Article
ALPHV/BlackCat Disruption: Operations Resume
Cyber Threats
Combating Ransomware
Threat Actors

Despite law enforcement’s disruption to ALPHV/BlackCat’s infrastructure in December 2023, the group has since resumed operations. As Arete previously reported, the Federal Bureau of Investigation (FBI) seized the ransomware group’s data leak site (DLS) on December 19, 2023, and obtained victim-specific decryption keys for over 500 ALPHV victims. Before this, the TOR chat sites used to communicate with victims also went offline in early December, causing some affiliates to resort to alternative means of communication, such as Tox chats and email correspondence, to continue efforts to extort money from their victims.
Interestingly, in January 2023 when the FBI infiltrated Hive ransomware’s operations, they gained access to the group’s servers and decryption keys and successfully shut down Hive’s data leak site, negotiation site, and web panels. This ultimately forced the group to cease operating under the Hive brand after the takedown. It remains to be seen whether ALPHV will suffer a similar fate.
What has happened from December 2023 through January 2024?
Unlike the Hive breach, the impact of this recent law enforcement operation against ALPHV seems to have only temporarily disrupted their infrastructure. Arete observed that the group is resuming normal operations.
After the FBI posted a notice on ALPHV’s data leak site stating it had been seized, the ransomware group briefly regained control of the URL and posted that the site had been “unseized.” The group reportedly retained access to the keys used to operate the DLS and used that access to point visitors to a new DLS that appears fully controlled by ALPHV. ALPHV claimed that the FBI only impacted a portion of its operations.
ALPHV began circulating a new URL for their data leak site shortly after the FBI seizure and has posted new victims since December 13, 2023. Although most of the victim content before law enforcement’s action is no longer on their dark web page, the group has continued to add to the new leak site, with over 20 victims posted as of January 16, 2024. The number of victims on the site continues to fluctuate as ALPHV negotiates with victims.
In response to the actions of law enforcement, the group posted new rules, allowing affiliates to target any organization outside of the Commonwealth of Independent States (CIS), including hospitals and critical infrastructure. The new rules also stated that discounts on ransom demands would no longer be given.
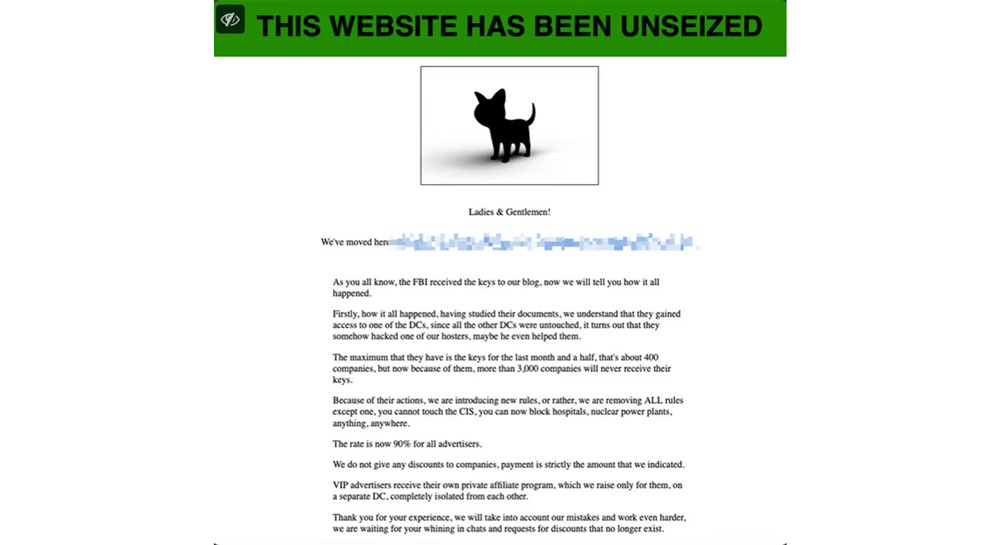
Figure 1 Image of Updated ALPHV rules. Image Source
Since the FBI announcement, Arete observed ALPHV continuing standard ransom communications with its victims contrary to their claims to have changed the rules for affiliates. In late December, the group began using their private TOR chats again to communicate with victims. The new ransom notes include language and naming conventions different from the ones sent to victims before the law enforcement operation. However, the private TOR chats remain the same, displaying a timer and listing a discount price and full price, along with Bitcoin and Monero wallets showing an additional 15% added if payment is in Bitcoin.
Image of ALPHV’s New Data Leak Site
Arete’s Observations
Although the FBI’s operations against ALPHV in December 2023 caused noticeable disruptions to the ransomware group’s ability to operate, law enforcement appeared unable to permanently shut down ALPHV’s infrastructure or operational capabilities, unlike prior law enforcement actions against groups like Hive or REvil. ALPHV appears to be trying to resume its activities in the same manner as before the disruption, reestablishing its data leak site and communicating with new victims on the group’s private TOR sites.
The group’s threats and newly imposed rules appear aimed at projecting strength in the face of the FBI breach rather than representing authentic internal policy changes that affiliates genuinely comply with. Since ALPHV made its public statement in December, Arete observed the group continuing to conduct extortion communications as they did before the disruption, with affiliates still offering discounted prices and showing a willingness to negotiate. While it is too soon to know if there will be a corresponding uptick in attacks against hospitals and critical infrastructure, Arete assesses this would be counterproductive if the group intends to continue operating under the ALPHV/BlackCat brand. The group was already known for attacking the healthcare industry, and future attacks against high-profile targets would lead to even greater attention from law enforcement.
Although ALPHV has been trying to salvage its reputation and resume operations, it is too early to assess whether the group will be able to continue operating as it did prior to law enforcement’s intervention. The knowledge that law enforcement is actively targeting ALPHV will likely deter some affiliates from continuing to work with the group, potentially leading some affiliates to accept active recruitment offers from other Ransomware-as-a-Service (RaaS) groups like LockBit. Even as ALPHV continues to operate, the group may eventually rebrand itself under a different name to complicate further action by law enforcement.
Sources
Back to Blog Posts
Article
Ransomware Trends & Data Insights: April 2026
The threat landscape has remained relatively predictable thus far in 2026. In April, Qilin dethroned Akira as the most active threat group for the month. Akira, who had been the top ransomware threat each month since July 2025, was still only slightly behind Qilin and had roughly the same activity level as in March. INC Ransom and DragonForce also remained active threats in April, with those four ransomware groups accounting for half of all ransomware and extortion activity observed by Arete.
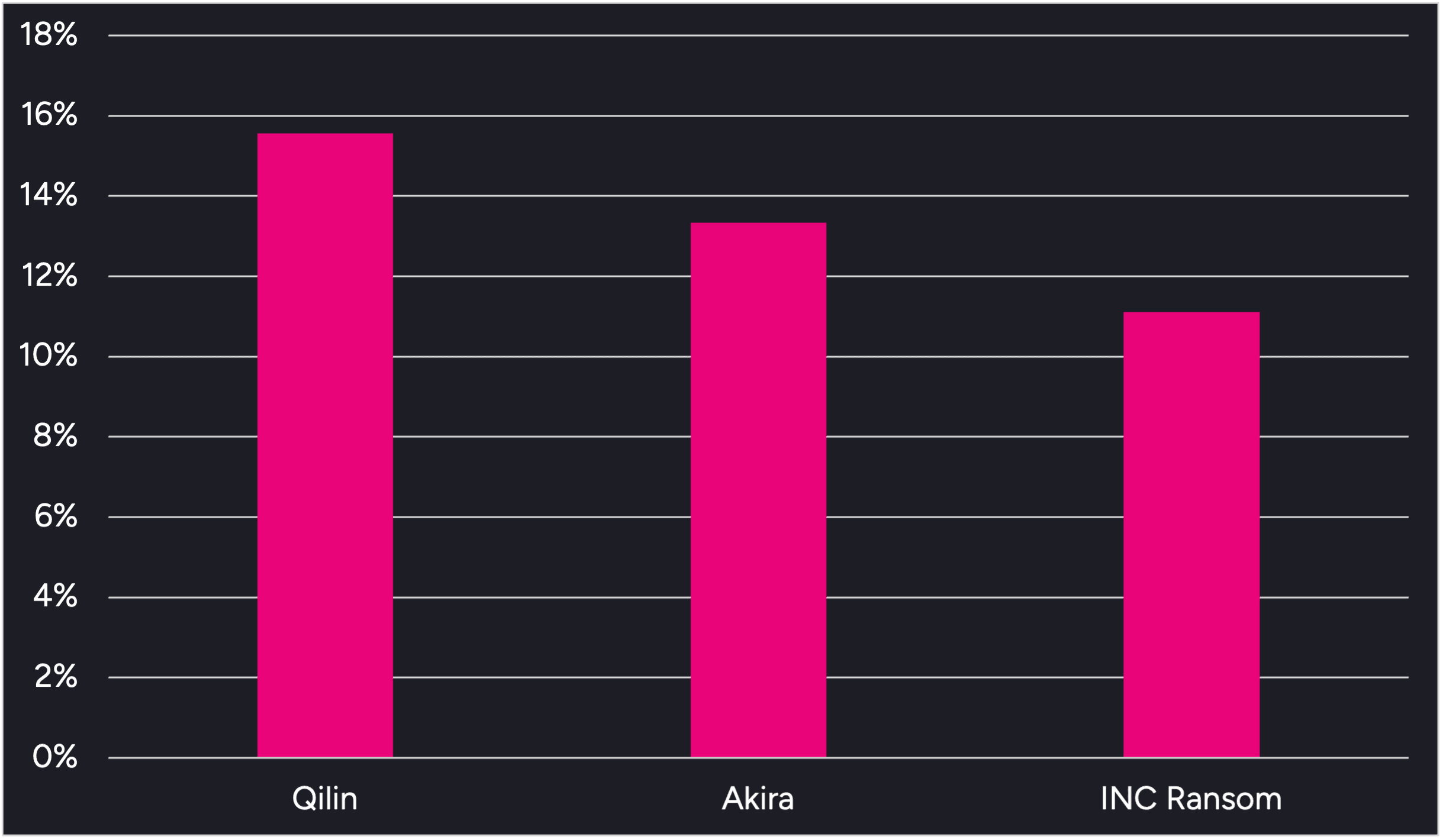
Figure 1. Activity from the top 3 threat groups in April 2026
Throughout the month, analysts at Arete identified several trends behind the threat actors perpetrating cybercrime activities:
Multiple ransomware operations continue to leverage the Bring Your Own Vulnerable Driver (BYOVD) technique to disable endpoint security controls prior to ransomware deployment. Qilin has recently been observed leveraging a malicious file loaded via DLL side-loading along with vulnerable drivers, including rwdrv.sys and hlpdrv.sys, to gain kernel-level access and disable security processes. Arete observed Akira using the same vulnerable drivers in multiple engagements dating back to Q3 2025.
DragonForce has leveraged several of the same tools in recent engagements, including the remote desktop application Remotely Agent and the PoisonX.sys vulnerable driver. Additionally, open-source reporting indicates that the group recently used a Python-based backdoor known as VIPERTUNNEL to maintain reliable operator access and evade detection. DragonForce was responsible for over 7% of Arete ransomware engagements in April, and Arete notes increased activity from the group this year compared to 2025.
A social engineering tactic has reemerged in recent months in which threat actors impersonate IT and helpdesk staff via Microsoft Teams to contact employees and attempt to convince them to install remote access tools like Quick Assist, giving the threat actors remote access to the victim’s environment. This tactic was initially observed in late 2024 and early 2025 and was linked to now-defunct groups like Black Basta and Cactus, but has more recently been observed in intrusions linked to the Akira and Payouts King ransomware groups.
Sources
Arete Internal
Article
Payouts King Utilizes QEMU Emulator to Bypass EDR
Researchers recently identified threat actor campaigns leveraging QEMU, a free open-source virtual machine (VM) emulator, to evade endpoint security solutions. Since QEMU acts as a VM within the target environment, endpoint detection tools cannot scan inside the emulator or detect any malicious files or payloads QEMU contains. Although threat actors have been utilizing QEMU maliciously since 2020, recent activity is attributed to the Payouts King ransomware group and a cluster of threat actors believed to be initial access brokers who have also been exploiting the CitrixBleed2 vulnerability CVE-2025-5777.
What’s Notable and Unique
Payouts King has been observed deploying QEMU since November and uses the VM to create a reverse SSH backdoor to evade detection and install various tools, including Rclone, Chisel, and BusyBox.
In a separate campaign, threat actors are exploiting CVE-2025-5777, a Citrix NetScaler vulnerability that allows attackers to bypass authentication. Once they’ve gained initial access, the threat actors use QEMU to deploy tools inside the VM, which are then used to steal credentials, identify Kerberos usernames, perform Active Directory reconnaissance, and set up FTP servers for staging or data exfiltration.
Analyst Comments
Threat actors continue to focus their efforts on defense evasion, often leveraging legitimate, easily accessible tools such as QEMU. The continued use of QEMU by multiple threat actors highlights the effectiveness of these tactics and the difficulty in detecting and defending against them. To counter this campaign, organizations should proactively monitor for unauthorized QEMU installations, abnormal scheduled tasks, and port forwarding rules.
Sources
QEMU abused to evade detection and enable ransomware delivery
Article
Microsoft Teams Continues to be Leveraged in Social Engineering Attacks
Microsoft warns that threat actors are increasingly abusing Microsoft Teams and relying on legitimate tools to gain access and conduct lateral movement within enterprise networks. The threat actors impersonate IT or helpdesk staff to contact employees via cross-tenant chats and trick them into granting remote access for data theft. Microsoft has observed multiple intrusions with a similar attack chain that utilized commercial remote management software, like Quick Assist and the Rclone utility, to transfer files to an external cloud storage service. This tactic, notably associated with Black Basta and Cactus ransomware operations in late 2024 and early 2025, appears to have resurfaced, with similar activity more recently observed in intrusions linked to the Akira and Payouts King ransomware groups.
What’s Notable and Unique
Initial access is achieved by leveraging external collaboration features in Microsoft Teams to allow impersonation of internal support personnel, tricking users into bypassing security warnings. This reflects abuse of legitimate functionality rather than exploitation of a Microsoft Teams vulnerability.
Following initial access, attackers conduct rapid reconnaissance using Command Prompt and PowerShell to assess privileges, domain membership, and opportunities for lateral movement. Persistence is maintained through Windows Registry modifications, after which attackers leveraged WinRM for lateral movement, targeting domain-joined systems and high-value assets, including domain controllers.
Malicious payloads were staged in user-writable directories and executed through DLL side-loading via trusted, signed applications, enabling covert code execution while blending with legitimate activity. Additional remote management tools were also deployed to support broader access, while Rclone or similar utilities were used to stage and exfiltrate sensitive data to external cloud storage.
Analyst Comments
This activity highlights how modern threat actors can leverage trusted collaboration workflows, remote management tools, and stealthy exfiltration techniques to conduct intrusions through a combination of social engineering and misuse of legitimate functionality. Effective defense depends on layered mitigations that combine identity controls, restricted remote administration, endpoint hardening, network protections, and user awareness measures to disrupt attacker activity at multiple stages of the intrusion lifecycle. To mitigate the risk of this and similar campaigns, users should treat external Teams contacts as untrusted by default, and administrators should restrict or closely monitor remote assistance tools while limiting WinRM usage to controlled systems.
Sources
Cross‑tenant helpdesk impersonation to data exfiltration: A human-operated intrusion playbook
Microsoft: Teams increasingly abused in helpdesk impersonation attacks
Payouts King Takes Aim at the Ransomware Throne
Article
Phishing-as-a-Service Evolves with Venom
“Whaling” has taken on a new meaning with a highly targeted phishing campaign active from November 2025 through March 2026, aimed exclusively at senior executives from more than 20 industries. The campaign, dubbed VENOM, is a phishing-as-a-service (PhaaS) platform that combines advanced evasion capabilities with immediate persistence of targeted executives. The initial phish impersonates an internal SharePoint document notification and uses embedded QR codes to convince victims to shift to unmanaged mobile devices to bypass corporate security controls. VENOM aims to establish persistence immediately by either registering a new MFA device or retaining long-lived refresh tokens, allowing threat actors to maintain access even after password resets or other base-level remediation efforts.
What’s Notable and Unique
This campaign is unique in its targeted nature of the PhaaS platform rather than broad, sweeping attempts. The threat actors behind VENOM create convincing phishing emails that impersonate SharePoint activity using the victim’s own domain, company name, and even fabricated email threads. These convincing social engineering tactics, combined with the specific targeting of executives, make this an effective capability for cybercriminals.
VENOM operates as a closed-access system, with full adversarial support, but has no public visibility on the dark web or from security researchers. The service likely operates on an invite-only basis, unlike most PhaaS platforms, which typically seek to have as many paying customers as possible. This, among other items such as the sophisticated evasion techniques, indicates a higher degree of sophistication than most other PhaaS offerings.
Either through MFA enrollment or Microsoft Device Code abuse, the threat actor forces the victim to aid them in establishing persistence early in the attack lifecycle. These tactics result in either valid tokens or an additional MFA login method controlled by the threat actor, meaning typical password resets alone are not effective against this technique. Administrators would be required to explicitly revoke sessions and token grants to mitigate the threat actors’ persistence.
Analyst Comments
Oftentimes, MFA is viewed as a one-stop shop to cybersecurity, but tactics such as this show how threat actors can bypass MFA, or worse, use it to establish persistence. Ultimately, this campaign highlights how modern attacks increasingly abuse legitimate authentication workflows rather than attempting to defeat them outright. Defenses that rely solely on MFA without other security posturing, such as continuous session monitoring, token revocation, and identity logging, can leave organizations vulnerable. As attackers shift toward token theft and device trust abuse, incident response and identity security strategies must evolve accordingly.
Sources
Meet VENOM: The PhaaS Platform That Neutralizes MFA



