Article
Managed Detection and Response: A Cornerstone of a Multi-Pronged Approach to Security
Security Recommendations

Ready to Take the Next Step?
The cyber threat landscape is continually evolving, and aided by advanced technology, threats are becoming increasingly more sophisticated. The barrier of entry into cybercrime has become significantly lower in recent years, with artificial intelligence, leaked source code, and Cybercrime-as-a-Service tools enabling even less experienced threat actors to execute damaging attacks.
As the global cost of cybercrime soars, organizations must transform their approach to security to protect their data and systems. Many organizations, especially small and medium-sized businesses (SMBs), face significant challenges in maintaining adequate cybersecurity measures due to resource constraints, evolving threats, and lack of expertise. Limited budgets often prevent SMBs from investing in advanced security tools or employing dedicated cybersecurity staff, leaving them reliant on outdated or insufficient defenses. Additionally, SMBs are prime targets for threat actors, as they often store valuable data but lack the robust defenses of larger enterprises.
While traditional tools like antivirus software and firewalls remain necessary, they are no longer sufficient to defend against advanced persistent threats (APTs) and zero-day exploits. In today’s threat landscape, no single tool or technique can fully secure an organization or individual in today’s complex cyber landscape. To defend against the evolving threat of cyberattacks, organizations should take a multi-pronged approach to cybersecurity, implementing multiple layers of defense mechanisms and strategies to protect digital assets against a variety of cyber threats.
The Value of MDR
A cornerstone of a well-rounded approach to cybersecurity is Managed Detection and Response (MDR), a cybersecurity service that combines advanced threat detection and continuous monitoring delivered by expert teams to protect organizations from evolving cyber threats.
MDR services continuously monitor systems, networks, and endpoints to detect suspicious activity in real- time and identify threats that traditional tools may miss. Unlike other managed security services that focus on prevention, MDR emphasizes active threat hunting and rapid response. By leveraging tools with advanced technologies like artificial intelligence (AI) and machine learning (ML), MDR detects anomalies and potential threats in real-time, enabling the identification of subtle indicators of compromise that traditional methods might miss.
A crucial aspect of MDR is its ability to reduce “dwell time”—the duration between when a breach occurs and when it is detected. By catching breaches early, MDR can help minimize the financial and operational damage caused by cyber incidents. Explore Arete’s Managed Detection and Response solution that combines cutting-edge technology, frontline insights, and deep security expertise to provide fully managed, 24/7/365 endpoint protection.
Economic Benefits of Managed Detection and Response
Small and medium-sized businesses, in particular, benefit from MDR by gaining access to enterprise-grade security without the need for an extensive, in-house team. The subscription-based model democratizes advanced cybersecurity, making it more accessible and scalable for organizations of all sizes. In addition to direct financial savings, MDR also aids in compliance management. With regulatory frameworks becoming stricter, organizations face hefty fines for data breaches or non-compliance. MDR services often include compliance monitoring and reporting, helping businesses stay aligned with regulations and avoid costly penalties.
The Technology-Human Balance in MDR
MDR is built on cutting-edge technology, but its true value lies in the combination of advanced tools with human expertise. Behavioral analytics and cloud-native architectures form the backbone of MDR’s technical capabilities, allowing for rapid identification of suspicious activities and scalable threat intelligence. However, it’s the collaboration between these technologies and skilled security analysts that makes MDR truly effective.
Automated tools can detect patterns, but human analysts bring context and insight, recognizing complex threats such as social engineering attacks, which exploit human behavior rather than technical vulnerabilities.
For an example of how MDR services work in real-world scenarios, check out this Client Success Story, which showcases the effectiveness of managed services in mitigating cyber threats.
Why Arete?
Arete combines cutting-edge technology, frontline insights, and deep security expertise to provide fully managed, 24/7/365 endpoint protection. We handle monitoring, review, and response to alleviate the constraints faced by your staff and enable your team to concentrate on your business.
Powered by real-time actionable intelligence from over 9,000 engagements, our MDR solution brings peace of mind by empowering your organization with data-driven detection tools to spot threats earlier. Arete’s solution is powered by knowledge and expertise from the frontlines of incident response. We also have long-standing partnerships with many insurance carriers and provide recommendations aligned with insurance policy requirements.
To provide enhanced detection, Arete provides our clients with access to Custom Detections and Blocking. Our experts reverse engineer malware to create a powerful threat detection tool that transforms knowledge and experience into actionable intelligence and enhances endpoint detection and response tools with hundreds of custom threat detection rules that act autonomously in seconds.
At Arete, we help organizations of all sizes implement an MDR solution that provides real-time threat detection and response, ensuring that your business is not only secure but also prepared for future challenges. MDR offers the expert protection you need to navigate today’s threat landscape with confidence.
Back to Blog Posts
Article
Ransomware Trends & Data Insights: February 2026
After a slight lull in January, Akira and Qilin returned to dominating ransomware activity in February, collectively accounting for almost half of all engagements that month. The rest of the threat landscape remained relatively diverse, with a mix of persistent threats like INC and PLAY, older groups like Cl0p and LockBit, and newer groups like BravoX and Payouts King. Given current trends, the first quarter of 2026 will likely remain relatively predictable, with the top groups from the second half of 2025 continuing to operate at fairly consistent levels month to month.
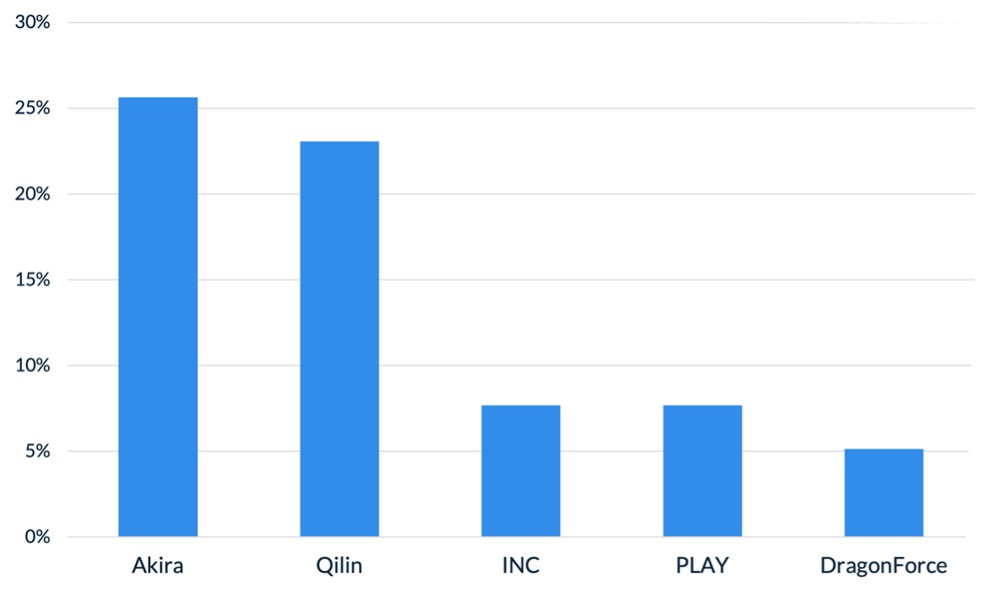
Figure 1. Activity from the top 5 threat groups in February 2026
Throughout the month of February, analysts at Arete identified several trends behind the threat actors perpetrating cybercrime activities:
In February, Arete observed Qilin actively targeting WatchGuard Firebox devices, especially those vulnerable to CVE-2025-14733, to gain initial access to victim environments. CVE-2025-14733 is a critical vulnerability in WatchGuard Fireware OS that allows a remote, unauthenticated threat actor to execute arbitrary code. In addition to upgrading WatchGuard devices to the latest Firebox OS version, which patches the bug, administrators are urged to rotate all shared secrets on affected devices that may have been compromised and may be used in future campaigns.
Reports from February suggest that threat actors are increasingly exploring AI-enabled tools and services to scale malicious activities, demonstrating how generative AI is being integrated into both espionage and financially motivated threat operations. The Google Threat Intelligence Group indicated that state-backed threat actors are leveraging Google’s Gemini AI as a force multiplier to support all stages of the cyberattack lifecycle, from reconnaissance to post-compromise operations. Separate reporting from Amazon Threat Intelligence identified a threat actor leveraging commercially available generative AI services to conduct a large-scale campaign against FortiGate firewalls, gaining access through weak or reused credentials protected only by single-factor authentication.
The Interlock ransomware group recently introduced a custom process-termination utility called “Hotta Killer,” designed to disable endpoint detection and response solutions during active intrusions. This tool exploits a zero-day vulnerability (CVE-2025-61155) in a gaming anti-cheat driver, marking a significant adaptation in the group’s operations against security tools like FortiEDR. Arete is actively monitoring this activity, which highlights the growing trend of Bring Your Own Vulnerable Driver (BYOVD) attacks, in which threat actors exploit legitimate, signed drivers to bypass and disable endpoint security controls.
Sources
Arete Internal
Article
ClickFix Campaign Delivers Custom RAT
Security researchers identified a sophisticated evolution of the ClickFix campaign that aims to compromise legitimate websites before delivering a five-stage malware chain, culminating in the deployment of MIMICRAT. MIMICRAT is a custom remote access trojan (RAT) written in the C/C++ programming language that offers various capabilities early in the attack lifecycle. The attack begins with victims visiting compromised websites, where JavaScript plugins load a fake Cloudflare verification that tricks users into executing a malicious PowerShell script, further displaying the prominence and effectiveness of ClickFix and its user interaction techniques.
Not Your Average RAT
MIMICRAT displays above-average defense evasion and sophistication, including:
A five-stage PowerShell sequence beginning with Event Tracing for Windows and Anti-Malware Scan Interface bypasses, which are commonly used in red teaming for evading detection by EDR and AV toolsets.
The malware later uses a lightweight scripting language that is scripted into memory, allowing malicious actions without files that could easily be detected by an EDR tool.
MIMICRAT uses malleable Command and Control profiles, allowing for a constantly changing communication infrastructure.
The campaign uses legitimate compromised infrastructure, rather than attacker-owned tools, and is prepped to use 17 different languages, which increases global reach and defense evasion.
Analyst Comments
The ClickFix social engineering technique remains an effective means for threat actors to obtain compromised credentials and initial access to victim environments, enabling them to deploy first-stage malware. Coupled with the sophisticated MIMICRAT RAT, the effectiveness of this campaign could increase. Arete will continue monitoring for changes to the ClickFix techniques, the deployment of MIMICRAT in other campaigns, and other pertinent information relating to the ongoing campaign.
Sources
MIMICRAT: ClickFix Campaign Delivers Custom RAT via Compromised Legitimate Websites
Article
Threat Actors Leveraging Gemini AI for All Attack Stages
State-backed threat actors are leveraging Google’s Gemini AI as a force multiplier to support all stages of the cyberattack lifecycle, from reconnaissance to post-compromise operations. According to the Google Threat Intelligence Group (GTIG), threat actors linked to the People’s Republic of China (PRC), Iran, North Korea, and other unattributed groups have misused Gemini to accelerate target profiling, synthesize open-source intelligence, identify official email addresses, map organizational structures, generate tailored phishing lures, translate content, conduct vulnerability testing, support coding tasks, and troubleshoot malware development. Cybercriminals are increasingly exploring AI-enabled tools and services to scale malicious activities, including social engineering campaigns such as ClickFix, demonstrating how generative AI is being integrated into both espionage and financially motivated threat operations.
What’s Notable and Unique
Threat actors are leveraging Gemini beyond basic reconnaissance, using it to generate polished, culturally nuanced phishing lures and sustain convincing multi-turn social engineering conversations that minimize traditional red flags.
In addition, threat actors rely on Gemini for vulnerability research, malware debugging, code generation, command-and-control development, and technical troubleshooting, with PRC groups emphasizing automation and vulnerability analysis, Iranian actors focusing on social engineering and malware development, and North Korean actors prioritizing high-fidelity target profiling.
Beyond direct operational support, adversaries have abused public generative AI platforms to host deceptive ClickFix instructions, tricking users into pasting malicious commands that deliver macOS variants of ATOMIC Stealer.
AI is also being integrated directly into malware development workflows, as seen with CoinBait’s AI-assisted phishing kit capabilities and HonestCue’s use of the Gemini API to dynamically generate and execute in-memory C# payloads.
Underground forums show strong demand for AI-powered offensive tools, with offerings like Xanthorox falsely marketed as custom AI but actually built on third-party commercial models integrated through open-source frameworks such as Crush, Hexstrike AI, LibreChat-AI, and Open WebUI, including Gemini.
Analyst Comments
The increasing misuse of generative AI platforms like Gemini highlights a rapidly evolving threat landscape in which state-backed and financially motivated actors leverage AI as a force multiplier for reconnaissance, phishing, malware development, and post-compromise operations. At the same time, large-scale model extraction attempts and API abuse demonstrate emerging risks to AI service integrity, intellectual property, and the broader AI-as-a-Service ecosystem. While these developments underscore the scalability and sophistication of AI-enabled threats, continued enforcement actions, strengthened safeguards, and proactive security testing by providers reflect ongoing efforts to mitigate abuse and adapt defenses in response to increasingly AI-driven adversaries.
Sources
GTIG AI Threat Tracker: Distillation, Experimentation, and (Continued) Integration of AI for Adversarial Use
Article
2025 VMware ESXi Vulnerability Exploited by Ransomware Groups
Ransomware groups are actively exploiting CVE‑2025‑22225, a VMware ESXi arbitrary write vulnerability that allows attackers to escape the VMX sandbox and gain kernel‑level access to the hypervisor. Although VMware (Broadcom) patched this flaw in March 2025, threat actors had already exploited it in the wild, and CISA recently confirmed that threat actors are exploiting CVE‑2025‑22225 in active campaigns.
What’s Notable and Unique
Chinese‑speaking threat actors abused this vulnerability at least a year before disclosure, via a compromised SonicWall VPN chain.
Threat researchers have observed sophisticated exploit toolkits, possibly developed well before public disclosure, that chain this bug with others to achieve full VM escape. Evidence points to targeted activity, including exploitation via compromised VPN appliances and automated orchestrators.
Attackers with VMX level privileges can trigger a kernel write, break out of the sandbox, and compromise the ESXi host. Intrusions observed in December 2025 showed lateral movement, domain admin abuse, firewall rule manipulation, and staging of data for exfiltration.
CISA has now added CVE-2025-22225 to its Known Exploited Vulnerabilities (KEV) catalog, underscoring ongoing use by ransomware attackers.
Analyst Comments
Compromise of ESXi hypervisors significantly amplifies operational impact, allowing access to and potential encryption of dozens of VMs simultaneously. Organizations running ESXi 7.x and 8.x remain at high risk if patches and mitigations have not been applied. Therefore, clients are recommended to apply VMware patches from VMSA‑2025‑0004 across all ESXi, Workstation, and Fusion deployments. Enterprises are advised to assess their setups in order to reduce risk, as protecting publicly accessible management interfaces is a fundamental security best practice.
Sources
CVE-2025-22225 in VMware ESXi now used in active ransomware attacks
The Great VM Escape: ESXi Exploitation in the Wild
VMSA-205-004: VMware ESXi, Workstation, and Fusion updates address multiple vulnerabilities (CVE-205-22224, CVE-2025-22225, CVE-2025-22226)