Article
PYSA: 2020 to Now
Arete Analysis
Cybersecurity Trends
Cyber Threats

PYSA is the newest variant of the Mespinoza Ransomware as a Service (RaaS) family, which was first observed infecting victims in the wild in December 2019. PYSA is likely a reference to the open-source web application auditing tool PYSA (Protect Your System Amigo) released by security engineers at Facebook.
Like Ryuk, PYSA is dubbed a “big game hunter” for their tendency to target large corporations. Based on their advanced encryption methods, double extortion tactics, and desire to distinguish themselves, this up-and-coming ransomware group is “one to watch.”
Since Q3 2020, Arete has responded to 26 total PYSA cases. With an average ransom payment of $346,603, PYSA ranks third highest in average ransom payouts tracked by Arete through July 2021. Additionally, Arete has observed a steady increase in cases sine Q3 2020 (see Figure 1).
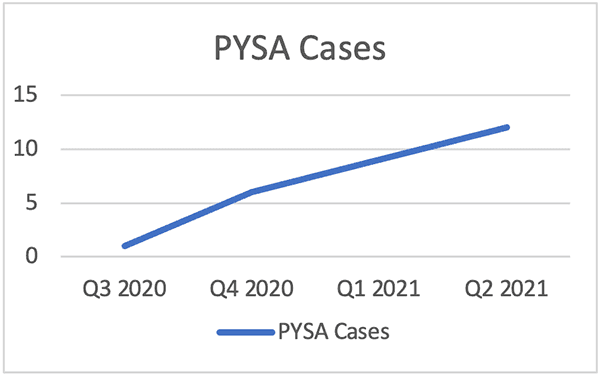
Figure 1: PYSA cases over a one-year period.
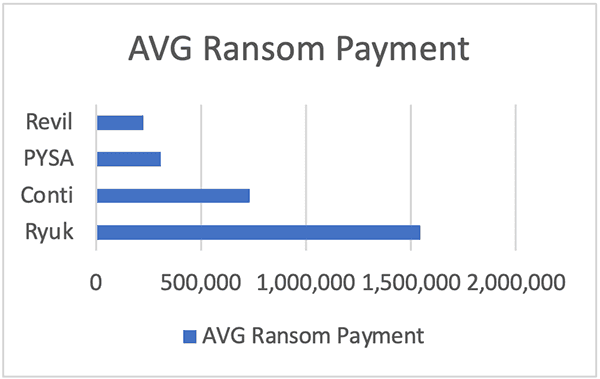
Figure 2: Arete PYSA cases average ransom payment.
Targeting Big Game
PYSA targets large companies or organizations susceptible to extortion, where business downtime would pose a significant impact to operations. By extorting companies with the threat of publishing sensitive data, PYSA increases the chances of ransom payments. The top three sectors targeted by PYSA include K-12 school systems (36%), professional services (20%), and healthcare providers (12%). See Figure 3 for all targeted sectors.
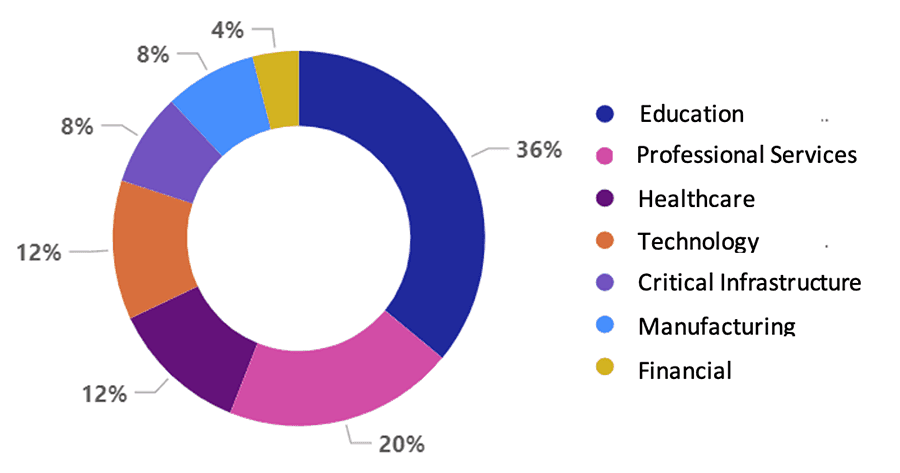
Figure 3: Arete PYSA cases, all targeted sectors.
Sophisticated Criminals
PYSA exhibits discipline by first surveying compromised systems to determine a victim’s potential “extortion value.” Open-source reporting indicates that PYSA searches not only for common keywords (e.g., PII, balance, routing), but also for keywords (e.g., illegal, fraud, criminal) that could be evidence of illegal activities by the victim.
Arete also identified some other key PYSA activity — specifically, that PYSA occasionally publishes data on leak sites after payment, provides decryptors that partially corrupt data, and stops communication for multiple days during negotiations.

Figure 4: Average time of business interruption.
Infection vector and persistence: Human-operated ransomware
Arete identified the following PYSA tactics, techniques, and procedures (TTPs) as being consistent with manually operated ransomware during the initial access phase:
Uses brute force remote desktop protocol (RDP) attacks against central management consoles, domain controllers, and Active Directory accounts.
Exfiltrates password databases prior to exploitation.
Leverages Mimikatz in victim environments, likely to gain access to credentials.
Additionally, Arete observed the following persistence toolset as part of PYSA campaigns:
Gasket. A backdoor written in the Go programming language, Gasket is designed as a backup to RDP to maintain access to the network. Gasket has many capabilities (e.g., “MagicSocks”) that allow PYSA to tunnel traffic to an externally controlled server.
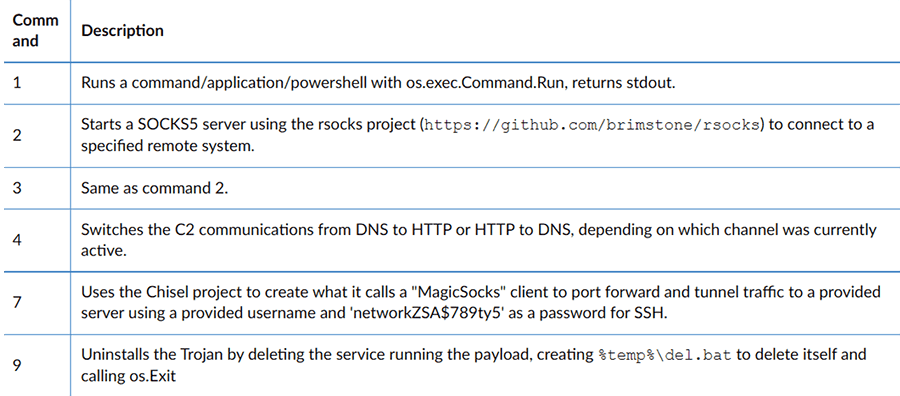
Figure 5: Gasket functionality.
MagicSocks. Leverages code from the Chisel project to tunnel traffic from the local system to an external, actor-controlled server. Next, uses Chisel code to tunnel traffic out of the local system to a landing page (“creatordampfe[.]xyz”) before routing the traffic to an unknown actor-controlled server.
Advanced encryption techniques
According to open-source data, PYSA uses Crypto++ to encrypt victim files with both RSA-4096 and AES-256-CFB. The group appends the encrypted files with the “.pysa” extension and leverages an allowlist and denylist to determine which files to encrypt.
The denylist contains all files to be encrypted.
The allowlist includes vital directories, such as Windows and Boot, which, if encrypted, would make recovery via the decryptor impossible. After, PYSA drops the ransom note (Figure 6) in every directory listed in the denylist.
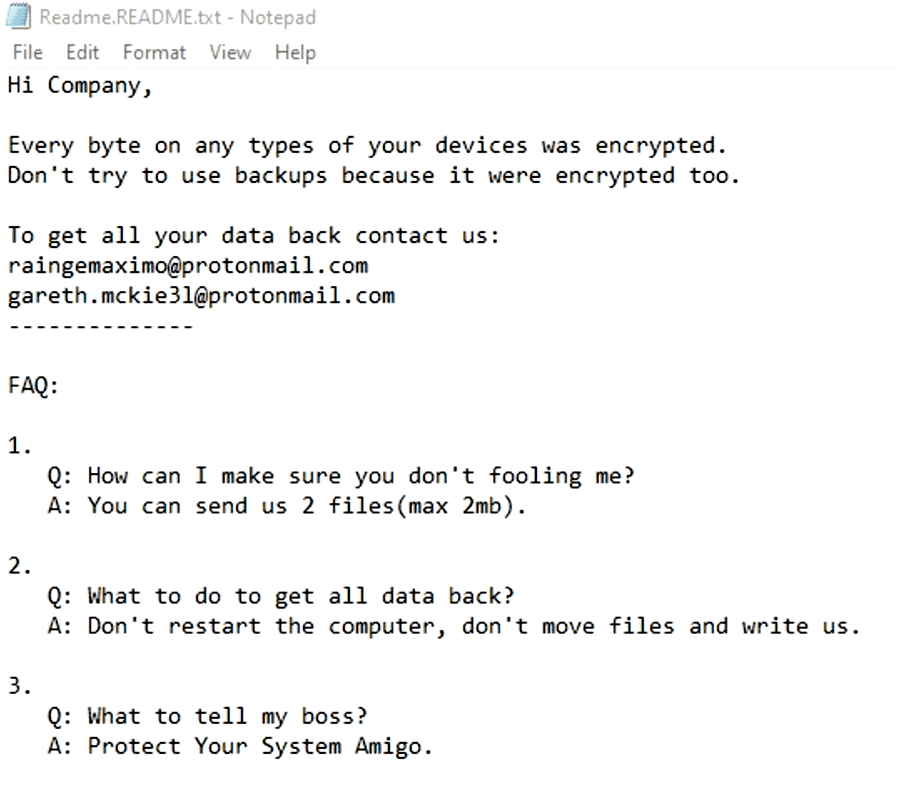
Figure 6: PYSA ransom note.
PYSA threat likely to remain steady
PYSA utilized the rapid shift of corporations to remote work during COVID-19 for opportunistic targeting against RDP and remote admin infrastructure. Arete asserts that the threat posed by PYSA campaigns will likely remain steady, with PYSA targeting larger corporations across sectors to demand higher ransom payments. PYSA’s discipline, target selection, and advanced encryption techniques make them a credible threat on the ransomware scene.
How Arete can help you “Protect Your Systems Amigo”
Arete has a complete suite of managed security services, including managed detection and response (MDR), SentinelOne Endpoint Detection and Response (EDR) software deployment, and Arsinal threat hunting services for defending against ransomware attacks.
The following rulesets would detect PYSA activity on a client endpoint:
PowerShell used to disable Windows Defender Protection.
Lsass dump.
Firewall Exception for Remote Desktop.
MS Windows Defender stopped.
Security Tool Services stopped.
Volume Shadow Copy deletion.
Process Masquerading in Registry – Svchost.
Advanced Port Scanner Tool download.
Advanced Port Scanner Process Masquerading.
Advanced Port Scanner Process.
Advanced Port Scanner File detected.
Mimikatz Process Execution.
Advanced IP Scanner Network Mapping Tool download.
Advanced IP Scanner Network Mapping Tool Process.
Advanced IP Scanner Network Mapping File detected.
Advanced IP Scanner Process Masquerading.
Indicators
Ransom Note Emails
johnfitzgerald@onionmail.org
cristianpalmerss@protonmail.com
wcraijones@protonmail.com
dec_restore1@outlook.com
zljanczplaizr@onionmail.org
EfreTavernia@protonmail.com
lizawilkinson@onionmail.org
Makailahuff@protonmail.com
Davionfinley@protonmail.com
joedansereau@onionmail.org
m0arc7bdhsohar@onionmail.org
david_ansty@protonmail.com
t.trstram@protonmail.com
Resources
https://unit42.paloaltonetworks.com/gasket-and-magicsocks-tools-install-mespinoza-ransomware/
https://blog.emsisoft.com/en/38840/ransomware-profile-mespinoza-pysa/
https://www.databreaches.net/k-12-school-districts-fall-prey-to-pysa-ransomware/
https://www.cert.ssi.gouv.fr/uploads/CERTFR-2020-CTI-003.pdf
https://www.documentcloud.org/documents/20514564-pysa-ransomware-bc
Back to Blog Posts
Article
Arete's 2026 Q1 Crimeware Report
Harness Arete’s unique data and expertise on extortion and ransomware to inform your response to the evolving threat landscape.
Article
CMS Vulnerability Leads to ClickFix Campaign
Threat actors compromised at least 700 education and technology websites in a recent ClickFix campaign by exploiting a critical SQL injection flaw (CVE-2026-26980) in the Ghost content management system (CMS). Adversaries combined the vulnerability with the ClickFix social engineering tactic to steal admin keys and inject a malicious JavaScript that delivers a fake Cloudflare or CAPTCHA verification pop-up, tricking victims into copying and pasting a malicious command into their systems.
What’s Notable and Unique
Rather than targeting the end user first, this campaign is unique in its initial exploitation of the system, followed by social engineering attempts. This hybrid attack style is likely being leveraged to bypass traditional defenses.
This recent campaign also highlights how trusted web properties can be weaponized at scale and coupled with unpatched CMS vulnerabilities. Rather than using the CMS compromise to perpetrate a single attack, threat actors turned it into a supply-chain attack that ultimately affected over 700 trusted websites.
Analyst Comments
As network defenders and their tools enhance threat detection capabilities, adversaries increasingly seek methods to bypass these defenses. By combining vulnerability exploitation, social engineering techniques, and staging for ancillary attacks, this campaign successfully bypassed traditional defenses and inflicted significant impact. Defending against hybrid cyberattacks requires comprehensive security controls beyond simply patching vulnerabilities. Organizations should focus on limiting movement within the environment, detecting abuse of trusted applications, and preventing end-user manipulation.
Sources
700+ education and tech websites hijacked in huge ClickFix malware campaign
Under the engineering hood: Why Malwarebytes chose WordPress as its CMS
Think before you Click(Fix): Analyzing the ClickFix social engineering technique
Ghost CMS Vulnerability Exploited to Infect 700 Sites With ClickFix Malware
Article
Threat Actors Leverage Fake JPEG Files for Initial Access
In a recent campaign, researchers observed threat actors using fake JPEG image files as a delivery mechanism to initiate the deployment of additional malicious components. The false JPEG files are typically distributed via phishing emails or other social engineering-based lures, and are actually PowerShell-based malware that deploys a trojanized version of ConnectWise ScreenConnect to establish and maintain persistence in the compromised environment.
What’s Notable and Unique
This campaign leverages JPEG images as the initial lure, where the images are not merely decoys but part of the infection workflow. Victims are typically led to download or open an image that triggers hidden execution logic or redirects them to a payload-delivery sequence that initiates later stages of the intrusion chain.
The attack chain is designed to blend into legitimate environments, making detection more difficult. Execution typically relies on scripted or native Windows components, often including PowerShell or other living-off-the-land binaries, enabling fileless or near-fileless execution and reducing forensic artifacts on disk.
The multistage design ensures that the initial JPEG does not directly contain the full payload but instead triggers retrieval or decryption steps that progressively assemble the final malicious components in memory.
Analyst Comments
This campaign illustrates how threat actors continue to blur the line between legitimate file handling and malicious execution chains, indicating potential overlap with remote management or administrative tooling. The use of JPEG-based staging combined with script-based execution reflects a broader evolution toward a stealth-first intrusion design, in which file formats serve as triggers rather than payload containers.
Sources
OPERATION SILENTCANVAS : JPEG BASED MULTISTAGE POWERSHELL INTRUSION
Podcast
Cyber Risk and Insurance for Law Firms
In this episode of Bytes of Insight, host Vinny Sakore is joined by Laura Zaroski, Managing Director of the Law Firms Group at Gallagher, as they discuss the evolution of cyber risk for law firms. Tune in for firsthand insights on how to select the right cyber policy, the incident response process, and the nuances of ransom payments and sensitive data.



