Article
SIEM vs. XDR: Advances in Security Monitoring and Cyber Defense
Arete Analysis
Cybersecurity 101

The cybersecurity industry is chockfull of jargon, abbreviations, and acronyms. So much so that it can often be difficult to decide which tools may provide the best protection for your company. To help, we’d like to clarify some terms and review the benefits of a few solutions.
Let’s begin with SIEMs
Security information and event management (SIEM) technology has been around for a long time. Having evolved from log aggregation, log management, and event management, SIEMs serve to collect, aggregate, analyze, and store large volumes of log data from across numerous systems.
SIEM vendors began by taking a broad approach and collecting available log and event data from almost any source across an enterprise. Over time, they extended a SIEM’s reach from the office to the manufacturing floor and beyond. The goal was to gain more complete visibility across an organization’s landscape — from firewalls and switches to operating systems and applications. Unfortunately, the level of detail in the data from each source is typically low. In other words, SIEMs provide wide, but shallow data sets, which requires far more work to derive meaning from them — and work is time and money.
Not only can it take years to map all the low–resolution log data to a meaningful alert, but also, with COVID–19 creating the new work–from–home norm, companies are now gathering far few system logs. Thanks to alternative, cloud–based solutions, many users simply never need a virtual private network (VPN) to communicate back to the company network.
Even though many SIEM solutions are adding agents to endpoints to gather and push logs to a cloud collector, if a person is working from home and not accessing the network for data, why create alerts from that computer’s logs if they don’t affect the security of the internal network? This would require a security engineer to further tune segregation issues — and that’s if you’re lucky enough to have an engineer on staff.
The advantages of EDR and XDR
Today, extended detection and response (XDR) tools are gaining traction. As the name would imply, they are an evolution of endpoint detection and response (EDR) tools, which combine antivirus with post–detection analysis capabilities — for example, enhanced alerting, automatic stopping and quarantining of malicious behavior, signature– and threat intelligence–based detection, and full–blown artificial intelligence on systems for autonomous operations.
While an XDR solution may appear similar in function to a SIEM platform, it offers much more. And that’s why Arete chooses to use XDR with our Managed Detection and Response (MDR) service.
The XDR console lives in the cloud to allow for fast, accurate reporting on what’s occurring across your entire pool of assets. In fact, it provides rich metadata on every event that occurs on monitored endpoints; records every DNS request, file access, and intercommunication between computers; and uses artificial intelligence to detect inappropriate actions by programs and scripts, stopping them before they can affect the kernel or memory.
XDR can also threat hunt for indicators related to attack precursors, which allows us to notify you of inappropriate communications coming through your firewalls or from unprotected endpoints that may be connected to your environment. It also static detects badness as malicious actors touch or execute files. In short, it’s hard to hide from XDR — and in using it to protect the core systems that contain your data, Arete protects your ability to do business.
Other advantages XDR has over SIEMs include:
The ability to detect all assets on networks where company computers with the agent reside.
USB control to prevent exfiltration.
Firewall control native to Windows systems.
Network interface card control to stop communications in an emergency.
Vulnerability data on all covered Windows, Linux and Mac systems.
XDR tools are not only capable of reporting on ransomware damage, but their autonomous behavior-based capabilities can detect and stop ransomware before it can cause any damage.
Back to Blog Posts
Report
Arete's 2025 Annual Crimeware Report
Harness Arete’s unique data and expertise on extortion and ransomware to inform your response to the evolving threat landscape.
Article
FortiGate Exploits Enable Network Breaches and Credential Theft
A recent security report indicates that threat actors are actively exploiting FortiGate Next-Generation Firewall (NGFW) appliances as initial access vectors to compromise enterprise networks. The activity leverages recently disclosed vulnerabilities or weak credentials to gain unauthorized access and extract configuration files, which often contain sensitive information, including service account credentials and detailed network topology data.
Analysis of these incidents shows significant variation in attacker dwell time, ranging from immediate lateral movement to delays of up to two months post-compromise. Since these appliances often integrate with authentication systems such as Active Directory and Lightweight Directory Access Protocol (LDAP), their compromise can grant attackers extensive access, substantially increasing the risk of widespread network intrusion and data exposure.
What’s Notable and Unique
The activity involves the exploitation of recently disclosed security vulnerabilities, including CVE-2025-59718, CVE-2025-59719, and CVE-2026-24858, or weak credentials, allowing attackers to gain administrative access, extract configuration files, and obtain service account credentials and network topology information.
In one observed incident, attackers created a FortiGate admin account with unrestricted firewall rules and maintained access over time, consistent with initial access broker activity. After a couple of months, threat actors extracted and decrypted LDAP credentials to compromise Active Directory.
In another case, attackers moved from FortiGate access to deploying remote access tools, including Pulseway and MeshAgent, while also utilizing cloud infrastructure such as Google Cloud Storage and Amazon Web Services (AWS).
Analyst Comments
Arete has identified multiple instances of Fortinet device exploitation for initial access, involving various threat actors, with the Qilin ransomware group notably leveraging Fortinet device exploits. Given their integration with systems like Active Directory, NGFW appliances remain high-value targets for both state-aligned and financially motivated actors. In parallel, Arete has observed recent dark web activity involving leaked FortiGate VPN access, further highlighting the expanding risk landscape. This aligns with the recent reporting from Amazon Threat Intelligence, which identified large-scale compromises of FortiGate devices driven by exposed management ports and weak authentication, rather than vulnerability exploitation. Overall, these developments underscore the increasing focus on network edge devices as entry points, reinforcing the need for organizations to strengthen authentication, restrict external exposure, and address fundamental security gaps to mitigate the risk of widespread compromise.
Sources
FortiGate Edge Intrusions | Stolen Service Accounts Lead to Rogue Workstations and Deep AD Compromise
Article
Vulnerability Discovered in Anthropic’s Claude Code
Security researchers discovered two critical vulnerabilities in Anthropic's agentic AI coding tool, Claude Code. The vulnerabilities, tracked as CVE-2025-59536 and CVE-2026-21852, allowed attackers to achieve remote code execution and to compromise a victim's API credentials. The vulnerabilities exploit maliciously crafted repository configurations to circumvent control mechanisms. It should be noted that Anthropic worked closely with the security researchers throughout the process, and the bugs were patched before the research was published.
What’s Notable and Unique
The configuration files .claude/settings.json and .mcp.json were repurposed to execute malicious commands. Because the configurations could be applied immediately upon starting Claude Code, the commands ran before the user could deny permissions via a dialogue prompt, or they bypassed the authentication prompt altogether.
.claude/settings.json also defines the endpoint for all Claude Code API communications. By replacing the default localhost URL with a URL they own, an attacker could redirect traffic to infrastructure they control. Critically, the authentication traffic generated upon starting Claude Code included the user's full Anthropic API key in plain text and was sent before the user could interact with the trust dialogue.
Restrictive permissions on sensitive files could be bypassed by simply prompting Claude Code to create a copy of the file's contents, which did not inherit the original file's permissions. A threat actor using a stolen API key could gain complete read and write access to all files within a workspace.
Analyst Comments
The vulnerabilities and attack paths detailed in the research illustrate the double-edged nature of AI tools. The speed, scale, and convenience characteristics that make AI tools attractive to developer teams also benefit threat actors who use them for nefarious purposes. Defenders should expect adversaries to continue seeking ways to exploit configurations and orchestration logic to increase the impact of their attacks. Organizations planning to implement AI development tools should prioritize AI supply-chain hygiene and CI/CD hardening practices.
Sources
Caught in the Hook: RCE and API Token Exfiltration Through Claude Code Project Files | CVE-2025-59536 | CVE-2026-21852
Article
Ransomware Trends & Data Insights: February 2026
After a slight lull in January, Akira and Qilin returned to dominating ransomware activity in February, collectively accounting for almost half of all engagements that month. The rest of the threat landscape remained relatively diverse, with a mix of persistent threats like INC and PLAY, older groups like Cl0p and LockBit, and newer groups like BravoX and Payouts King. Given current trends, the first quarter of 2026 will likely remain relatively predictable, with the top groups from the second half of 2025 continuing to operate at fairly consistent levels month to month.
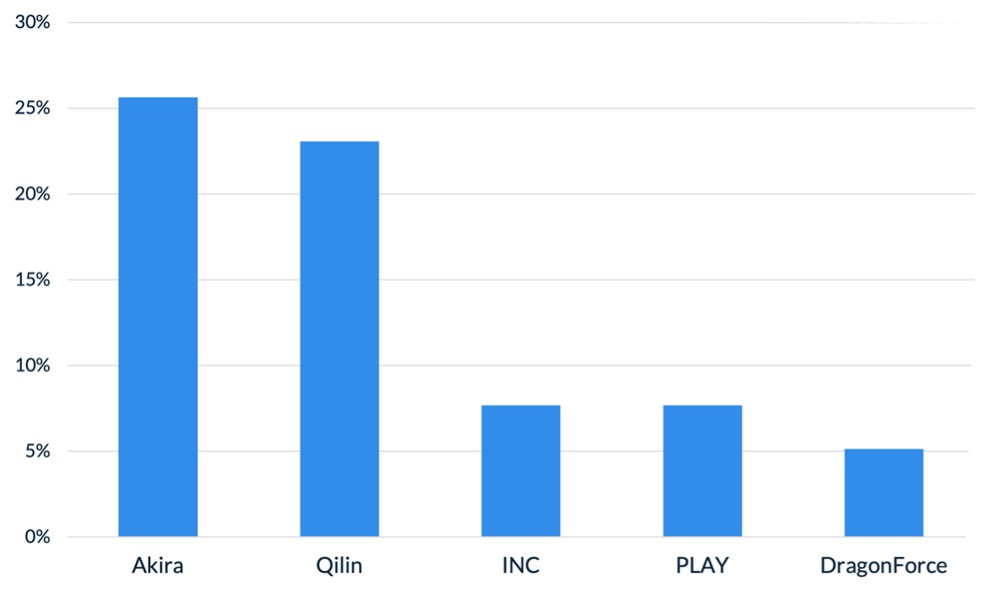
Figure 1. Activity from the top 5 threat groups in February 2026
Throughout the month of February, analysts at Arete identified several trends behind the threat actors perpetrating cybercrime activities:
In February, Arete observed Qilin actively targeting WatchGuard Firebox devices, especially those vulnerable to CVE-2025-14733, to gain initial access to victim environments. CVE-2025-14733 is a critical vulnerability in WatchGuard Fireware OS that allows a remote, unauthenticated threat actor to execute arbitrary code. In addition to upgrading WatchGuard devices to the latest Firebox OS version, which patches the bug, administrators are urged to rotate all shared secrets on affected devices that may have been compromised and may be used in future campaigns.
Reports from February suggest that threat actors are increasingly exploring AI-enabled tools and services to scale malicious activities, demonstrating how generative AI is being integrated into both espionage and financially motivated threat operations. The Google Threat Intelligence Group indicated that state-backed threat actors are leveraging Google’s Gemini AI as a force multiplier to support all stages of the cyberattack lifecycle, from reconnaissance to post-compromise operations. Separate reporting from Amazon Threat Intelligence identified a threat actor leveraging commercially available generative AI services to conduct a large-scale campaign against FortiGate firewalls, gaining access through weak or reused credentials protected only by single-factor authentication.
The Interlock ransomware group recently introduced a custom process-termination utility called “Hotta Killer,” designed to disable endpoint detection and response solutions during active intrusions. This tool exploits a zero-day vulnerability (CVE-2025-61155) in a gaming anti-cheat driver, marking a significant adaptation in the group’s operations against security tools like FortiEDR. Arete is actively monitoring this activity, which highlights the growing trend of Bring Your Own Vulnerable Driver (BYOVD) attacks, in which threat actors exploit legitimate, signed drivers to bypass and disable endpoint security controls.
Sources
Arete Internal



