Article
New Group Emerges with Similarities to ALPHV/BlackCat
Threat Actors
Arete Analysis

A new Ransomware-as-a-Service (RaaS) group calling themselves Cicada3301 emerged in early June 2024 and has been using recruitment posts in dark web forums to attract new affiliates. As with many of the current active RaaS organizations, Cicada3301 uses double extortion, encrypting victim systems and stealing sensitive data. They have a data leak site (DLS) on the dark web where they have been posting victims since mid-June. The group has been observed encrypting Linux/VMware ESXi in addition to Windows operating systems.
Similarities with ALPHV/BlackCat
A recent analysis of Cicada3301’s ransomware conducted by cyber researchers discovered several significant code overlaps with the ransomware used by ALPHV, the prolific threat group who was targeted by law enforcement earlier this year and subsequently shut down their RaaS. According to researchers from Truesec, Cicada3301 and ALPHV ransomware similarities include:
Written in Rust programming language
Use the ChaCha20 algorithm for encryption
Use almost identical commands to shutdown VM and remove snapshots
Use the same command parameters to provide a graphic output on encryption
Use intermittent encryptions on files larger than 100MB
Use a similar naming convention for the ransom note file and the same key parameter used to decrypt the ransomware note
In addition to the code overlaps, Arete has also observed similarities in the format and design of the Tor chats Cicada3301 uses to communicate ransom payments to its victims. Like the Tor chats ALPHV used, Cicada3301’s has a similar layout, with certain words bolded in the instructions, a countdown timer, two prices listed based on whether the victim pays within the time limit posted, and payments are accepted in both Bitcoin and Monero.
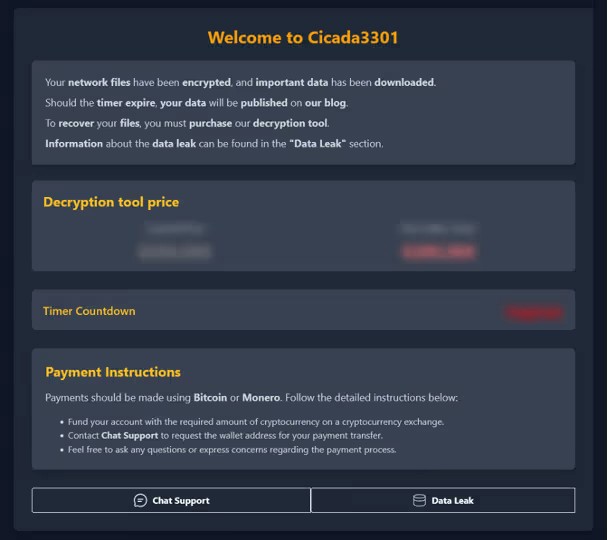
Figure 1. Screenshot of TOR chat used by Cicada3301 (source: Arete)
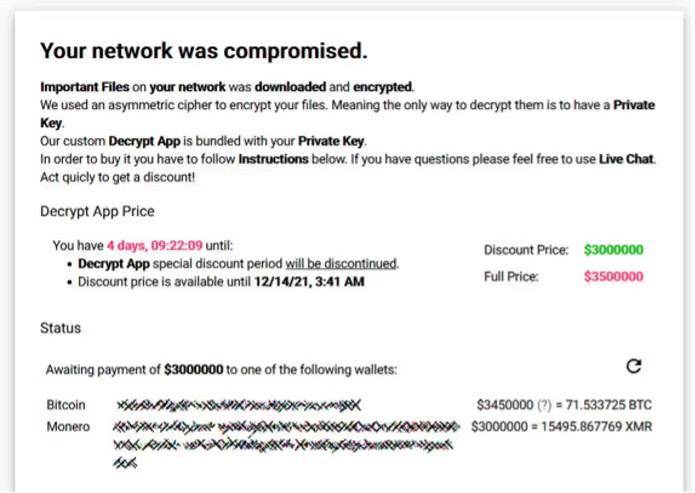
Figure 2. Screenshot of TOR chat used by ALPHV (source: bleepingcomputer.com)
Will the Real Cicada Please Stand Up?
This new ransomware group also appears to have taken their name from Cicada 3301, which was an unknown group who posted elaborate puzzles on the internet between 2012 and 2014. Solving the puzzles required knowledge of computer science and data security concepts such as coding, cryptography, and encryption. The last puzzle posted by the group was in early 2014 and has still not been solved. Although the purpose of the puzzles, and individuals who created them remains a mystery, there is no indication that this current ransomware group has any association with the original Cicada 3301. This wouldn’t be the first time a threat actor has used the name, as an unrelated group of hackers operating in 2015 also called themselves 3301.
Analyst Comments
At this time, it is too early to assess whether the similarities between the two groups are coincidental, or if there is a connection in the form of a rebranding of ALPHV, a new group working with former developers from ALPHV, or if ALPHV’s ransomware code was sold after the RaaS shut down its operations earlier this year. Following ALPHV’s exit scam and departure from the ransomware landscape, it was assumed members of the RaaS would rebrand or re-affiliate with other threat groups, so any of these connections are plausible. However, with 24 victims already posted to its DLS in less than three months, Cicada3301 already appears to be an emerging threat in the near-term, regardless of who is ultimately behind the new RaaS.
Sources
Back to Blog Posts
Article
Arete's 2026 Q1 Crimeware Report
Harness Arete’s unique data and expertise on extortion and ransomware to inform your response to the evolving threat landscape.
Article
CMS Vulnerability Leads to ClickFix Campaign
Threat actors compromised at least 700 education and technology websites in a recent ClickFix campaign by exploiting a critical SQL injection flaw (CVE-2026-26980) in the Ghost content management system (CMS). Adversaries combined the vulnerability with the ClickFix social engineering tactic to steal admin keys and inject a malicious JavaScript that delivers a fake Cloudflare or CAPTCHA verification pop-up, tricking victims into copying and pasting a malicious command into their systems.
What’s Notable and Unique
Rather than targeting the end user first, this campaign is unique in its initial exploitation of the system, followed by social engineering attempts. This hybrid attack style is likely being leveraged to bypass traditional defenses.
This recent campaign also highlights how trusted web properties can be weaponized at scale and coupled with unpatched CMS vulnerabilities. Rather than using the CMS compromise to perpetrate a single attack, threat actors turned it into a supply-chain attack that ultimately affected over 700 trusted websites.
Analyst Comments
As network defenders and their tools enhance threat detection capabilities, adversaries increasingly seek methods to bypass these defenses. By combining vulnerability exploitation, social engineering techniques, and staging for ancillary attacks, this campaign successfully bypassed traditional defenses and inflicted significant impact. Defending against hybrid cyberattacks requires comprehensive security controls beyond simply patching vulnerabilities. Organizations should focus on limiting movement within the environment, detecting abuse of trusted applications, and preventing end-user manipulation.
Sources
700+ education and tech websites hijacked in huge ClickFix malware campaign
Under the engineering hood: Why Malwarebytes chose WordPress as its CMS
Think before you Click(Fix): Analyzing the ClickFix social engineering technique
Ghost CMS Vulnerability Exploited to Infect 700 Sites With ClickFix Malware
Article
Threat Actors Leverage Fake JPEG Files for Initial Access
In a recent campaign, researchers observed threat actors using fake JPEG image files as a delivery mechanism to initiate the deployment of additional malicious components. The false JPEG files are typically distributed via phishing emails or other social engineering-based lures, and are actually PowerShell-based malware that deploys a trojanized version of ConnectWise ScreenConnect to establish and maintain persistence in the compromised environment.
What’s Notable and Unique
This campaign leverages JPEG images as the initial lure, where the images are not merely decoys but part of the infection workflow. Victims are typically led to download or open an image that triggers hidden execution logic or redirects them to a payload-delivery sequence that initiates later stages of the intrusion chain.
The attack chain is designed to blend into legitimate environments, making detection more difficult. Execution typically relies on scripted or native Windows components, often including PowerShell or other living-off-the-land binaries, enabling fileless or near-fileless execution and reducing forensic artifacts on disk.
The multistage design ensures that the initial JPEG does not directly contain the full payload but instead triggers retrieval or decryption steps that progressively assemble the final malicious components in memory.
Analyst Comments
This campaign illustrates how threat actors continue to blur the line between legitimate file handling and malicious execution chains, indicating potential overlap with remote management or administrative tooling. The use of JPEG-based staging combined with script-based execution reflects a broader evolution toward a stealth-first intrusion design, in which file formats serve as triggers rather than payload containers.
Sources
OPERATION SILENTCANVAS : JPEG BASED MULTISTAGE POWERSHELL INTRUSION
Podcast
Cyber Risk and Insurance for Law Firms
In this episode of Bytes of Insight, host Vinny Sakore is joined by Laura Zaroski, Managing Director of the Law Firms Group at Gallagher, as they discuss the evolution of cyber risk for law firms. Tune in for firsthand insights on how to select the right cyber policy, the incident response process, and the nuances of ransom payments and sensitive data.



