Article
Ransomware Decryptors for a (varying) fee
Arete Analysis

Ransomware attacks wreak havoc on business operations. Destroying recovery options, instilling fear and panic, and most often creating high levels of stress for IT staff, owners, and operators. A simple, but often costly fix is to just pay the Threat Actor for the decryption utility. While making a payment to an anonymous entity is a highly debated topic, let us assume, for the purposes of this article, that the payment is the only option other than closing your business. Please note, Arete is not advocating to pay ransoms; the choice is entirely a business decision to pursue. This article is intended to provide insight into the various types of decryptors the threat groups provide to unlock your files. We will discuss specific decryptors for some of the more popular variants as well as address subtle nuances between the decryptors.
Full Disk Encryption
Ransomware variants like THT, Mamba, or MCrypt use native or opensource encryption software to encrypt the entire hard drive of the system. Once the TA gains access to the system with administrator privileges, the TA will use a tool like Bestcrypt, DiskCryptor or even Windows Bitlocker to encrypt the full disk. Once encryption is complete, the system reboots and the victims are locked out.
Communication preference: Email usually protonmail, firemail.cc, or cock.li domains
Average ransom payment: $36,000 – $55,000
Preferred currency: Bitcoin (BTC)
Decryptor received: 100% of the time. TA will provide passwords per system for access
Watch out: MCrypt will hold volumes hostage and “re-extort” victims into making multiple payments. During the initial negotiation, the TA will not indicate multiple drives are encrypted. Instead they will negotiate a single amount for initial access to the Operating System; essentially allowing access into Windows. Once access to Windows is regained, victims often surprised to find their “data” partitions are encrypted causing the victim to return to the negotiation table to once again shell out more money to unlock their information.
Notes: After gaining access, the open source encryption tool still needs to be removed otherwise after reboot, the data storage will be locked again.
System Specific Encryption
Ransomware variants like Phobos, Dharma or CryLock are file level encryption. The TA gains access to the system, copies specific encryption executables onto the systems then runs the executables to encrypt the files. The results are files with a new extension appended to the old file name. Sometimes it’s a random sequence of numbers and letters (e.g. *.nocv) or a specific tag (e.g. *[CryLockDecrypt@****.com][1].[ID-*****- COM]). System specific encryption generates a unique key per encrypted system. The ransom note or the file extension may indicate an “ID” that would be different on each system.

CryLock Scanner & Decryptor
Communication preference: Email usually aol.com, protonmail.com, or cock.li domains
Average ransom payment: $27,000 – $500,000
Preferred currency: Bitcoin (BTC)
Decryptor Received: 95% of the time. Certain variants of Phobos and Dharma will attempt to re-extort a second payment if a large discount is negotiated.
Watch out: Phobos, Dharma, and CryLock are a two-step process. The TA will first send a “scanner” tool that needs to be run on every infected system. The scanner will look for the public keys used to encrypt the files, then write that information to a corresponding .txt or .ini file. Those corresponding files need to be sent to the TA in order to generate a decryptor. The TA in return will send the decryptors. The two-step process adds significant overhead due to the running of multiple tools on the infected system as well as the delay with communicating via email. On average after making a payment for the decryptor, clients are who are infected with Phobos are down for approximately 11 days whereas clients who are infected with Dharma experience downtime of about 7.75 days. The high number of days can be attributed to the two-step process and multiple email communications.
Notes: Negotiating with the Phobos and Dharma group can be tricky. These variants are Ransom-as-a-Service (RaaS) model so you’re not dealing with the same core group of people as you would with variants like Ryuk (or now Conti). Negotiating with RaaS groups can also create confusion and complexities with a different operator responding to each email. The groups who deploy these variants also look for exploiting publicly accessible Remote Desktop Protocol (RDP). Disable external access to RDP to lessen the chance of being infected by this variant.
System Specific Encryption with a Universal Option
Ransomware variants like Sodinokibi are file level encryption with a unique ID per system. Once the TA gains access to the network, they release their Sodinokibi ransomware throughout the environment. The systems are infected with a unique randomly generated file extension per system. Their ransom notes are usually within a text file and explain what happened, including if any data was exfiltrated. The group is very organized and can often share information about their victim’s networks including domain information, infected systems, and any stolen data.

Sodinokibi Decryptor
Communication preference: TOR Website via chat room. The ransom note contains a link to the TOR site as well as a unique key to gain access to a private chat room where the negotiations occur.
Average ransom payment: $170,000
Preferred currency: Monero (XMR)
Decryptor received: 100% of the time. Sodin offers a general decryptor which requires the victim to collect the file extensions from all of their infected systems. This can be very tedious once the payment is made, the victim can input any number of file extensions into the input box on the TOR site to generate a decryptor. Sodin will keep that private room open for 30 days after payment allowing victims to return if they find any extensions not previously found. A lesser known secret with Sodin, if you ask nicely for a universal decryptor, the operator may create the decryptor for you; providing a single decryptor that can be used across your network. The universal decryptor certainly saves a lot of time with decrypting files and minimizing the number of times having to launch the TOR browser.
Watch out: Earlier this year, Sodin changed their code base for their encryption payloads causing instability on certain Windows Operating Systems within the master boot files. Using certain security tools after a Sodin outbreak can cause systems to hang during reboot. Sodin encryption is one of the more aggressive encryptions.
Be sure to create a snapshot or backup the files prior to installing any new software or performing live forensics on critical systems.
Notes: Sodin has made headlines throughout 2020 for following Maze with exfiltrating data as well as being the first ransomware group to only accept Monero for payments.
System Specific Encryption with a Universal Option
Ransomware variants like Sodinokibi are file level encryption with a unique ID per system. Once the TA gains access to the network, they release their Sodinokibi ransomware throughout the environment. The systems are infected with a unique randomly generated file extension per system. Their ransom notes are usually within a text file and explain what happened, including if any data was exfiltrated. The group is very organized and can often share information about their victim’s networks including domain information, infected systems, and any stolen data.
Sodinokibi Decryptor
Communication preference: TOR Website via chat room. The ransom note contains a link to the TOR site as well as a unique key to gain access to a private chat room where the negotiations occur.
Average ransom payment: $170,000
Preferred currency: Monero (XMR)
Decryptor received: 100% of the time. Sodin offers a general decryptor which requires the victim to collect the file extensions from all of their infected systems. This can be very tedious once the payment is made, the victim can input any number of file extensions into the input box on the TOR site to generate a decryptor. Sodin will keep that private room open for 30 days after payment allowing victims to return if they find any extensions not previously found. A lesser known secret with Sodin, if you ask nicely for a universal decryptor, the operator may create the decryptor for you; providing a single decryptor that can be used across your network. The universal decryptor certainly saves a lot of time with decrypting files and minimizing the number of times having to launch the TOR browser.
Watch out: Earlier this year, Sodin changed their code base for their encryption payloads causing instability on certain Windows Operating Systems within the master boot files. Using certain security tools after a Sodin outbreak can cause systems to hang during reboot. Sodin encryption is one of the more aggressive encryptions.
Be sure to create a snapshot or backup the files prior to installing any new software or performing live forensics on critical systems.
Notes: Sodin has made headlines throughout 2020 for following Maze with exfiltrating data as well as being the first ransomware group to only accept Monero for payments. eir.co
Universal Encryption
Ransomware variants like Ryuk, WastedLocker, and Dopplepaymer are also file level encryption. These groups will gain access to the network and perform reconnaissance to identify the victim, understand their business, identify critical systems, and delete backups to force their victims into making a payment. The groups can have access to the network for a few hours or upwards of over a month. Ryuk is commonly associated with precursor trojans such as Trickbot and Emotet. Arete has observed Ryuk deployed as quickly as 6 hours after a Trickbot infection. Ryuk infections result with *.ryk appended to the file name. Comparatively, the deployment of WastedLocker is much more calculated with the TA staying on the network for an average of 2 weeks from initial infection to ransomware deployment. Wasted infections result with *.abcwasted appended to the file name where “abc” is a 3 letter abbreviation relating directly to the victims name.
WastedLocker Decryptor
Communication preference: Email usually protonmail.com domains or TOR Website
Average ransom payment: Ryuk $598,000; WastedLocker $2,400,000; Dopplepaymer $304,000
Preferred currency: Bitcoin (BTC)
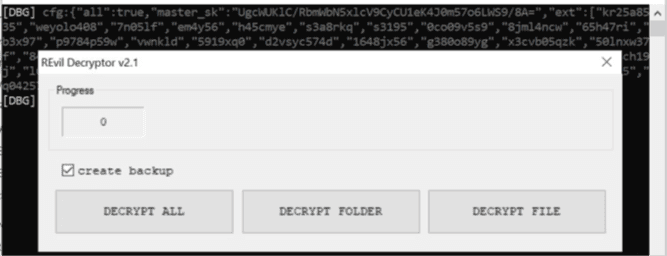
Decryptor received: 100% of the time. The decryptor received is universal. It is typically a 32-bit executable that will work on any windows OS version. While these groups are known for a high ransom price, their decryptor is probably the simplest to run.
Watch out: WastedLocker is extremely difficult to negotiate. In fact, if negotiation is attempted, they may threaten to increase the ransom by approximately 5% of the ransom per day until it is paid. They are also very slow to respond to email and even post their business hours of UTC 5am- 8am and 5pm-8pm.
Notes: Dopplepaymer has been linked to gaining access to large environments and deploying cryptomining malware before launching their ransomware attack.
Pro Tips to Prevent Ransomware

Attacks
Implement Endpoint, Detection, and Response software such as SentinelOne to monitor the computer systems in use by your organization. SentinelOne uses Artificial Intelligence technology to detect malicious actions and prevent them before they can severely affect the endpoint.
Leverage a Security Operations Center (“SOC”) to monitor computer systems 24 hours a day by 7 days a week. The SOC can instantly respond to triage and mitigate any alerts while keeping your IT personnel focused on maintain business productivity.
Enable Multi-Factor Authentication (“MFA”) on remote access technologies such as VPN and Email.
Use complex passwords with a minimum of 16 alphanumeric characters (non- dictionary words).
Don’t reuse passwords.
Encourage discussion about cybersecurity within the workplace including establishing end user awareness training.
Ensure backups are current, air gapped from the production network, and viable.
Back to Blog Posts
Article
Arete's 2026 Q1 Crimeware Report
Harness Arete’s unique data and expertise on extortion and ransomware to inform your response to the evolving threat landscape.
Article
CMS Vulnerability Leads to ClickFix Campaign
Threat actors compromised at least 700 education and technology websites in a recent ClickFix campaign by exploiting a critical SQL injection flaw (CVE-2026-26980) in the Ghost content management system (CMS). Adversaries combined the vulnerability with the ClickFix social engineering tactic to steal admin keys and inject a malicious JavaScript that delivers a fake Cloudflare or CAPTCHA verification pop-up, tricking victims into copying and pasting a malicious command into their systems.
What’s Notable and Unique
Rather than targeting the end user first, this campaign is unique in its initial exploitation of the system, followed by social engineering attempts. This hybrid attack style is likely being leveraged to bypass traditional defenses.
This recent campaign also highlights how trusted web properties can be weaponized at scale and coupled with unpatched CMS vulnerabilities. Rather than using the CMS compromise to perpetrate a single attack, threat actors turned it into a supply-chain attack that ultimately affected over 700 trusted websites.
Analyst Comments
As network defenders and their tools enhance threat detection capabilities, adversaries increasingly seek methods to bypass these defenses. By combining vulnerability exploitation, social engineering techniques, and staging for ancillary attacks, this campaign successfully bypassed traditional defenses and inflicted significant impact. Defending against hybrid cyberattacks requires comprehensive security controls beyond simply patching vulnerabilities. Organizations should focus on limiting movement within the environment, detecting abuse of trusted applications, and preventing end-user manipulation.
Sources
700+ education and tech websites hijacked in huge ClickFix malware campaign
Under the engineering hood: Why Malwarebytes chose WordPress as its CMS
Think before you Click(Fix): Analyzing the ClickFix social engineering technique
Ghost CMS Vulnerability Exploited to Infect 700 Sites With ClickFix Malware
Article
Threat Actors Leverage Fake JPEG Files for Initial Access
In a recent campaign, researchers observed threat actors using fake JPEG image files as a delivery mechanism to initiate the deployment of additional malicious components. The false JPEG files are typically distributed via phishing emails or other social engineering-based lures, and are actually PowerShell-based malware that deploys a trojanized version of ConnectWise ScreenConnect to establish and maintain persistence in the compromised environment.
What’s Notable and Unique
This campaign leverages JPEG images as the initial lure, where the images are not merely decoys but part of the infection workflow. Victims are typically led to download or open an image that triggers hidden execution logic or redirects them to a payload-delivery sequence that initiates later stages of the intrusion chain.
The attack chain is designed to blend into legitimate environments, making detection more difficult. Execution typically relies on scripted or native Windows components, often including PowerShell or other living-off-the-land binaries, enabling fileless or near-fileless execution and reducing forensic artifacts on disk.
The multistage design ensures that the initial JPEG does not directly contain the full payload but instead triggers retrieval or decryption steps that progressively assemble the final malicious components in memory.
Analyst Comments
This campaign illustrates how threat actors continue to blur the line between legitimate file handling and malicious execution chains, indicating potential overlap with remote management or administrative tooling. The use of JPEG-based staging combined with script-based execution reflects a broader evolution toward a stealth-first intrusion design, in which file formats serve as triggers rather than payload containers.
Sources
OPERATION SILENTCANVAS : JPEG BASED MULTISTAGE POWERSHELL INTRUSION
Podcast
Cyber Risk and Insurance for Law Firms
In this episode of Bytes of Insight, host Vinny Sakore is joined by Laura Zaroski, Managing Director of the Law Firms Group at Gallagher, as they discuss the evolution of cyber risk for law firms. Tune in for firsthand insights on how to select the right cyber policy, the incident response process, and the nuances of ransom payments and sensitive data.



