Report
Threat Actor Spotlight: BlackSuit Ransomware
Arete Analysis
Tips

Download The Report
Executive Summary
Since May 2023, Arete’s Incident Response (IR) team has responded to multiple BlackSuit ransomware engagements against organizations in the healthcare, financial services, manufacturing, professional services, public service, entertainment, and retail sectors. This spotlight explores the ransomware behavior observed, statistics from IR engagements, and background information on the threat actor. Finally, we discuss security recommendations to better defend against this evolving cyber threat and mitigate the risk of financial and reputational losses arising from these incidents.
Incident Response Data on BlackSuit Ransomware
The information below is based on BlackSuit incidents investigated by Arete since May 2023. Our IR and teams work together to analyze key data points during every ransomware engagement and form real-time threat actor (TA) insights.
Arete has investigated dozens of engagements involving BlackSuit.
We have been extremely successful in negotiating discounted ransoms with this TA.
The highest observed ransom demand is around $18 million.
The average initial demand is around $2.5 million.
The average ransom payment facilitated is around $500,000.
Commonly observed methods of intrusions include remote desktop protocol (RDP), virtual private network (VPN), and firewall vulnerabilities.
Tools observed during the investigations include CobaltStrike, WinRAR, PUTTY, Rclone, Advanced IP Scanner, Network Scanner, Mimikatz, and GMER.
A commonly observed ransom note filename is readme.blacksuit.txt.
In some instances, backups were encrypted or deleted, while in others, backups were used for restoration.
Background
The information about the BlackSuit threat actor group in this section was shared in Arete’s 2024 Q1 Crimeware Report.
The most notable newcomer in Q1 was BlackSuit, the third most active group of Q1. Although Arete first observed BlackSuit ransomware operating in May 2023, it only accounted for less than a half percent of the total engagements in 2023. The group significantly increased its activity in Q1 2024, and there were more BlackSuit engagements in February 2024 alone than in all of 2023. BlackSuit operates as a private group without affiliates, targeting both Windows and Linux users and utilizing a double extortion method of stealing and encrypting sensitive data on a victim’s network.
BlackSuit: A Continuation of Royal Ransomware?
The BlackSuit ransomware payload has significant code overlap with Royal ransomware, and the Cybersecurity and Infrastructure Security Agency (CISA) and the FBI believe BlackSuit to likely be a rebranding or spinoff variant of Royal. While BlackSuit could be using the same developer or code with slight modifications, Arete also observed language used by BlackSuit in ransom negotiations identical to previous engagements with Royal, which lends to the assessment that the group might be a rebrand or offshoot. Regardless, BlackSuit’s emergence demonstrates that although names may change, threat actors will find ways to adapt and evolve their operations.
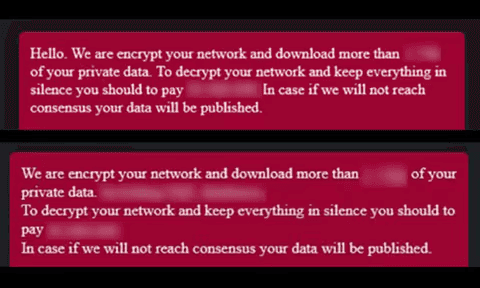
Figure 1. Language from two separate BlackSuit TOR chats (Source: Arete)
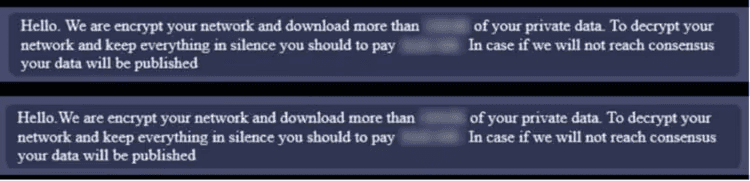
Figure 2. Identical language from two separate Royal TOR chats (Source: Arete)
Technical Analysis
Malware analysis revealed that BlackSuit ransomware:
Supports multiple command-line arguments.
Encrypts files on the system and mounted shares.
Adds the following extension to encrypted files: .blacksuit (e.g., file.docx.blacksuit).
Creates a ransom note with the following filename: readme.blacksuit.txt.
Self-identifies the group as BlackSuit in the ransom note.
References a data leak site in the ransom note that, when accessed, self-identifies the group as BlackSuit.
Kills a list of processes and services.
Maintains a list of whitelisted files and directories to make sure it will not render the system unusable, preventing recovery when running a decryptor.
Attempts to prevent system recovery by deleting the system’s volume shadow copies.
Creates the following mutex during execution: WLm87eV1oNRx6P3E4Cy9.
Execution Pattern/Arguments
BlackSuit ransomware needs command line arguments to execute and encrypt files in the system. Command line arguments supported:
Command line argument | Description |
|---|---|
-id [32-byte characters] | Ransomware ID |
-size | Invoked with drag and drop |
-ep | Number that represents the percentage of the file that will be encrypted |
-path [target_directory_path] | Used to specify a target directory to encrypt |
-localonly | Encrypt only the local system |
-networkonly | Encrypt only shared volumes/directory |
-aavm | Encrypt all files |
The ransomware will not execute in the system without the “–id” argument followed by a 32-character value that is unique in each engagement and present in the ransom note TOR URL. Portion of the data in the ransom note that contains the ID:
All your files will be decrypted, your data will be reset, your systems will stay in safe. Contact us through TOR browser using the link: http://c7jpc6h2ccrdwmhofuij7kz6sr2fg2ndtbvvqy4fse23cf7m2e5hvqid[.]onion/?id=[32-characters] | ||
|---|---|---|
Execution of ransomware to encrypt files:
blacksuit.exe -id [32-characters] | ||
|---|---|---|
The ransomware developer coded the logic to allow configuration of the 32-character value in the command line during execution. This same victim-specific 32-character string value is then added to the ransom note URL used for negotiations. Due to this implementation in the ransomware code, threat researchers can execute the ransomware without knowing the 32-character string value, as any value of this type can be used to execute the malicious code. In analyzing Royal ransomware samples, Arete found a similarity in that any 32-character value can be supplied to execute the ransomware, and the value is also added to the ransom note TOR chat URL.
Example of how the ransom note content looks with a randomly supplied string (e.g., blacksuit.exe -id 7777777777777777777777777777777):
All your files will be decrypted, your data will be reset, your systems will stay in safe. Contact us through TOR browser using the link: http://c7jpc6h2ccrdwmhofuij7kz6sr2fg2ndtbvvqy4fse23cf7m2e5hvqid[.]onion/?id=77777777777777777777777777777777777777 | ||
|---|---|---|
Obfuscated Files or Information: Software Packing
Most of the strings in the ransomware are encoded. The encoded strings are hardcoded and decoded at runtime. Every encoded string has its own decoding loop:
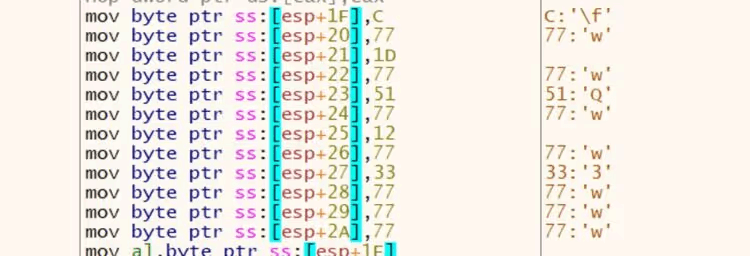
Figure 3. Encoded strings hardcoded
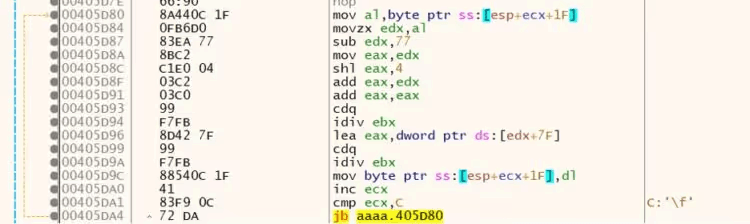
Figure 4. String decoding loop
Some relevant strings decoded in memory:
Global\\\WLm87eV1oNRx6P3E4Cy9 | -ep |
Obfuscated Files or Information: Dynamic API Resolution
To avoid static or other defensive analysis, the ransomware uses dynamic API resolution to conceal malware characteristics and functionality. The ransomware initially decrypts DLL names, then loads the APIs. Hardcoded encoded DLL names are shown below:
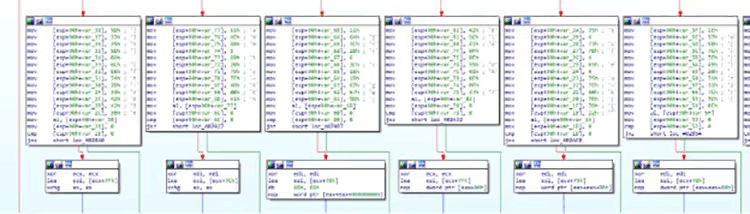
Figure 5. Encoded DLL names
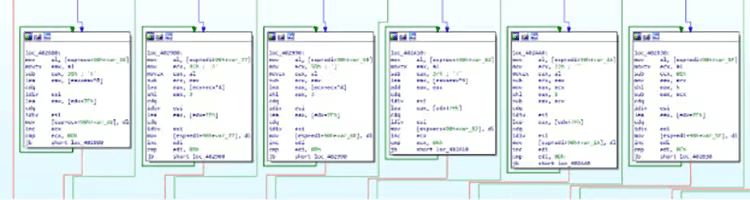
Figure 6. DLL name decoding loop
DLL names decoded at runtime:
shell32.dll | rstrtmgr.dll |
Stop Services and Processes
Before file encryption, the ransomware terminates a list of known running processes and services to encrypt as many files as possible. BlackSuit ransomware utilizes the Windows Restart Manager to terminate any process using files other than explorer.exe or a critical process.
Sequence of Windows Restart Manager APIs used by the ransomware:
RmStartSession | Starts the Restart Manager session. |
RmRegisterResources | Registers resources, in this case the targeted filename |
RmGetList | Determine which processes or services are using the registered resource (file) |
RmShutdown | Shuts down any identified process or service using the registered resource |
RmEndSession | Closes the Restart Manager session. |
The ransomware also uses Windows native CreateToolhelp32Snapshot, Process32FirstW, and Process32NextW APIs to enumerate processes in the system.
File and Directory Exclusions
The ransomware excludes system-related files and folders, ransomware-related files, and whitelisted extensions during encryption.
Excluded file extensions:
.com .ani .scr .drv .hta .rom .bin .msc .ps1 .shs .adv .msu .prf .bat .idx .mpa .cmd .msi .mod .ocx .ics .386 .sys .rtp .wpx .msp .cab .ldf .lnk .cur .nls .hlp .key .ico .exe .icns .lock .theme .diagpkg .diagcab .nomedia .diagcfg .msstyles .themepack .blacksuit .deskthemepack | ||
|---|---|---|
Excluded files and directories:
“msocache”, “intel”, “$recycle.bin”, “windows”, “windows.old”, “mozilla firefox”, “$WinREAgent”, “boot”, “google”, “perflogs”, “system volume information”, “appdata”, “tor browser”, “$windows.~ws”, “application data”, “$windows.~bt”, “mozilla”, “readme.blacksuit.txt” | ||
|---|---|---|
Inhibit System Recovery
Windows operating systems contain features that can help fix corrupted system files, including shadow copies, which are backups of files created by the Volume Shadow Copy Service (VSS). By deleting shadow copies, the ransomware can prevent victims from restoring files from backups, making it more difficult for them to recover their data without paying the ransom.
With the CreateProcessW function, the ransomware deletes volume shadow copies before file encryption by executing the following command:
cmd.exe /c vssadmin delete shadows /all /quiet | ||
|---|---|---|
Code in the ransomware showing this operation (the EAX register contains the kernel32.CreateProcessW address):
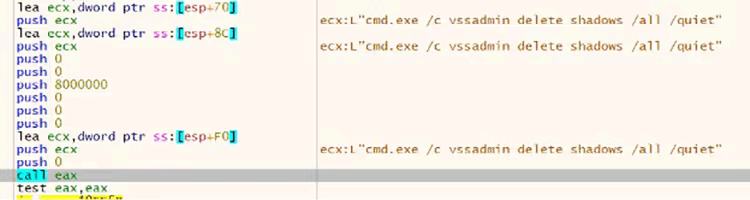
Figure 7. Create process call to delete volume shadow copies
System Network Connections Discovery
BlackSuit ransomware can enumerate network-mounted shares by scanning the network interfaces.
Data Encrypted for Impact
The ransomware initially finds available drives and loads the files one by one using the Windows API FindFirstFileW and FindNextFileW. It then uses OpenSSL AES keys to encrypt the files and adds the extension .blacksuit to the encrypted file name.
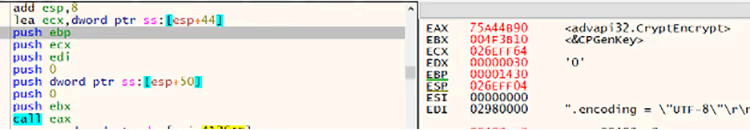
Figure 8. Windows native CryptEncrypt API call to encrypt the data
Public key:
—–BEGIN RSA PUBLIC KEY—– MIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEA+O9FGkh466oxay/9u//rycLpGqFwcUSQIy0d27cnpRqq1W4De/boeoJC/HJqkr3WaEqr2JHgjSQcMimTxy8d3NLJT7M3uTVaxXD3Bck83ns5S/WhiF5tQGHtAGetGv8gXYSq/bm6HAlWBMBaOvv4of7ov7/cTAl1pwwgnaYzws4q6C9Q5zwmcU7DFcOohyVqBu/2svUlvtfMJGzYVeUJSUF6E2NMhClxddDLr32wCuoZ567uMBLQB2e5DUTkplR1OdVeyWyxhAXJSjQ5T9LpwuUHNm89nuo25slwlUx2m5a2k6wn2husXhXj+NRN/c2F3zh2qkcgs318XY8es1r3UgIBdCYMMGKsZ0DxKJZ1fq4nU93c+aP0qFBawmYhgIZq6MBYrG23LGbJPZvcC8pkyJrT51ygthCVPtpThqlthdqzqnV+7gPaf/XRwHeLkqawPhe1omd9m7gSuFwIREUe2MW1qZ7p3Nzhf8ZF4/YN7PSN1m6Ve5HS1MgnR9cbj655Jt3lqgW6rillrP+DbdrnjYo7yz2CsxSL3vKVtzcDzsbEFPkAFDyfSrYVxMYCEUJ8jHlctrNo+UiuZTT0O9dbwoGfCSrg8w+V0h8pYaiGnVwwGGkQbLgBAvz+iOOyElbZDLEPJxZ1+ipYzADufQSh8RHh/nXpWirlzQNH7oqrA0fUCAwEAAQ== —–END RSA PUBLIC KEY—– | ||
|---|---|---|
The ransomware encrypts files, adds the .blacksuit extension at the end of the encrypted files, and adds the following bytes at the end of the file (“??” represents variable bytes):
00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ?? 00 00 00 ?? 00 00 00 | ||
|---|---|---|
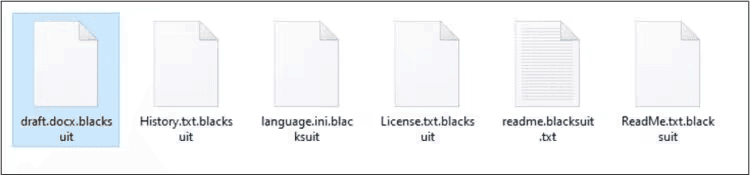
Figure 9. “.blacksuit” extension added to the encrypted files
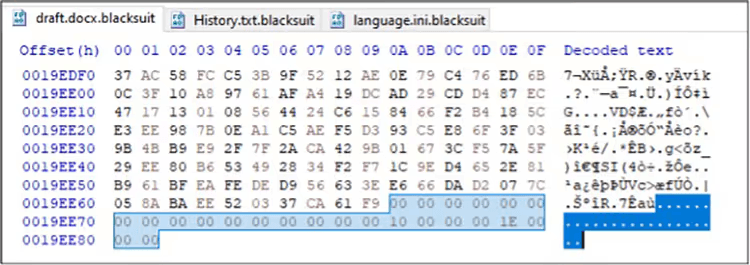
Figure 10. Padding bytes in encrypted files
Upon successful execution, the ransomware creates ransom notes with the file name readme.blacksuit.txt.
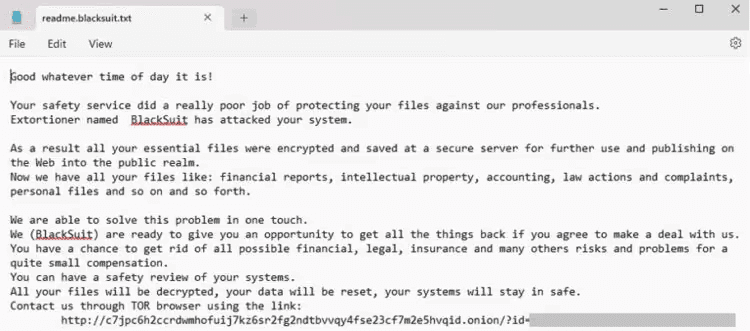
Figure 11. Screenshot of BlackSuit ransom note
Modify Registry
The ransomware did not perform any registry key modification.
Mutex
The mutex is the fundamental tool for managing shared resources between multiple threads or processes. Typically, ransomware uses a mutex to avoid reinfecting the victim system and causing multiple layers of encryption. The ransomware creates the following mutex value: “WLm87eV1oNRx6P3E4Cy9”.
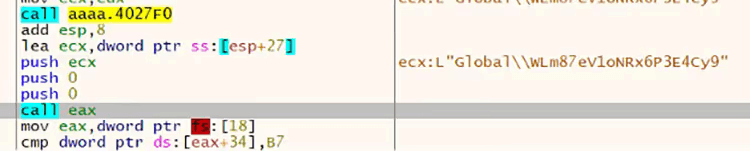
Figure 12. Screenshot of the mutex value created while debugging the ransomware
Network Activity
The ransomware did not try to communicate with a remote server other than encrypting data from mounted shares.
Indicators of Compromise
Indicator | Type | Context |
|---|---|---|
f1684fb118d4d8fc56653fcc49e12a659b64c4459ba037fa94f21783235cc6ba | SHA256 hash | BlackSuit ransomware |
C:\readme.blacksuit.txt | File path | BlackSuit ransom note |
.blacksuit | Extension | Encrypted files extension |
vssadmin delete shadows /all /quiet | Process | Volume Shadow Copy deletion |
WLm87eV1oNRx6P3E4Cy9 | Mutex | Mutex value object created by the BlackSuit ransomware |
Any 32-character string | Password | Command line argument needed to properly execute the ransomware. The ransomware developer doesn’t validate it |
c7jpc6h2ccrdwmhofuij7kz6sr2fg2ndtbvvqy4fse23cf7m2e5hvqid [.]onion | URL | TA data leak site (DLS) |
Data Leak Site
The ransom note contains a data leak site (DLS) that displayed the following page, self-identifying the group as BlackSuit:
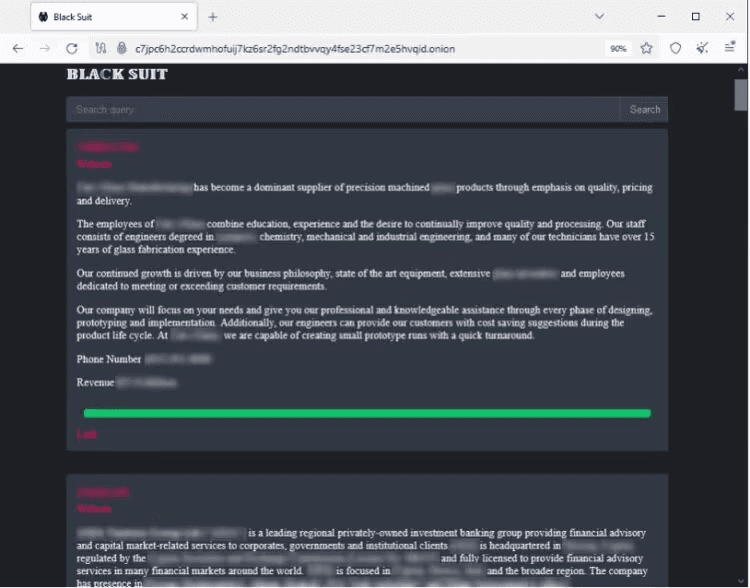
Figure 13. TOR DLS: c7jpc6h2ccrdwmhofuij7kz6sr2fg2ndtbvvqy4fse23cf7m2e5hvqid[.]onion
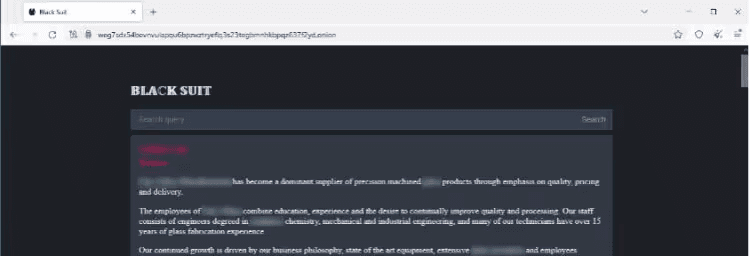
Figure 14. TOR DLS: weg7sdx54bevnvulapqu6bpzwztryeflq3s23tegbmnhkbpqz637f2yd[.]onion
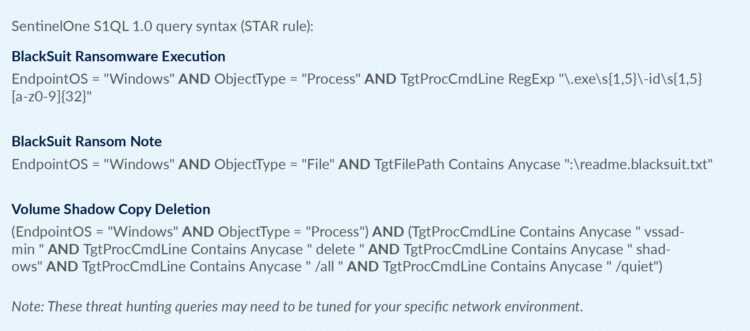
Detection Mechanisms
Custom Detections and Blocking with Arete’s Arsinal
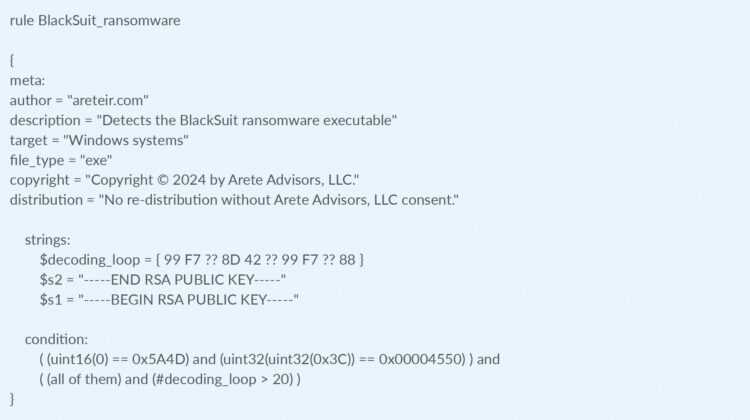
Yara
Recommended Mitigations
Utilize an endpoint detection and response (EDR) solution with the capability to halt detected processes and isolate systems on the network based on identified conditions.
Block any known attacker C2s in the firewall.
Implement multi-factor authentication on RDP and VPN to restrict access to critical network resources.
Eliminate unnecessary RDP ports exposed to the internet.
Block a high number of SMB connection attempts from one system to others in the network over a short period of time.
Perform periodic dark web monitoring to verify if data is available for sale on the black market.
Perform penetration tests.
Periodically patch systems and update tools.
Monitor connections to the network from suspicious locations.
Monitor downloads and uploads of files to file-sharing services outside standard work hours.
Monitor file uploads from domain controllers to the internet.
Monitor network scans from uncommon servers (e.g., RDP server).
Organizations can find the full list of US government recommended ransomware prevention and mitigation guidance here: https://www.cisa.gov/stopransomware/ransomware-guide.
Arete provides data-driven cybersecurity solutions to transform your response to emerging cyber threats. Learn more.
References
Back to Blog Posts
Article
Ransomware Trends & Data Insights: February 2026
After a slight lull in January, Akira and Qilin returned to dominating ransomware activity in February, collectively accounting for almost half of all engagements that month. The rest of the threat landscape remained relatively diverse, with a mix of persistent threats like INC and PLAY, older groups like Cl0p and LockBit, and newer groups like BravoX and Payouts King. Given current trends, the first quarter of 2026 will likely remain relatively predictable, with the top groups from the second half of 2025 continuing to operate at fairly consistent levels month to month.
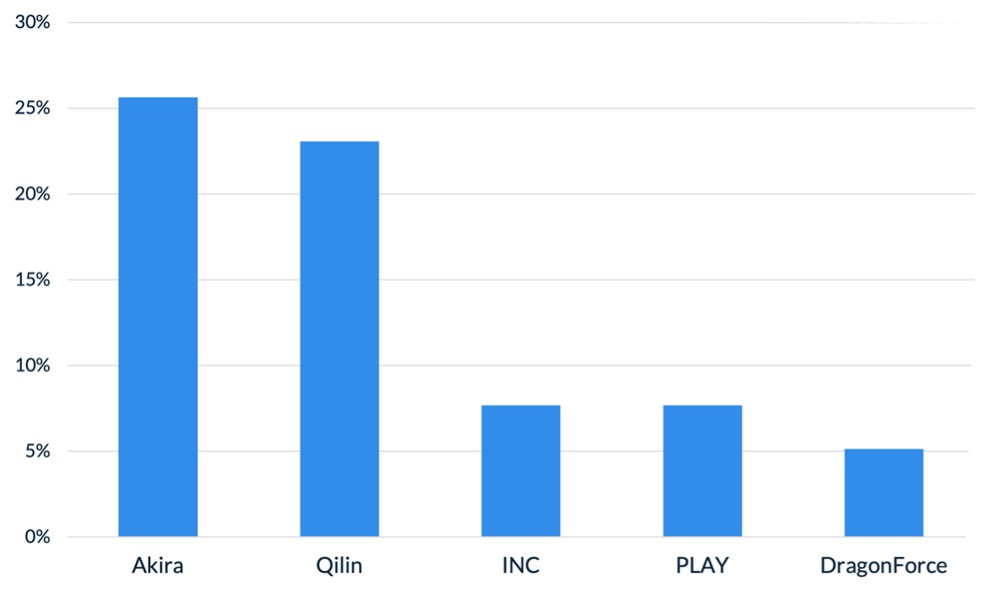
Figure 1. Activity from the top 5 threat groups in February 2026
Throughout the month of February, analysts at Arete identified several trends behind the threat actors perpetrating cybercrime activities:
In February, Arete observed Qilin actively targeting WatchGuard Firebox devices, especially those vulnerable to CVE-2025-14733, to gain initial access to victim environments. CVE-2025-14733 is a critical vulnerability in WatchGuard Fireware OS that allows a remote, unauthenticated threat actor to execute arbitrary code. In addition to upgrading WatchGuard devices to the latest Firebox OS version, which patches the bug, administrators are urged to rotate all shared secrets on affected devices that may have been compromised and may be used in future campaigns.
Reports from February suggest that threat actors are increasingly exploring AI-enabled tools and services to scale malicious activities, demonstrating how generative AI is being integrated into both espionage and financially motivated threat operations. The Google Threat Intelligence Group indicated that state-backed threat actors are leveraging Google’s Gemini AI as a force multiplier to support all stages of the cyberattack lifecycle, from reconnaissance to post-compromise operations. Separate reporting from Amazon Threat Intelligence identified a threat actor leveraging commercially available generative AI services to conduct a large-scale campaign against FortiGate firewalls, gaining access through weak or reused credentials protected only by single-factor authentication.
The Interlock ransomware group recently introduced a custom process-termination utility called “Hotta Killer,” designed to disable endpoint detection and response solutions during active intrusions. This tool exploits a zero-day vulnerability (CVE-2025-61155) in a gaming anti-cheat driver, marking a significant adaptation in the group’s operations against security tools like FortiEDR. Arete is actively monitoring this activity, which highlights the growing trend of Bring Your Own Vulnerable Driver (BYOVD) attacks, in which threat actors exploit legitimate, signed drivers to bypass and disable endpoint security controls.
Sources
Arete Internal
Article
ClickFix Campaign Delivers Custom RAT
Security researchers identified a sophisticated evolution of the ClickFix campaign that aims to compromise legitimate websites before delivering a five-stage malware chain, culminating in the deployment of MIMICRAT. MIMICRAT is a custom remote access trojan (RAT) written in the C/C++ programming language that offers various capabilities early in the attack lifecycle. The attack begins with victims visiting compromised websites, where JavaScript plugins load a fake Cloudflare verification that tricks users into executing a malicious PowerShell script, further displaying the prominence and effectiveness of ClickFix and its user interaction techniques.
Not Your Average RAT
MIMICRAT displays above-average defense evasion and sophistication, including:
A five-stage PowerShell sequence beginning with Event Tracing for Windows and Anti-Malware Scan Interface bypasses, which are commonly used in red teaming for evading detection by EDR and AV toolsets.
The malware later uses a lightweight scripting language that is scripted into memory, allowing malicious actions without files that could easily be detected by an EDR tool.
MIMICRAT uses malleable Command and Control profiles, allowing for a constantly changing communication infrastructure.
The campaign uses legitimate compromised infrastructure, rather than attacker-owned tools, and is prepped to use 17 different languages, which increases global reach and defense evasion.
Analyst Comments
The ClickFix social engineering technique remains an effective means for threat actors to obtain compromised credentials and initial access to victim environments, enabling them to deploy first-stage malware. Coupled with the sophisticated MIMICRAT RAT, the effectiveness of this campaign could increase. Arete will continue monitoring for changes to the ClickFix techniques, the deployment of MIMICRAT in other campaigns, and other pertinent information relating to the ongoing campaign.
Sources
MIMICRAT: ClickFix Campaign Delivers Custom RAT via Compromised Legitimate Websites
Article
Threat Actors Leveraging Gemini AI for All Attack Stages
State-backed threat actors are leveraging Google’s Gemini AI as a force multiplier to support all stages of the cyberattack lifecycle, from reconnaissance to post-compromise operations. According to the Google Threat Intelligence Group (GTIG), threat actors linked to the People’s Republic of China (PRC), Iran, North Korea, and other unattributed groups have misused Gemini to accelerate target profiling, synthesize open-source intelligence, identify official email addresses, map organizational structures, generate tailored phishing lures, translate content, conduct vulnerability testing, support coding tasks, and troubleshoot malware development. Cybercriminals are increasingly exploring AI-enabled tools and services to scale malicious activities, including social engineering campaigns such as ClickFix, demonstrating how generative AI is being integrated into both espionage and financially motivated threat operations.
What’s Notable and Unique
Threat actors are leveraging Gemini beyond basic reconnaissance, using it to generate polished, culturally nuanced phishing lures and sustain convincing multi-turn social engineering conversations that minimize traditional red flags.
In addition, threat actors rely on Gemini for vulnerability research, malware debugging, code generation, command-and-control development, and technical troubleshooting, with PRC groups emphasizing automation and vulnerability analysis, Iranian actors focusing on social engineering and malware development, and North Korean actors prioritizing high-fidelity target profiling.
Beyond direct operational support, adversaries have abused public generative AI platforms to host deceptive ClickFix instructions, tricking users into pasting malicious commands that deliver macOS variants of ATOMIC Stealer.
AI is also being integrated directly into malware development workflows, as seen with CoinBait’s AI-assisted phishing kit capabilities and HonestCue’s use of the Gemini API to dynamically generate and execute in-memory C# payloads.
Underground forums show strong demand for AI-powered offensive tools, with offerings like Xanthorox falsely marketed as custom AI but actually built on third-party commercial models integrated through open-source frameworks such as Crush, Hexstrike AI, LibreChat-AI, and Open WebUI, including Gemini.
Analyst Comments
The increasing misuse of generative AI platforms like Gemini highlights a rapidly evolving threat landscape in which state-backed and financially motivated actors leverage AI as a force multiplier for reconnaissance, phishing, malware development, and post-compromise operations. At the same time, large-scale model extraction attempts and API abuse demonstrate emerging risks to AI service integrity, intellectual property, and the broader AI-as-a-Service ecosystem. While these developments underscore the scalability and sophistication of AI-enabled threats, continued enforcement actions, strengthened safeguards, and proactive security testing by providers reflect ongoing efforts to mitigate abuse and adapt defenses in response to increasingly AI-driven adversaries.
Sources
GTIG AI Threat Tracker: Distillation, Experimentation, and (Continued) Integration of AI for Adversarial Use
Article
2025 VMware ESXi Vulnerability Exploited by Ransomware Groups
Ransomware groups are actively exploiting CVE‑2025‑22225, a VMware ESXi arbitrary write vulnerability that allows attackers to escape the VMX sandbox and gain kernel‑level access to the hypervisor. Although VMware (Broadcom) patched this flaw in March 2025, threat actors had already exploited it in the wild, and CISA recently confirmed that threat actors are exploiting CVE‑2025‑22225 in active campaigns.
What’s Notable and Unique
Chinese‑speaking threat actors abused this vulnerability at least a year before disclosure, via a compromised SonicWall VPN chain.
Threat researchers have observed sophisticated exploit toolkits, possibly developed well before public disclosure, that chain this bug with others to achieve full VM escape. Evidence points to targeted activity, including exploitation via compromised VPN appliances and automated orchestrators.
Attackers with VMX level privileges can trigger a kernel write, break out of the sandbox, and compromise the ESXi host. Intrusions observed in December 2025 showed lateral movement, domain admin abuse, firewall rule manipulation, and staging of data for exfiltration.
CISA has now added CVE-2025-22225 to its Known Exploited Vulnerabilities (KEV) catalog, underscoring ongoing use by ransomware attackers.
Analyst Comments
Compromise of ESXi hypervisors significantly amplifies operational impact, allowing access to and potential encryption of dozens of VMs simultaneously. Organizations running ESXi 7.x and 8.x remain at high risk if patches and mitigations have not been applied. Therefore, clients are recommended to apply VMware patches from VMSA‑2025‑0004 across all ESXi, Workstation, and Fusion deployments. Enterprises are advised to assess their setups in order to reduce risk, as protecting publicly accessible management interfaces is a fundamental security best practice.
Sources
CVE-2025-22225 in VMware ESXi now used in active ransomware attacks
The Great VM Escape: ESXi Exploitation in the Wild
VMSA-205-004: VMware ESXi, Workstation, and Fusion updates address multiple vulnerabilities (CVE-205-22224, CVE-2025-22225, CVE-2025-22226)