3/17/2021
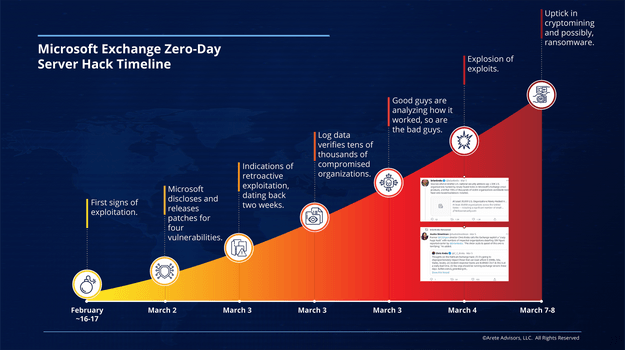
 On March 2, 2021, Microsoft disclosed and provided security updates for four [4] critical vulnerabilities — CVE-2021-26855, CVE-2021-26857, CVE-2021-26858, and CVE-2021-27065 — impacting on-premises Microsoft Exchange Servers.
On March 2, 2021, Microsoft disclosed and provided security updates for four [4] critical vulnerabilities — CVE-2021-26855, CVE-2021-26857, CVE-2021-26858, and CVE-2021-27065 — impacting on-premises Microsoft Exchange Servers.
While Internet-facing Exchange Servers, such as Outlook Web Access systems, are at particular risk — and especially those at organizations without a dedicated Exchange Server administrator — Microsoft says the vulnerabilities do not impact Office 365/Exchange online mailboxes.
The Microsoft Threat Intelligence Center (MSTIC) attributes the activity to HAFNIUM, a Chinese state-sponsored threat group. Chinese state-sponsored threat actors historically target government agencies, higher-education institutions, law firms, defense contractors, policy think tanks, non-governmental organizations (NGOs), and most recently, infectious disease researchers.
IMMEDIATE ACTION: If you have not done so already, review the Microsoft advisories and apply patches to protect vulnerable systems.
Arete Contextual Insights
- State-sponsored threat groups, such as HAFNIUM, have the time, skills, and resources to manufacture these potent vulnerability exploits. They are not, however, the only bad actors wielding these techniques.
- Beyond what Chinese state-sponsored operations have perpetrated, Arete expects broad impact in high orders of magnitude across multiple industry verticals.
- Since the disclosure, multiple security researchers have been analyzing the Exchange
vulnerability patches. Arete can assert that cybercriminals and other state-sponsored actors are doing the same, most likely racing against patch cycles. - The Cybersecurity and Infrastructure Security Agency (CISA) and other high-fidelity sources estimate that tens of thousands of organizations are likely compromised. Via research channels, Arete is aware that one high-fidelity source provided Information Sharing and Analysis Centers (ISACs) with a list of approximately 12,000 organizations for victim notification.
- Leveraging Microsoft resources, Arete has identified multiple impacted clients and is currently responding to exploitations across a broad variety of organizations from a variety of cybercrime actors deploying payloads, including, but not limited to, cryptomining malware and ransomware.
Follow-On Actions
Assess systems to validate compromise and analyze impact. Rapid identification and triage
analysis through deployment of SentinelOne and data collection scripts across the impacted Exchange Server(s) to identify malicious activity.
- Implement protective measures to harden environments. Based on findings, deploy SentinelOne throughout the remainder of the environment to identify all instances of lateral movement, search for indicators of compromise (IOC’s), and provide insight into the current state of systems health throughout the environment.
Additional Defense Services Available
Managed Detection and Response (MDR) service combines cutting-edge machine learning and artificial intelligence technologies with insights from Arete cyber professionals to provide 24/7 monitoring, reporting, and defense against threats.
Cyber Strategy and Defense. Arete performs current-state testing to assess clients’ cyber hygiene and create a prioritized action plan that closes identified security gaps, strengthens existing infrastructure, and formalizes people, processes, and technologies into a robust cybersecurity program.
Cloud Advisory and Architecture Services. Arete helps clients navigate the shared responsibility model, advising on cloud architectures based on economics, business use, and security.