Report
Observations on Midnight Group’s Fraud Campaign Resurgence
Arete Analysis
Cybersecurity Trends

Download The Report
Click the 'Access The Report' button above to read the full report.
Arete’s research recently discovered a fraud campaign by a re-emerging actor dubbed “Midnight Group” specifically targeting organizations who previously fell victim to ransomware attacks. Midnight Group operations date back as far as 2019, but recently their operational tempo has increased dramatically. Interestingly, the re-victimized organizations experienced the initial attacks at the hands of over five distinct threat actor groups. Victims of this fraud campaign receive emails claiming the Midnight Group was behind the original ransomware attack, and their data will be posted on the dark web if they do not pay. At the time of this reporting, at least 15 current or previous Arete clients received this fraudulent email.
• The Midnight Group threat actor is identifying victims of ransomware attacks, even when the victims are not publicly available.
• The Midnight Group claims to have exfiltrated between 700GB–900GB of data, even in cases where no data exfiltration occurred, or a different amount of data was exfiltrated.
• Contacted individuals appear to have been identified on the victim’s public website.
• In several instances, the threat actor claimed to be associated with different ransomware
operations (e.g. Surtr and Silent Ransom), but these threat actor groups were not involved in the original ransomware attack suffered by the victims.
Back to Blog Posts
Article
Critical MOVEit Automation Vulnerabilities Disclosed
A security advisory released by Progress Software details critical and high-severity vulnerabilities affecting their MOVEit Automation managed file transfer (MFT) solution. The vulnerabilities, tracked as CVE-2026-4670 and CVE-2026-5174, could allow a threat actor to bypass authentication and escalate privileges, leading to unauthorized access, administrative control, and data exposure. Cybercriminals have leveraged several MFT tools in previous campaigns, including the Accellion File Transfer Application (FTA), Fortra GoAnywhere MFT, and Cleo MFT. Flaws in MFT software are highly targeted by cybercriminals due to the volume and sensitivity of the data they control.
What’s Notable and Unique
MOVEit Transfer was heavily exploited by the Cl0p ransomware group in the summer of 2023. While the window of exploit activity lasted only a few weeks, victim extortion and data leaks continued throughout the remainder of the year, leading to more than 70 class-action lawsuits filed in the U.S.
There is no workaround or hotfix for these vulnerabilities. To fully patch the flaws, MOVEit administrators need to perform a "full install" of the latest version, which will require taking the system offline.
Security researchers have discovered ~1,400 MOVEit Automation instances exposed to the internet, with dozens belonging to U.S. local and state government agencies.
Analyst Comments
While the vulnerabilities patched in Progress Software's recent release differ from the SQL injection vulnerability exploited by the Cl0p ransomware group in 2023, exploitation of CVE-2026-4670 and CVE-2026-5174 could lead to equally impactful outcomes. Beyond the immediate impacts on affected organizations, trusted data-exchange platforms provide threat actors with an avenue to obtain sensitive information and infect partner and supplier environments. Furthermore, Arete has seen the time window between disclosure and weaponization of critical vulnerabilities continue to shrink, especially as threat actors increasingly adopt AI-enabled tooling. As such, organizations should not only implement the patches released by Progress Software, but also hunt for typical post-compromise behavior like enumeration of the underlying database, the creation of new user accounts or users operating with unexpected administrator privileges, and the presence of unauthorized remote monitoring and management (RMM) tools.
Sources
MOVEit Automation Critical Security Alert Bulletin – April 2026 – (CVE-2026-4670, CVE-2026-5174)
From Breach to Courtroom: Inside the MOVEit Exploitation and Mass Litigation
Progress warns of critical MOVEit Automation auth bypass flaw
Article
Ransomware Trends & Data Insights: April 2026
The threat landscape has remained relatively predictable thus far in 2026. In April, Qilin dethroned Akira as the most active threat group for the month. Akira, who had been the top ransomware threat each month since July 2025, was still only slightly behind Qilin and had roughly the same activity level as in March. INC Ransom and DragonForce also remained active threats in April, with those four ransomware groups accounting for half of all ransomware and extortion activity observed by Arete.
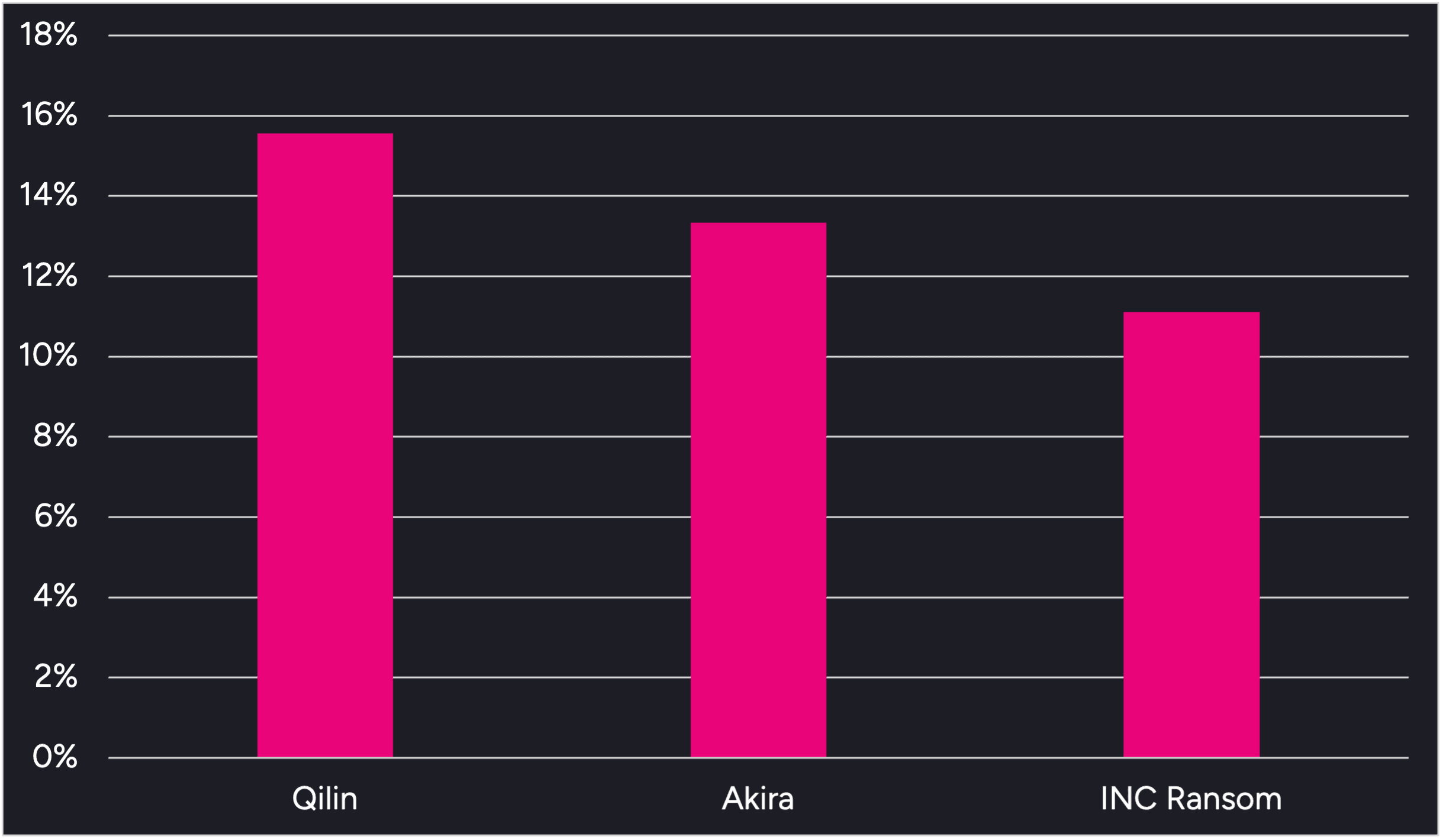
Figure 1. Activity from the top 3 threat groups in April 2026
Throughout the month, analysts at Arete identified several trends behind the threat actors perpetrating cybercrime activities:
Multiple ransomware operations continue to leverage the Bring Your Own Vulnerable Driver (BYOVD) technique to disable endpoint security controls prior to ransomware deployment. Qilin has recently been observed leveraging a malicious file loaded via DLL side-loading along with vulnerable drivers, including rwdrv.sys and hlpdrv.sys, to gain kernel-level access and disable security processes. Arete observed Akira using the same vulnerable drivers in multiple engagements dating back to Q3 2025.
DragonForce has leveraged several of the same tools in recent engagements, including the remote desktop application Remotely Agent and the PoisonX.sys vulnerable driver. Additionally, open-source reporting indicates that the group recently used a Python-based backdoor known as VIPERTUNNEL to maintain reliable operator access and evade detection. DragonForce was responsible for over 7% of Arete ransomware engagements in April, and Arete notes increased activity from the group this year compared to 2025.
A social engineering tactic has reemerged in recent months in which threat actors impersonate IT and helpdesk staff via Microsoft Teams to contact employees and attempt to convince them to install remote access tools like Quick Assist, giving the threat actors remote access to the victim’s environment. This tactic was initially observed in late 2024 and early 2025 and was linked to now-defunct groups like Black Basta and Cactus, but has more recently been observed in intrusions linked to the Akira and Payouts King ransomware groups.
Sources
Arete Internal
Article
Payouts King Utilizes QEMU Emulator to Bypass EDR
Researchers recently identified threat actor campaigns leveraging QEMU, a free open-source virtual machine (VM) emulator, to evade endpoint security solutions. Since QEMU acts as a VM within the target environment, endpoint detection tools cannot scan inside the emulator or detect any malicious files or payloads QEMU contains. Although threat actors have been utilizing QEMU maliciously since 2020, recent activity is attributed to the Payouts King ransomware group and a cluster of threat actors believed to be initial access brokers who have also been exploiting the CitrixBleed2 vulnerability CVE-2025-5777.
What’s Notable and Unique
Payouts King has been observed deploying QEMU since November and uses the VM to create a reverse SSH backdoor to evade detection and install various tools, including Rclone, Chisel, and BusyBox.
In a separate campaign, threat actors are exploiting CVE-2025-5777, a Citrix NetScaler vulnerability that allows attackers to bypass authentication. Once they’ve gained initial access, the threat actors use QEMU to deploy tools inside the VM, which are then used to steal credentials, identify Kerberos usernames, perform Active Directory reconnaissance, and set up FTP servers for staging or data exfiltration.
Analyst Comments
Threat actors continue to focus their efforts on defense evasion, often leveraging legitimate, easily accessible tools such as QEMU. The continued use of QEMU by multiple threat actors highlights the effectiveness of these tactics and the difficulty in detecting and defending against them. To counter this campaign, organizations should proactively monitor for unauthorized QEMU installations, abnormal scheduled tasks, and port forwarding rules.
Sources
QEMU abused to evade detection and enable ransomware delivery
Article
Microsoft Teams Continues to be Leveraged in Social Engineering Attacks
Microsoft warns that threat actors are increasingly abusing Microsoft Teams and relying on legitimate tools to gain access and conduct lateral movement within enterprise networks. The threat actors impersonate IT or helpdesk staff to contact employees via cross-tenant chats and trick them into granting remote access for data theft. Microsoft has observed multiple intrusions with a similar attack chain that utilized commercial remote management software, like Quick Assist and the Rclone utility, to transfer files to an external cloud storage service. This tactic, notably associated with Black Basta and Cactus ransomware operations in late 2024 and early 2025, appears to have resurfaced, with similar activity more recently observed in intrusions linked to the Akira and Payouts King ransomware groups.
What’s Notable and Unique
Initial access is achieved by leveraging external collaboration features in Microsoft Teams to allow impersonation of internal support personnel, tricking users into bypassing security warnings. This reflects abuse of legitimate functionality rather than exploitation of a Microsoft Teams vulnerability.
Following initial access, attackers conduct rapid reconnaissance using Command Prompt and PowerShell to assess privileges, domain membership, and opportunities for lateral movement. Persistence is maintained through Windows Registry modifications, after which attackers leveraged WinRM for lateral movement, targeting domain-joined systems and high-value assets, including domain controllers.
Malicious payloads were staged in user-writable directories and executed through DLL side-loading via trusted, signed applications, enabling covert code execution while blending with legitimate activity. Additional remote management tools were also deployed to support broader access, while Rclone or similar utilities were used to stage and exfiltrate sensitive data to external cloud storage.
Analyst Comments
This activity highlights how modern threat actors can leverage trusted collaboration workflows, remote management tools, and stealthy exfiltration techniques to conduct intrusions through a combination of social engineering and misuse of legitimate functionality. Effective defense depends on layered mitigations that combine identity controls, restricted remote administration, endpoint hardening, network protections, and user awareness measures to disrupt attacker activity at multiple stages of the intrusion lifecycle. To mitigate the risk of this and similar campaigns, users should treat external Teams contacts as untrusted by default, and administrators should restrict or closely monitor remote assistance tools while limiting WinRM usage to controlled systems.
Sources
Cross‑tenant helpdesk impersonation to data exfiltration: A human-operated intrusion playbook
Microsoft: Teams increasingly abused in helpdesk impersonation attacks
Payouts King Takes Aim at the Ransomware Throne



