Article
Scattered Spider Adapts to Evolving Threat Landscaped
Arete Analysis

As Arete reported in last week’s article, RansomHub emerged as a new Ransomware-as-a-Service (RaaS) operation in early 2024 and has already targeted several high-profile victims, including telecom giant Frontier Communications and Christie’s auction house. According to a recent analysis, at least one affiliate of RansomHub is a present or former member of the Scattered Spider threat group and previously worked with ALPHV/BlackCat prior to its shutdown. According to the report, the RansomHub affiliate was observed using the same tools, tactics, and techniques previously used by a Scattered Spider threat actor.
These tools include ngrok for remote access, remote desktop client Remmina, and Tailscale virtual private network (VPN) service.
Similar tactics included the use of social engineering by individuals with American accents to manipulate victims into resetting account passwords.
Scattered Spider: #OpenToWork
Scattered Spider—also known by several other names, including Octo Tempest, Oktapus, Scattered Swine, and UNC3944—is a sophisticated threat group that has been active since at least May 2022. The group is known to conduct solo exfiltration-based extortion attacks and work within the affiliate structure of the now-defunct ALPHV RaaS. As an affiliate of ALPHV, Scattered Spider gained notoriety after its alleged attack on Caesars Entertainment and MGM Resorts in late 2023.
Law enforcement operations against ALPHV in December 2023 eventually led to the RaaS group shutting down its operations in March 2024. RansomHub was one of the emerging RaaS groups that took advantage of the pool of ex-ALPHV affiliates and began posting recruiting advertisements on Dark Web forums that referenced ALPHV’s struggles and offered a generous 90/10 payment split for new affiliates.
Evolving Tactics – Scattered Spider Getting SaaSy
In addition to Scattered Spider reportedly aligning with RansomHub, separate reporting indicated that the group has been focusing on data theft extortion without using ransomware, expanding tactics to include data theft from software-as-a-service (SaaS) applications. In the past, Scattered Spider was known to leverage compromised credentials and social engineering attacks via phishing and SIM swapping to gain access to victim networks. However, Scattered Spider threat actors recently shifted to using stolen credentials to access SaaS applications, including vCenter, CyberArk, SalesForce, Azure, CrowdStrike, Amazon Web Service (AWS), and Google Cloud Platform (GCP). After gaining access to a victim’s environment, they use legitimate cloud syncing tools to move victim data to services like AWS and GCP.
Analyst Comments
Law enforcement operations against large RaaS groups like ALPHV and LockBit in 2024 created a fractured ransomware landscape, but groups like Scattered Spider are finding ways to adapt their operations and tactics. Although recent reports seem to portray conflicting tactics of data theft and ransomware, both are aligned with previous Scattered Spider operations. The group remains opportunistic, operating independently in data theft-only attacks, as well as aligning with RaaS groups. Given RansomHub’s focus on recruiting ex-APLHV affiliates, it makes sense that Scattered Spider would pivot between affiliate structures and work with the emerging RaaS, particularly given the lucrative affiliate terms promised on RansomHub’s recruitment posts. Although its tactics or affiliations may shift, Scattered Spider will likely remain a dynamic threat group and pivot to the opportunities that meet its evolving needs.
Sources
Back to Blog Posts
Podcast
Cyber Risk and Insurance for Law Firms
In this episode of Bytes of Insight, host Vinny Sakore is joined by Laura Zaroski, Managing Director of the Law Firms Group at Gallagher, as they discuss the evolution of cyber risk for law firms. Tune in for firsthand insights on how to select the right cyber policy, the incident response process, and the nuances of ransom payments and sensitive data.
Article
Canvas Platform Compromised by ShinyHunters
In early May, the ShinyHunters threat group claimed responsibility for a large-scale cyberattack on the Canvas learning management platform, affecting almost 9,000 educational institutions worldwide. Instructure, the education technology company that owns Canvas, confirmed the intrusion and, on May 11th, announced that a settlement was reached with the threat actor. According to the statement, the settlement included return of the stolen data to Instructure, assurance of destruction of any copies of the data, and assurance that no Canvas users would be extorted for additional ransom payments.
Unauthorized activity was first detected in Canvas on April 29th and was reportedly the result of cross-site scripting vulnerabilities. Leveraging the same vulnerability, the threat actor conducted a follow-up attack on May 7th, replacing the login screens of Canvas users at hundreds of institutions with a message from ShinyHunters, claiming responsibility for the attack and displaying a list of impacted schools and the threat actor’s contact information.
By May 8th, neither Canvas nor Instructure was posted on ShinyHunter’s data leak site (DLS), and instead a vague “Press Statement” indicated that the group would not comment on the incident. On May 9th, Instructure shared another update, indicating that Canvas was “fully back online and available for use,” along with updates to the company’s FAQ page.
Figure 1. Press statement on ShinyHunters DLS (Source: Arete)
ShinyHunters: Not Just For Pokémon Anymore
ShinyHunters is a predominantly English-speaking cybercriminal group first observed in 2020 that focuses on data exfiltration and extortion. During its early operational phase, the group carried out a series of data breaches targeting organizations, including Tokopedia, Wattpad, and Nitro PDF, establishing a reputation for compromising and monetizing large datasets. Over this period, ShinyHunters remained heavily centered on a “pay or leak” model, leveraging stolen data to pressure victims into ransom payments or selling the information on underground forums when demands were not met.
As the group matured, it evolved beyond opportunistic database theft into a more sophisticated threat actor capable of executing complex, large-scale intrusion campaigns. ShinyHunters has since demonstrated an ability to target higher‑profile industries, including telecommunications, aviation, and enterprise software-as-a-service (SaaS) platforms, by leveraging advanced tactics such as social engineering, SaaS abuse, and supply chain compromise.
The group went as far as to partner with two other threat groups to form the Scattered Lapsus$ Hunters (SLH) collective in early 2025. Playing to each group’s strengths, SLH leveraged compromised OAuth tokens from the Salesloft Drift integration in an advanced supply-chain attack that led to the exfiltration of data across hundreds of Salesforce instances. Despite multiple law enforcement actions and arrests linked to its members, the group has remained operational under the same branding for several years. This persistence highlights the group’s resilience and adaptability, suggesting an operational model that can evolve in response to external pressures.
Analyst Comments
Given the group’s track record, ShinyHunters is likely to continue conducting large-scale data theft and extortion operations while further engraining itself within the broader cybercriminal ecosystem. This recent incident highlights the disproportionate impact of cyberattacks against supply chain vendors like SaaS platforms, open-source ecosystems, MSPs, and cloud integrations, where a breach on one platform can affect thousands of organizations. Any organizations impacted by the recent Canvas incident should not attempt any communication with the threat actor and should continue to follow any future guidance posted on Instructure’s Incident Update & FAQ page.
Sources
Security Incident Update & FAQs
Canvas login portals hacked in mass ShinyHunters extortion campaign
ShinyHunters: A Threat Profile
ShinyHunters
Scattered LAPSUS$ Hunters: Anatomy of a Federated Cybercriminal Brand
FBI warns of UNC6040, UNC6395 hackers stealing Salesforce data
Article
Critical MOVEit Automation Vulnerabilities Disclosed
A security advisory released by Progress Software details critical and high-severity vulnerabilities affecting their MOVEit Automation managed file transfer (MFT) solution. The vulnerabilities, tracked as CVE-2026-4670 and CVE-2026-5174, could allow a threat actor to bypass authentication and escalate privileges, leading to unauthorized access, administrative control, and data exposure. Cybercriminals have leveraged several MFT tools in previous campaigns, including the Accellion File Transfer Application (FTA), Fortra GoAnywhere MFT, and Cleo MFT. Flaws in MFT software are highly targeted by cybercriminals due to the volume and sensitivity of the data they control.
What’s Notable and Unique
MOVEit Transfer was heavily exploited by the Cl0p ransomware group in the summer of 2023. While the window of exploit activity lasted only a few weeks, victim extortion and data leaks continued throughout the remainder of the year, leading to more than 70 class-action lawsuits filed in the U.S.
There is no workaround or hotfix for these vulnerabilities. To fully patch the flaws, MOVEit administrators need to perform a "full install" of the latest version, which will require taking the system offline.
Security researchers have discovered ~1,400 MOVEit Automation instances exposed to the internet, with dozens belonging to U.S. local and state government agencies.
Analyst Comments
While the vulnerabilities patched in Progress Software's recent release differ from the SQL injection vulnerability exploited by the Cl0p ransomware group in 2023, exploitation of CVE-2026-4670 and CVE-2026-5174 could lead to equally impactful outcomes. Beyond the immediate impacts on affected organizations, trusted data-exchange platforms provide threat actors with an avenue to obtain sensitive information and infect partner and supplier environments. Furthermore, Arete has seen the time window between disclosure and weaponization of critical vulnerabilities continue to shrink, especially as threat actors increasingly adopt AI-enabled tooling. As such, organizations should not only implement the patches released by Progress Software, but also hunt for typical post-compromise behavior like enumeration of the underlying database, the creation of new user accounts or users operating with unexpected administrator privileges, and the presence of unauthorized remote monitoring and management (RMM) tools.
Sources
MOVEit Automation Critical Security Alert Bulletin – April 2026 – (CVE-2026-4670, CVE-2026-5174)
From Breach to Courtroom: Inside the MOVEit Exploitation and Mass Litigation
Progress warns of critical MOVEit Automation auth bypass flaw
Article
Ransomware Trends & Data Insights: April 2026
The threat landscape has remained relatively predictable thus far in 2026. In April, Qilin dethroned Akira as the most active threat group for the month. Akira, who had been the top ransomware threat each month since July 2025, was still only slightly behind Qilin and had roughly the same activity level as in March. INC Ransom and DragonForce also remained active threats in April, with those four ransomware groups accounting for half of all ransomware and extortion activity observed by Arete.
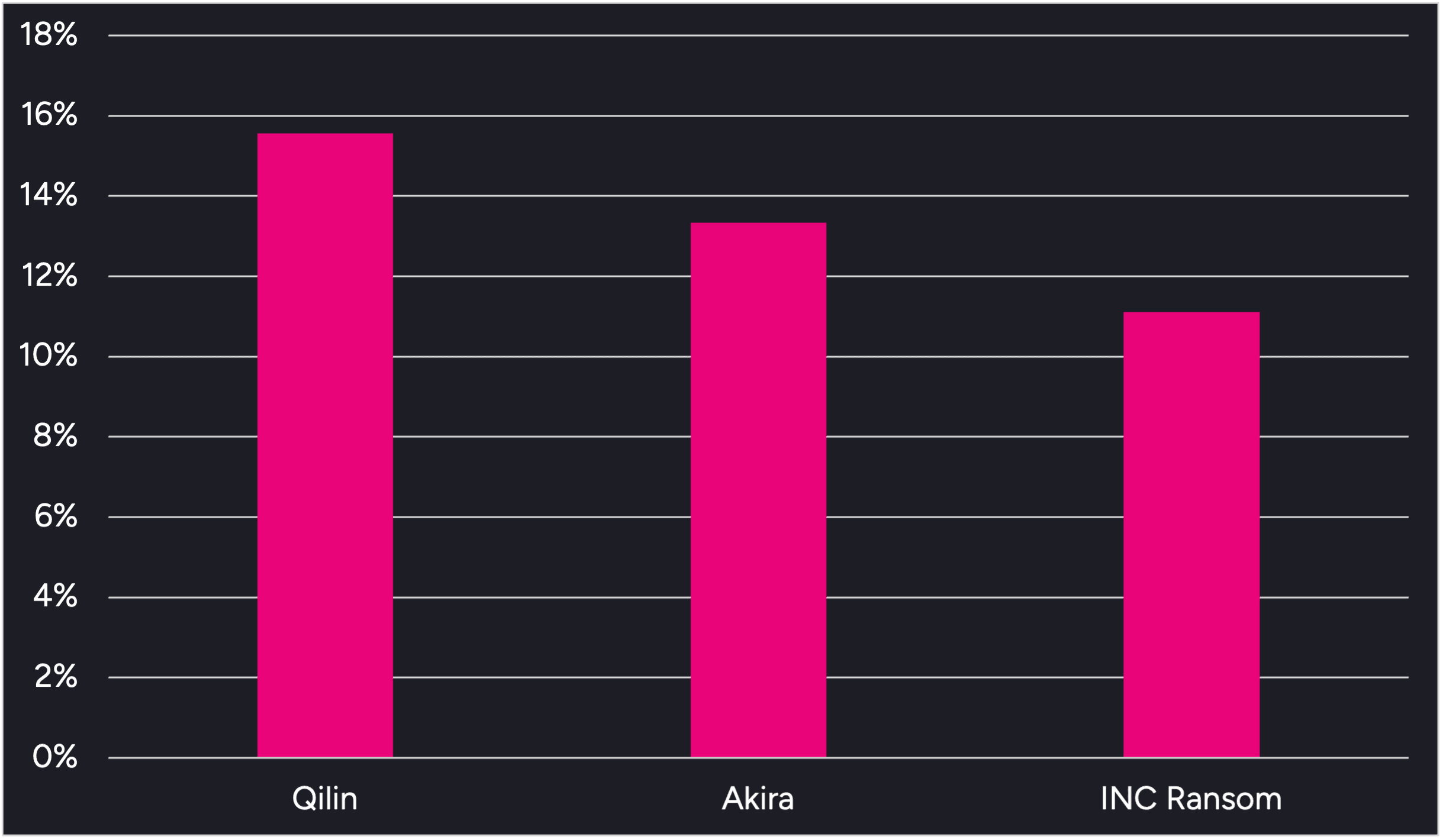
Figure 1. Activity from the top 3 threat groups in April 2026
Throughout the month, analysts at Arete identified several trends behind the threat actors perpetrating cybercrime activities:
Multiple ransomware operations continue to leverage the Bring Your Own Vulnerable Driver (BYOVD) technique to disable endpoint security controls prior to ransomware deployment. Qilin has recently been observed leveraging a malicious file loaded via DLL side-loading along with vulnerable drivers, including rwdrv.sys and hlpdrv.sys, to gain kernel-level access and disable security processes. Arete observed Akira using the same vulnerable drivers in multiple engagements dating back to Q3 2025.
DragonForce has leveraged several of the same tools in recent engagements, including the remote desktop application Remotely Agent and the PoisonX.sys vulnerable driver. Additionally, open-source reporting indicates that the group recently used a Python-based backdoor known as VIPERTUNNEL to maintain reliable operator access and evade detection. DragonForce was responsible for over 7% of Arete ransomware engagements in April, and Arete notes increased activity from the group this year compared to 2025.
A social engineering tactic has reemerged in recent months in which threat actors impersonate IT and helpdesk staff via Microsoft Teams to contact employees and attempt to convince them to install remote access tools like Quick Assist, giving the threat actors remote access to the victim’s environment. This tactic was initially observed in late 2024 and early 2025 and was linked to now-defunct groups like Black Basta and Cactus, but has more recently been observed in intrusions linked to the Akira and Payouts King ransomware groups.
Sources
Arete Internal



