the following Powershell process and executing the command:
powershell.exe -Command “Get-WmiObject Win32_Shadowcopy | Remove-WmiObject” |
Network Share Discovery
Akira ransomware can enumerate network-mounted shares by scanning the network interfaces. If any are found, it will attempt to encrypt them, as shown below.
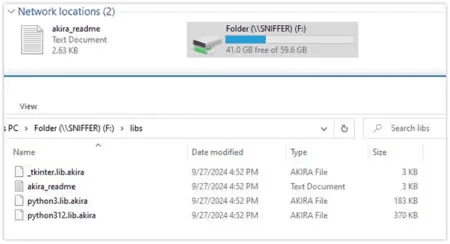
Figure 2. Share drive encrypted
Data Encrypted for Impact
The ransomware initially finds available drives and then loads the files one by one using the Windows API FindFirstFileW and FindNextFileW. The ransomware generates random AES keys to encrypt the files, and after encrypting them, the keys are encrypted using a public RSA key. The resulting key is again encrypted and placed at the end of the file.
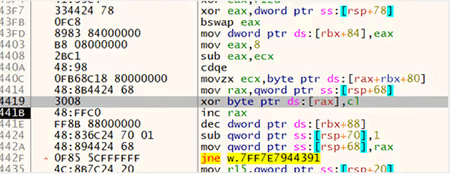
Figure 3. Data encryption code
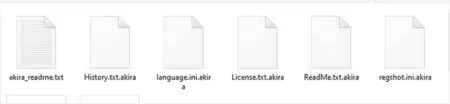
Figure 4. Extension added to the encrypted files
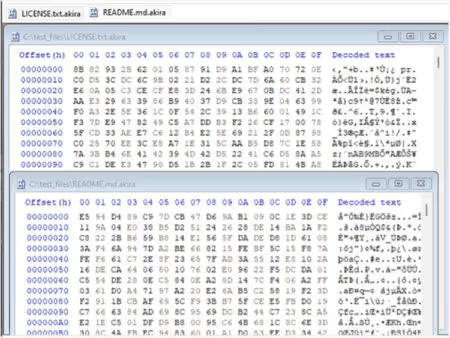
Figure 5. Encrypted files
During execution, the ransomware creates a log file in the working directory where the file is executed from. The log file is named based on the date and time of execution using the following string format: Log-%d-%m-%Y-%H-%M-%S. For example, during execution, the following log file with the name was created: Log-19-09-2024-09-21-20.txt.
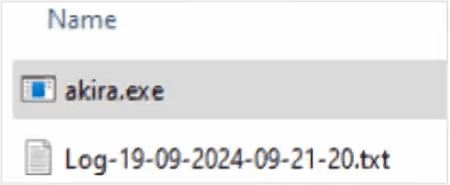
Figure 6. Log file created by Akira
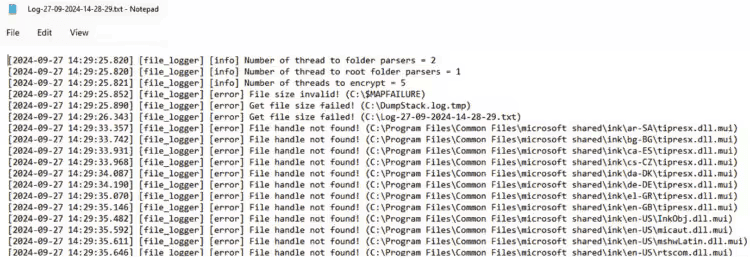
Figure 7. Portion of the log file
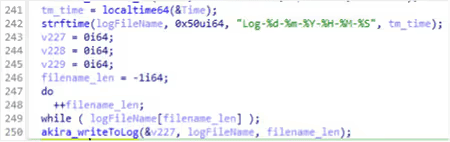
Figure 8. Log file name string format in the code
Upon successful execution, the ransomware creates ransom notes with the file name akira_readme.txt. The Megazord variant creates ransom notes with the same content, but the file name is powerranges.txt.
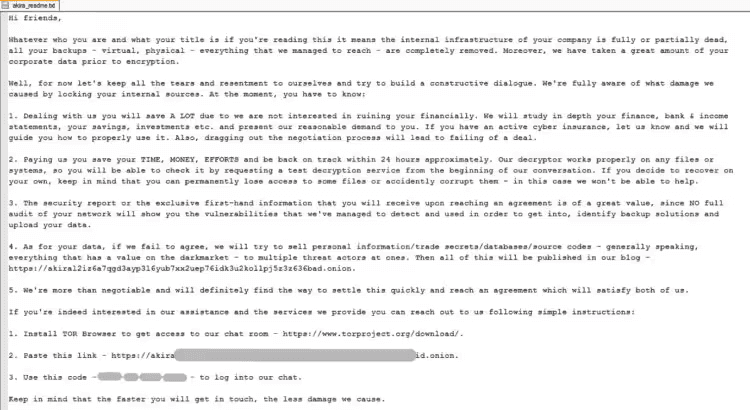
Figure 9. Akira ransom note
Ransom note content:
Hi friends,
| ||
|---|---|---|
Modify Registry
The Windows registry is a database that stores configuration settings and values for the Windows operating system. It manages user preferences, installed software, system configurations, and more. Malware abuses the Windows registry to maintain persistence, hide its presence, disable security settings, and launch malicious scripts. Akira did not perform any registry key modification.
Mutex
The mutex is the fundamental tool for managing shared resources between multiple threads or processes. Typically, ransomware uses a mutex to avoid reinfecting the victim system and causing multiple layers of encryption. The ransomware did not create a mutex during execution.
Network Activity
The ransomware did not try to communicate with a remote server other than encrypting data from mounted shares.
Indicators of Compromise
Indicator | Type | Context |
|---|---|---|
9f873c29a38dd265decb6517a2a1f3b5d4f90ccd42e-b61039086ea0b5e74827e | SHA256 hash | Akira ransomware |
2b00a02196b87445633cabde506b4387979504cf60955f0b-40cf2e4da4f0fd23 | SHA256 hash | Akira ransomware |
237d3c744fd5fc5d7e7a55e4385dff51045a1c6d8ee-7346a270a688ab3791d49 | SHA256 hash | Akira ransomware |
akira_readme.txt, powerranges.txt | File name | Akiraransom notes |
.akira, .powerranges, .akiranew | Extension | Encrypted files extension |
powershell.exe -Command “Get-WmiObject Win32_Shadowcopy | Remove-WmiObject” | Process | Volume Shadow Copy deletion |
Log-19-09-2024-09-21-20.txt | File name | Example log file name created by Akira |
https://akirai2iz6a7qgd3ayp3l6yub7xx2uep76idk3u2kolIpj5z3z636bad[.]onion | URL | TA data leak site (DLS) |
Data Leak Site
The ransom note contains a data leak site (DLS) that, when accessed, displayed the following page, self-identifying the group as Akira:
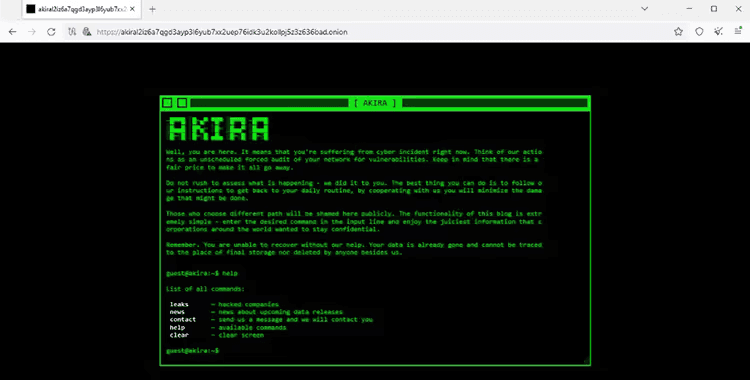
Figure 10. Tor DLS
Tor Chat Site
The ransom note contains a Tor chat site and a unique code used to log into the chat. The Tor chat site displayed the following page:
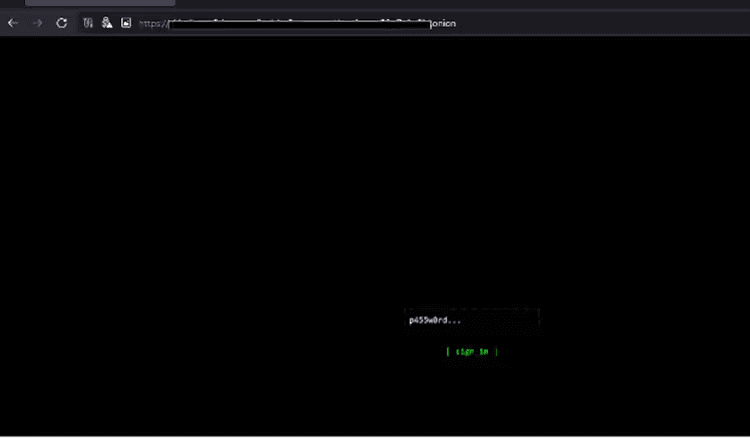
Figure 11. Tor chat site
Detection Mechanisms
Custom Detections and Blocking with Arete Bloktd℠
SentinelOne S1QL 1.0 query syntax (STAR rule):
Volume Shadow Copy Deletion
Akira Ransomware
Note: These threat hunting queries may need to be tuned for your specific network environment.
Yara
Recommended Mitigations
Utilize an endpoint detection and response (EDR) solution with the capability to halt detected processes and isolate systems on the network based on identified conditions.
Block any known attacker C2s in the firewall.
Implement multi-factor authentication on RDP and VPN to restrict access to critical network resources.
Eliminate unnecessary RDP ports exposed to the internet.
Block a high number of SMB connection attempts from one system to others in the network over a short period of time.
Perform periodic dark web monitoring to verify if data is available for sale on the black market.
Perform penetration tests.
Periodically patch systems and update tools.
Monitor connections to the network from suspicious locations.
Monitor downloads and uploads of files to file-sharing services outside standard work hours.
Monitor file uploads from domain controllers to the internet.
Monitor network scans from uncommon servers (e.g., RDP server).
Organizations can find the full list of US government-recommended ransomware prevention and mitigation
guidance here: https://www.cisa.gov/stopransomware/ransomware-guide.
Arete provides data-driven cybersecurity solutions to transform your response to emerging cyber threats.
Click here to learn more.
References
At Arete, we envision a world without cyber extortion, where people, businesses, and governments can thrive. We are taking all that we know from over 9,000 engagements to inform our solutions and strengthen powerful tools to better prevent, detect, and respond to the cyber extortion threats of tomorrow. Our elite team of experts provides unparalleled capabilities to address the entire cyber threat lifecycle, from incident response and restoration to advisory and managed security services. To learn more about our solutions, visit www.areteir.com. | ||
|---|---|---|
Back to Blog Posts
Article
Arete's 2026 Q1 Crimeware Report
Harness Arete’s unique data and expertise on extortion and ransomware to inform your response to the evolving threat landscape.
Article
CMS Vulnerability Leads to ClickFix Campaign
Threat actors compromised at least 700 education and technology websites in a recent ClickFix campaign by exploiting a critical SQL injection flaw (CVE-2026-26980) in the Ghost content management system (CMS). Adversaries combined the vulnerability with the ClickFix social engineering tactic to steal admin keys and inject a malicious JavaScript that delivers a fake Cloudflare or CAPTCHA verification pop-up, tricking victims into copying and pasting a malicious command into their systems.
What’s Notable and Unique
Rather than targeting the end user first, this campaign is unique in its initial exploitation of the system, followed by social engineering attempts. This hybrid attack style is likely being leveraged to bypass traditional defenses.
This recent campaign also highlights how trusted web properties can be weaponized at scale and coupled with unpatched CMS vulnerabilities. Rather than using the CMS compromise to perpetrate a single attack, threat actors turned it into a supply-chain attack that ultimately affected over 700 trusted websites.
Analyst Comments
As network defenders and their tools enhance threat detection capabilities, adversaries increasingly seek methods to bypass these defenses. By combining vulnerability exploitation, social engineering techniques, and staging for ancillary attacks, this campaign successfully bypassed traditional defenses and inflicted significant impact. Defending against hybrid cyberattacks requires comprehensive security controls beyond simply patching vulnerabilities. Organizations should focus on limiting movement within the environment, detecting abuse of trusted applications, and preventing end-user manipulation.
Sources
700+ education and tech websites hijacked in huge ClickFix malware campaign
Under the engineering hood: Why Malwarebytes chose WordPress as its CMS
Think before you Click(Fix): Analyzing the ClickFix social engineering technique
Ghost CMS Vulnerability Exploited to Infect 700 Sites With ClickFix Malware
Article
Threat Actors Leverage Fake JPEG Files for Initial Access
In a recent campaign, researchers observed threat actors using fake JPEG image files as a delivery mechanism to initiate the deployment of additional malicious components. The false JPEG files are typically distributed via phishing emails or other social engineering-based lures, and are actually PowerShell-based malware that deploys a trojanized version of ConnectWise ScreenConnect to establish and maintain persistence in the compromised environment.
What’s Notable and Unique
This campaign leverages JPEG images as the initial lure, where the images are not merely decoys but part of the infection workflow. Victims are typically led to download or open an image that triggers hidden execution logic or redirects them to a payload-delivery sequence that initiates later stages of the intrusion chain.
The attack chain is designed to blend into legitimate environments, making detection more difficult. Execution typically relies on scripted or native Windows components, often including PowerShell or other living-off-the-land binaries, enabling fileless or near-fileless execution and reducing forensic artifacts on disk.
The multistage design ensures that the initial JPEG does not directly contain the full payload but instead triggers retrieval or decryption steps that progressively assemble the final malicious components in memory.
Analyst Comments
This campaign illustrates how threat actors continue to blur the line between legitimate file handling and malicious execution chains, indicating potential overlap with remote management or administrative tooling. The use of JPEG-based staging combined with script-based execution reflects a broader evolution toward a stealth-first intrusion design, in which file formats serve as triggers rather than payload containers.
Sources
OPERATION SILENTCANVAS : JPEG BASED MULTISTAGE POWERSHELL INTRUSION
Podcast
Cyber Risk and Insurance for Law Firms
In this episode of Bytes of Insight, host Vinny Sakore is joined by Laura Zaroski, Managing Director of the Law Firms Group at Gallagher, as they discuss the evolution of cyber risk for law firms. Tune in for firsthand insights on how to select the right cyber policy, the incident response process, and the nuances of ransom payments and sensitive data.



