Article
Empowering Cybersecurity Career Advancement in India
At Arete

Companies around the world have long relied on India for cost-effective technical outsourcing. Thanks to the country’s abundance of highly trained technical talent, it’s been a successful support model. But like any successful business strategy, there’s always room for improvement. Particularly when it comes to security.
When NotPetya hit a few years ago, it should have been a global wake-up call. And now, if the SolarWinds attack has taught us anything, it’s that we can’t keep hitting the snooze button on cybersecurity. Like elsewhere, supply chain attacks — as well as ransomware and malware attacks — are a worrisome reality in India.
At Arete, we have an opportunity to tackle this challenge head-on and forge a new path — in a leading, not supporting role — to build strong, world-class defense capabilities for India’s businesses.
Homegrown Talent And Relationship Building
It all starts with developing talent. At Arete, we give our employees the tools to advance their careers in a direction that makes sense for them and the company — no matter their geographical location.
To help fulfill this mission, we are bringing our North American cyber career model to India. Our aim is to seed organic growth, build local capacity, and create more leadership opportunities in-country. We believe that employees should be empowered to grow their cyber careers beyond IT support roles, without feeling compelled to emigrate elsewhere.
Taking Technology Skills And Careers To The Next Level
It’s not necessary to know everything up front. Whether our employees begin in IT support, system administration, or digital forensics roles, Arete has programs designed to help them develop the cybersecurity skills they need to move from support to leadership roles.
We focus on an employee’s talents and interests, pair them with colleagues whose abilities complement theirs, and provide a framework for cross-functional collaboration that allows the whole team to build on one another’s strengths and learn new skills on the job.
Beyond Technical Skills: What Success Looks Like
Beyond the jumping-off point of technical degrees and certifications, it’s often the soft skills that will set an individual apart and above in this field. For success, a cybersecurity professional must possess a flexible mindset and the ability to adapt to changing situations, troubleshoot under pressure, and demonstrate tenacity through crises. They should also be able to proactively visualize attack vectors, high-value assets, layers of defense, and containment measures.
A well-rounded skill set will take you far. And whatever team you belong to at Arete, you can know your work will be generating data-driving intelligence that directly supports the discovery of brand-new indicators of compromise (IoCs). As your skill sets mature, you will be expected to assert yourself in what will often be actual business-saving endeavors throughout India. And you’ll be able to see how your threat hunts and searches for anomalous behavior and new activity will enable clients not only react to cyberattacks, but proactively stop them.
If you have a desire to help protect Indian businesses from corrupt cybercriminals, consider joining the Arete team in one of our currently open positions. Here, you’ll be surrounded by the best and brightest in the field. Professionals who can and will help you take your career to the highest level.
Back to Blog Posts
Article
FortiGate Exploits Enable Network Breaches and Credential Theft
A recent security report indicates that threat actors are actively exploiting FortiGate Next-Generation Firewall (NGFW) appliances as initial access vectors to compromise enterprise networks. The activity leverages recently disclosed vulnerabilities or weak credentials to gain unauthorized access and extract configuration files, which often contain sensitive information, including service account credentials and detailed network topology data.
Analysis of these incidents shows significant variation in attacker dwell time, ranging from immediate lateral movement to delays of up to two months post-compromise. Since these appliances often integrate with authentication systems such as Active Directory and Lightweight Directory Access Protocol (LDAP), their compromise can grant attackers extensive access, substantially increasing the risk of widespread network intrusion and data exposure.
What’s Notable and Unique
The activity involves the exploitation of recently disclosed security vulnerabilities, including CVE-2025-59718, CVE-2025-59719, and CVE-2026-24858, or weak credentials, allowing attackers to gain administrative access, extract configuration files, and obtain service account credentials and network topology information.
In one observed incident, attackers created a FortiGate admin account with unrestricted firewall rules and maintained access over time, consistent with initial access broker activity. After a couple of months, threat actors extracted and decrypted LDAP credentials to compromise Active Directory.
In another case, attackers moved from FortiGate access to deploying remote access tools, including Pulseway and MeshAgent, while also utilizing cloud infrastructure such as Google Cloud Storage and Amazon Web Services (AWS).
Analyst Comments
Arete has identified multiple instances of Fortinet device exploitation for initial access, involving various threat actors, with the Qilin ransomware group notably leveraging Fortinet device exploits. Given their integration with systems like Active Directory, NGFW appliances remain high-value targets for both state-aligned and financially motivated actors. In parallel, Arete has observed recent dark web activity involving leaked FortiGate VPN access, further highlighting the expanding risk landscape. This aligns with the recent reporting from Amazon Threat Intelligence, which identified large-scale compromises of FortiGate devices driven by exposed management ports and weak authentication, rather than vulnerability exploitation. Overall, these developments underscore the increasing focus on network edge devices as entry points, reinforcing the need for organizations to strengthen authentication, restrict external exposure, and address fundamental security gaps to mitigate the risk of widespread compromise.
Sources
FortiGate Edge Intrusions | Stolen Service Accounts Lead to Rogue Workstations and Deep AD Compromise
Article
Vulnerability Discovered in Anthropic’s Claude Code
Security researchers discovered two critical vulnerabilities in Anthropic's agentic AI coding tool, Claude Code. The vulnerabilities, tracked as CVE-2025-59536 and CVE-2026-21852, allowed attackers to achieve remote code execution and to compromise a victim's API credentials. The vulnerabilities exploit maliciously crafted repository configurations to circumvent control mechanisms. It should be noted that Anthropic worked closely with the security researchers throughout the process, and the bugs were patched before the research was published.
What’s Notable and Unique
The configuration files .claude/settings.json and .mcp.json were repurposed to execute malicious commands. Because the configurations could be applied immediately upon starting Claude Code, the commands ran before the user could deny permissions via a dialogue prompt, or they bypassed the authentication prompt altogether.
.claude/settings.json also defines the endpoint for all Claude Code API communications. By replacing the default localhost URL with a URL they own, an attacker could redirect traffic to infrastructure they control. Critically, the authentication traffic generated upon starting Claude Code included the user's full Anthropic API key in plain text and was sent before the user could interact with the trust dialogue.
Restrictive permissions on sensitive files could be bypassed by simply prompting Claude Code to create a copy of the file's contents, which did not inherit the original file's permissions. A threat actor using a stolen API key could gain complete read and write access to all files within a workspace.
Analyst Comments
The vulnerabilities and attack paths detailed in the research illustrate the double-edged nature of AI tools. The speed, scale, and convenience characteristics that make AI tools attractive to developer teams also benefit threat actors who use them for nefarious purposes. Defenders should expect adversaries to continue seeking ways to exploit configurations and orchestration logic to increase the impact of their attacks. Organizations planning to implement AI development tools should prioritize AI supply-chain hygiene and CI/CD hardening practices.
Sources
Caught in the Hook: RCE and API Token Exfiltration Through Claude Code Project Files | CVE-2025-59536 | CVE-2026-21852
Article
Ransomware Trends & Data Insights: February 2026
After a slight lull in January, Akira and Qilin returned to dominating ransomware activity in February, collectively accounting for almost half of all engagements that month. The rest of the threat landscape remained relatively diverse, with a mix of persistent threats like INC and PLAY, older groups like Cl0p and LockBit, and newer groups like BravoX and Payouts King. Given current trends, the first quarter of 2026 will likely remain relatively predictable, with the top groups from the second half of 2025 continuing to operate at fairly consistent levels month to month.
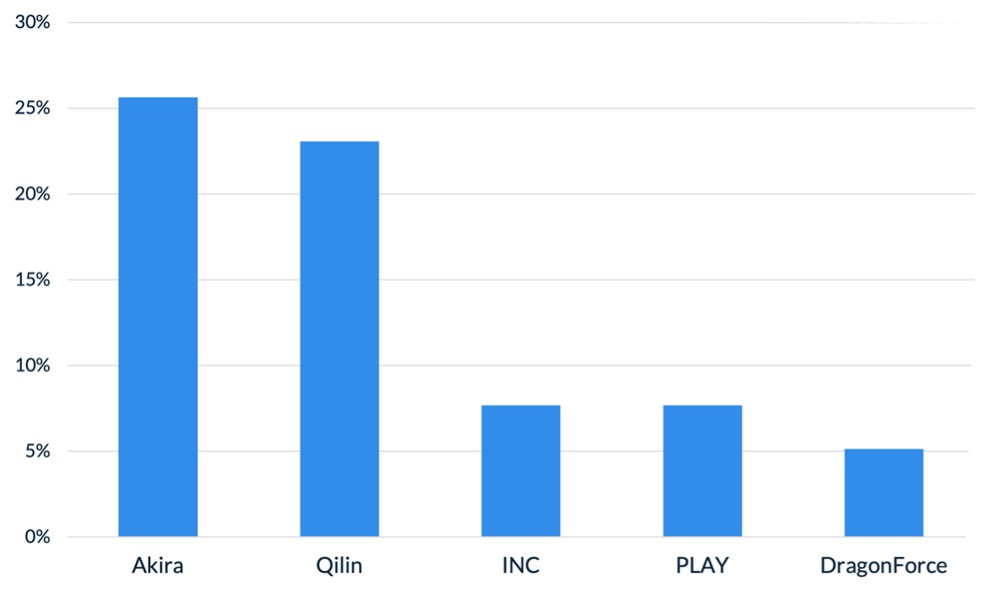
Figure 1. Activity from the top 5 threat groups in February 2026
Throughout the month of February, analysts at Arete identified several trends behind the threat actors perpetrating cybercrime activities:
In February, Arete observed Qilin actively targeting WatchGuard Firebox devices, especially those vulnerable to CVE-2025-14733, to gain initial access to victim environments. CVE-2025-14733 is a critical vulnerability in WatchGuard Fireware OS that allows a remote, unauthenticated threat actor to execute arbitrary code. In addition to upgrading WatchGuard devices to the latest Firebox OS version, which patches the bug, administrators are urged to rotate all shared secrets on affected devices that may have been compromised and may be used in future campaigns.
Reports from February suggest that threat actors are increasingly exploring AI-enabled tools and services to scale malicious activities, demonstrating how generative AI is being integrated into both espionage and financially motivated threat operations. The Google Threat Intelligence Group indicated that state-backed threat actors are leveraging Google’s Gemini AI as a force multiplier to support all stages of the cyberattack lifecycle, from reconnaissance to post-compromise operations. Separate reporting from Amazon Threat Intelligence identified a threat actor leveraging commercially available generative AI services to conduct a large-scale campaign against FortiGate firewalls, gaining access through weak or reused credentials protected only by single-factor authentication.
The Interlock ransomware group recently introduced a custom process-termination utility called “Hotta Killer,” designed to disable endpoint detection and response solutions during active intrusions. This tool exploits a zero-day vulnerability (CVE-2025-61155) in a gaming anti-cheat driver, marking a significant adaptation in the group’s operations against security tools like FortiEDR. Arete is actively monitoring this activity, which highlights the growing trend of Bring Your Own Vulnerable Driver (BYOVD) attacks, in which threat actors exploit legitimate, signed drivers to bypass and disable endpoint security controls.
Sources
Arete Internal
Article
ClickFix Campaign Delivers Custom RAT
Security researchers identified a sophisticated evolution of the ClickFix campaign that aims to compromise legitimate websites before delivering a five-stage malware chain, culminating in the deployment of MIMICRAT. MIMICRAT is a custom remote access trojan (RAT) written in the C/C++ programming language that offers various capabilities early in the attack lifecycle. The attack begins with victims visiting compromised websites, where JavaScript plugins load a fake Cloudflare verification that tricks users into executing a malicious PowerShell script, further displaying the prominence and effectiveness of ClickFix and its user interaction techniques.
Not Your Average RAT
MIMICRAT displays above-average defense evasion and sophistication, including:
A five-stage PowerShell sequence beginning with Event Tracing for Windows and Anti-Malware Scan Interface bypasses, which are commonly used in red teaming for evading detection by EDR and AV toolsets.
The malware later uses a lightweight scripting language that is scripted into memory, allowing malicious actions without files that could easily be detected by an EDR tool.
MIMICRAT uses malleable Command and Control profiles, allowing for a constantly changing communication infrastructure.
The campaign uses legitimate compromised infrastructure, rather than attacker-owned tools, and is prepped to use 17 different languages, which increases global reach and defense evasion.
Analyst Comments
The ClickFix social engineering technique remains an effective means for threat actors to obtain compromised credentials and initial access to victim environments, enabling them to deploy first-stage malware. Coupled with the sophisticated MIMICRAT RAT, the effectiveness of this campaign could increase. Arete will continue monitoring for changes to the ClickFix techniques, the deployment of MIMICRAT in other campaigns, and other pertinent information relating to the ongoing campaign.
Sources
MIMICRAT: ClickFix Campaign Delivers Custom RAT via Compromised Legitimate Websites



